Post-Quantum Cryptography
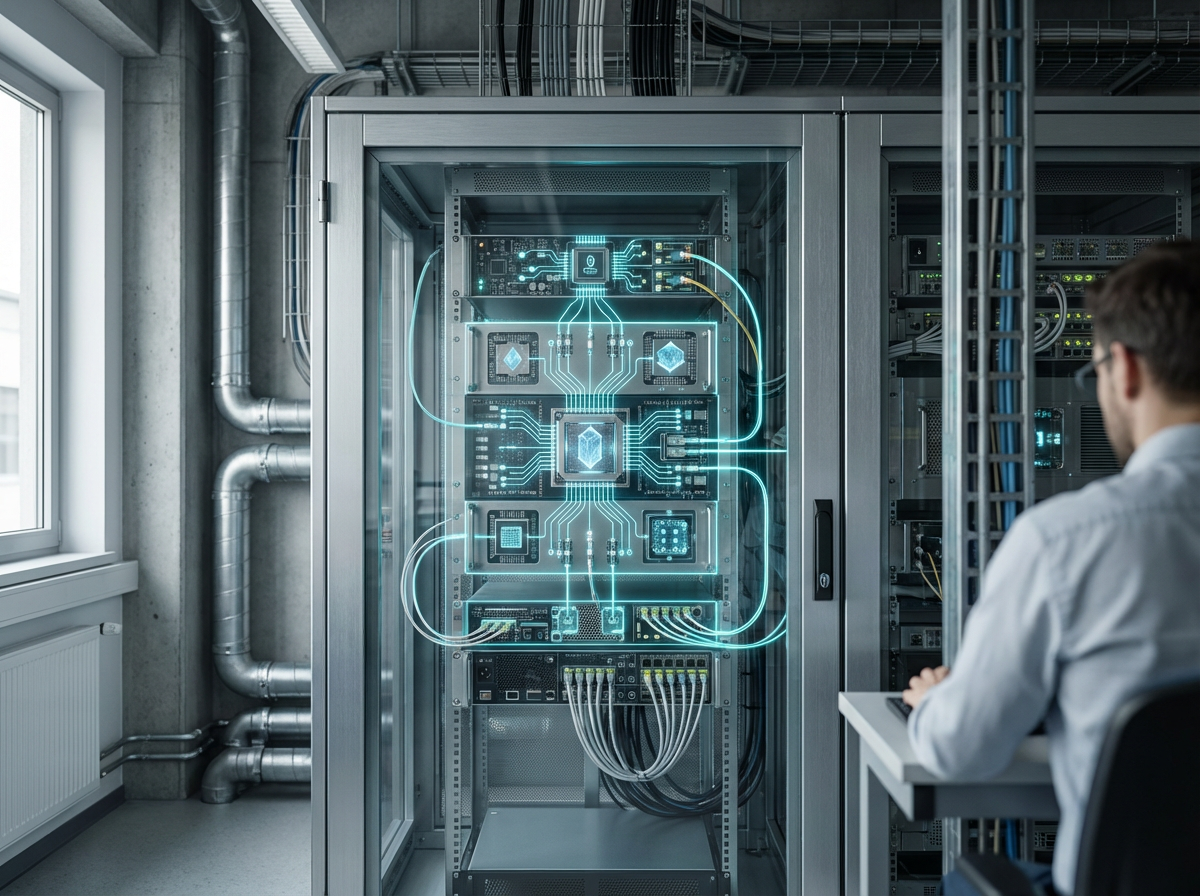
Post-quantum cryptography represents a fundamental shift in how we approach data security in anticipation of quantum computing's arrival. Traditional cryptographic systems, including RSA and elliptic curve cryptography, rely on mathematical problems that are computationally difficult for classical computers to solve—such as factoring large prime numbers or computing discrete logarithms. However, quantum computers leverage principles of quantum mechanics to perform certain calculations exponentially faster than classical machines. Algorithms like Shor's algorithm could theoretically break these widely-used encryption methods, rendering current security infrastructure vulnerable. Post-quantum cryptography addresses this looming threat by developing new cryptographic algorithms based on mathematical problems that remain difficult even for quantum computers to solve. These include lattice-based cryptography, hash-based signatures, code-based cryptography, and multivariate polynomial equations. The National Institute of Standards and Technology (NIST) has been leading a multi-year standardization process to evaluate and select the most promising post-quantum algorithms for widespread adoption.
The implications for national security, critical infrastructure, and global commerce are profound. Governments and organizations face a "harvest now, decrypt later" threat, where adversaries collect encrypted data today with the intention of decrypting it once quantum computers become sufficiently powerful. This makes the transition to post-quantum cryptography urgent, particularly for sensitive information that must remain confidential for decades, such as medical records, financial transactions, diplomatic communications, and classified intelligence. The challenge extends beyond simply replacing algorithms—it requires updating entire security protocols, key management systems, and hardware implementations across vast networks. Industries ranging from telecommunications to banking must coordinate this transition while maintaining backward compatibility with existing systems. The computational overhead of some post-quantum algorithms also presents practical challenges, as they often require larger key sizes and more processing power than current methods.
Research institutions and technology companies are actively developing and testing post-quantum implementations across various sectors. Financial institutions are piloting quantum-resistant protocols for secure transactions, while telecommunications providers are exploring integration into 5G and future network architectures. Government agencies are beginning to mandate post-quantum readiness timelines for contractors and critical infrastructure operators. The transition is expected to unfold gradually over the next decade, with hybrid approaches combining classical and post-quantum methods serving as an intermediate step. As quantum computing capabilities advance, the race to deploy quantum-resistant cryptography becomes increasingly critical for maintaining the security foundations of digital society, protecting everything from personal privacy to national sovereignty in an era where computational power could fundamentally alter the balance of information security.
Related Organizations
US federal agency that sets standards for technology, including facial recognition vendor tests (FRVT).
Long-standing leader in neuro-symbolic AI, combining neural networks with logical reasoning for enterprise applications.
A spinout from Oxford University providing hardware and software IP for PQC, including side-channel analysis tools to test resistance.
Spun out of Alphabet, they provide a Security Suite that discovers cryptographic vulnerabilities and manages the migration to PQC.
Develops crypto-agile solutions and tools to test and migrate systems to quantum-safe standards.
Provides 'QuProtect', a software platform that monitors network traffic to detect and upgrade vulnerable cryptographic connections.
A major semiconductor manufacturer developing secure chips with hardware support for PQC algorithms.
Integrated quantum computing company formed by Honeywell and CQC.
Prime contractor for the TeQuantS project and a key partner in ESA's quantum satellite initiatives.
Co-founded by Michele Mosca, offering 'Quantum Risk Assessment' services and tools to evaluate organizational vulnerability to quantum decryption.