Post-Quantum Cryptography
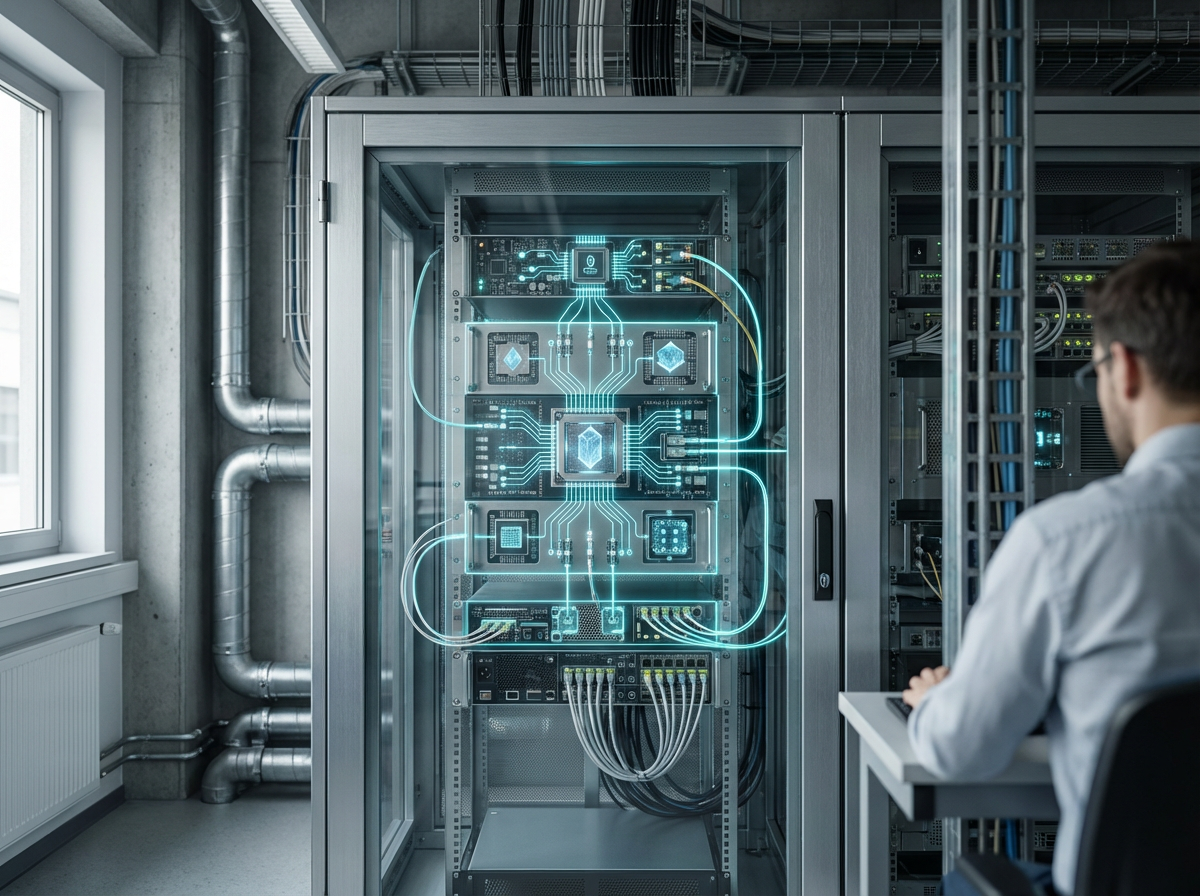
Post-quantum cryptography represents a fundamental shift in how industrial systems protect sensitive data and communications against an emerging threat: quantum computers capable of breaking current encryption standards. Traditional cryptographic methods, such as RSA and elliptic curve cryptography, rely on mathematical problems that are computationally difficult for classical computers to solve. However, quantum computers leverage principles of quantum mechanics to perform certain calculations exponentially faster, potentially rendering these widely-used encryption methods obsolete. Post-quantum cryptography addresses this vulnerability by developing new algorithms based on mathematical problems that remain difficult even for quantum computers to crack. These include lattice-based cryptography, hash-based signatures, code-based cryptography, and multivariate polynomial equations. Standards like ML-KEM (Module-Lattice-Based Key-Encapsulation Mechanism) exemplify this new generation of cryptographic protocols, designed specifically to withstand both classical and quantum computational attacks while maintaining practical performance for real-world deployment.
The industrial sector faces a unique challenge known as "harvest now, decrypt later," where adversaries could intercept and store encrypted data today with the intention of decrypting it once sufficiently powerful quantum computers become available. This threat is particularly acute for operational technology environments, where critical infrastructure components such as power grids, manufacturing systems, and industrial control networks often operate for decades. Equipment installed today may still be processing sensitive information twenty or thirty years from now, well into an era when quantum computing capabilities could be widespread. Post-quantum cryptography solves this problem by enabling organizations to implement quantum-resistant security measures immediately, protecting long-lifecycle assets throughout their operational lifespan. This proactive approach prevents the costly and disruptive need to retrofit security systems across vast industrial networks once quantum threats materialize. Furthermore, regulatory bodies and industry standards organizations are increasingly recognizing the importance of quantum-resistant security, with guidelines emerging that recommend or mandate post-quantum cryptographic implementations for critical infrastructure.
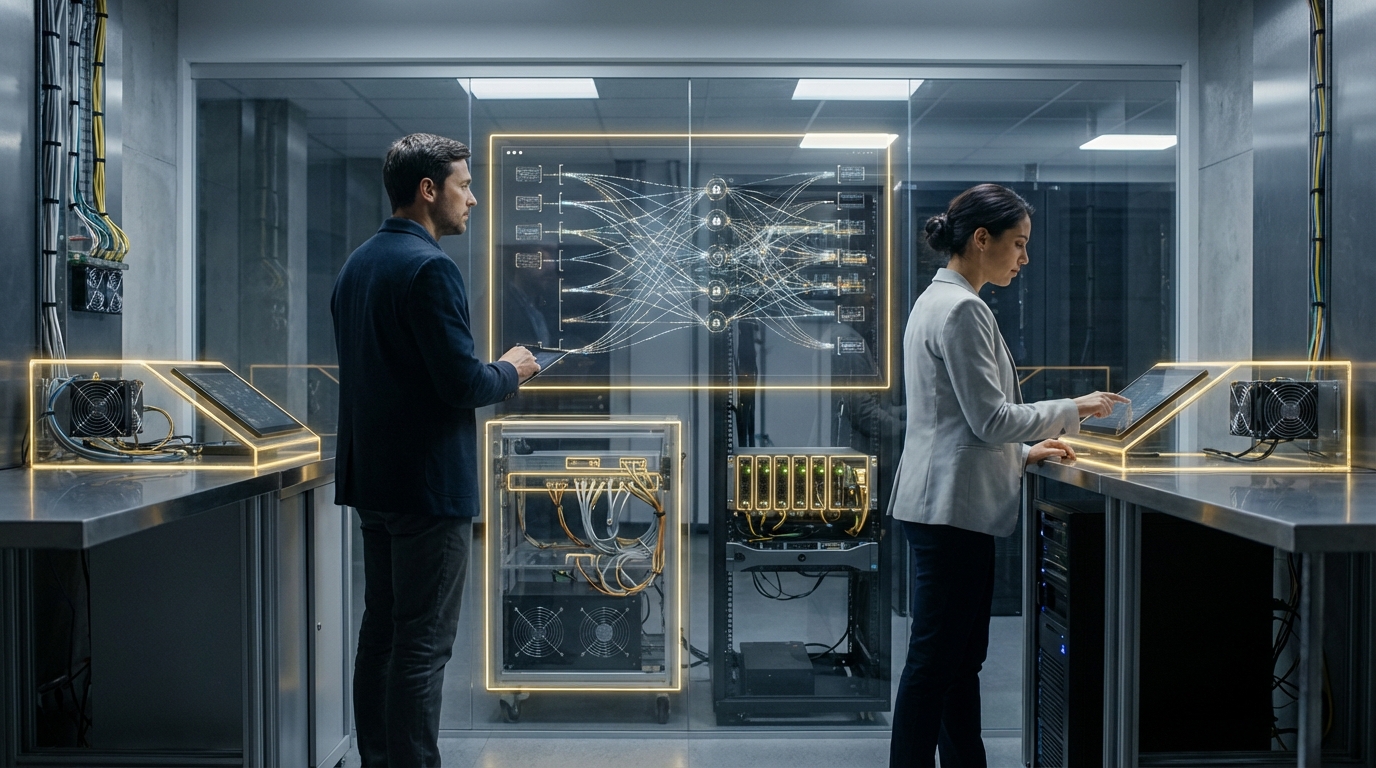
Early adoption of post-quantum cryptography is already underway across various industrial sectors, with pilot programs testing the integration of quantum-resistant algorithms into programmable logic controllers, supervisory control and data acquisition systems, and other operational technology platforms. Research indicates that hybrid approaches—combining traditional and post-quantum algorithms—are gaining traction as organizations transition toward full quantum resistance while maintaining backward compatibility. The manufacturing sector, energy utilities, and transportation infrastructure operators are among the early adopters, recognizing that the window for implementing these protections is narrowing as quantum computing advances accelerate. Industry analysts note that the convergence of cyber-physical systems and the Industrial Internet of Things amplifies the urgency, as interconnected devices create expanded attack surfaces that must be secured against both present and future threats. As quantum computing continues its rapid development trajectory, post-quantum cryptography will transition from a forward-looking precaution to an essential component of industrial cybersecurity frameworks, ensuring that the Fourth Industrial Revolution's digital infrastructure remains resilient against the computational capabilities of tomorrow.
Related Organizations
Long-standing leader in neuro-symbolic AI, combining neural networks with logical reasoning for enterprise applications.
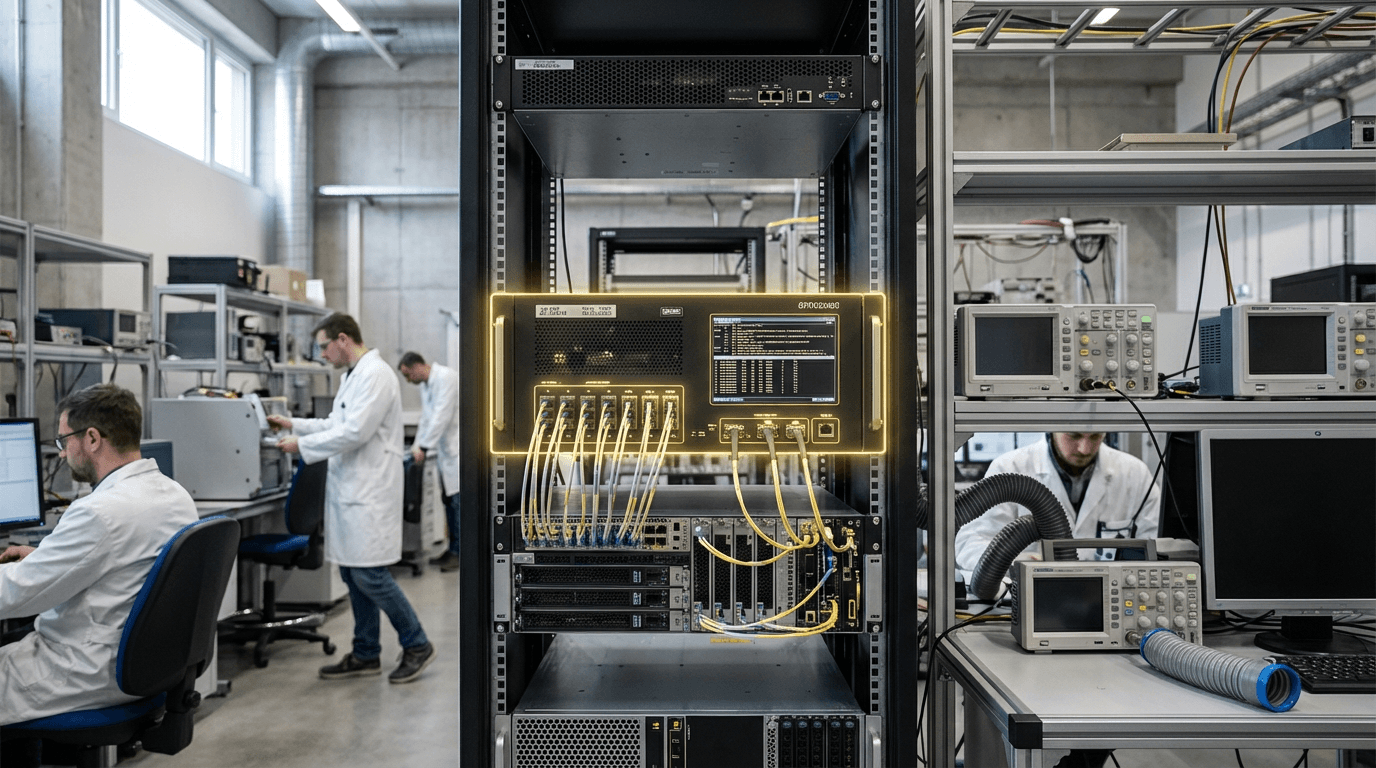
A spinout from Oxford University providing hardware and software IP for PQC, including side-channel analysis tools to test resistance.
Spun out of Alphabet, they provide a Security Suite that discovers cryptographic vulnerabilities and manages the migration to PQC.
Provides 'QuProtect', a software platform that monitors network traffic to detect and upgrade vulnerable cryptographic connections.
Develops crypto-agile solutions and tools to test and migrate systems to quantum-safe standards.
Co-founded by Michele Mosca, offering 'Quantum Risk Assessment' services and tools to evaluate organizational vulnerability to quantum decryption.
Integrated quantum computing company formed by Honeywell and CQC.
A web infrastructure and security company that has already enabled PQC support for a significant portion of the internet.
A major semiconductor manufacturer developing secure chips with hardware support for PQC algorithms.
Prime contractor for the TeQuantS project and a key partner in ESA's quantum satellite initiatives.