Post-Quantum Cryptography
Post-quantum cryptography represents a fundamental shift in how financial institutions protect sensitive data against an emerging threat: quantum computers capable of breaking current encryption standards. Traditional cryptographic systems, including RSA and elliptic curve cryptography that underpin modern banking, payment processing, and blockchain networks, rely on mathematical problems that are computationally infractible for classical computers to solve. However, quantum computers leveraging algorithms like Shor's algorithm could theoretically crack these encryption methods in minutes rather than millennia. Post-quantum cryptography addresses this vulnerability by developing new cryptographic algorithms based on mathematical problems that remain difficult even for quantum computers, such as lattice-based cryptography, hash-based signatures, and code-based encryption. The National Institute of Standards and Technology (NIST) has led a multi-year standardization process, selecting algorithms like CRYSTALS-Kyber for key encapsulation and CRYSTALS-Dilithium for digital signatures as the foundation for quantum-resistant security protocols.
The financial services industry faces particularly acute risks from quantum computing advances, as the sector depends entirely on cryptographic security for transaction authentication, customer data protection, and regulatory compliance. A sufficiently powerful quantum computer could retroactively decrypt archived financial communications, compromise digital signatures on contracts and transactions, or undermine the cryptographic foundations of blockchain-based assets and central bank digital currencies. Post-quantum cryptography provides financial institutions with migration pathways to quantum-resistant security before quantum computers reach operational capability. This transition addresses not only future threats but also "harvest now, decrypt later" attacks, where adversaries collect encrypted data today with the intention of decrypting it once quantum computers become available. The technology enables banks, insurance companies, and payment processors to maintain the confidentiality and integrity guarantees that customers and regulators expect, even in a post-quantum world.
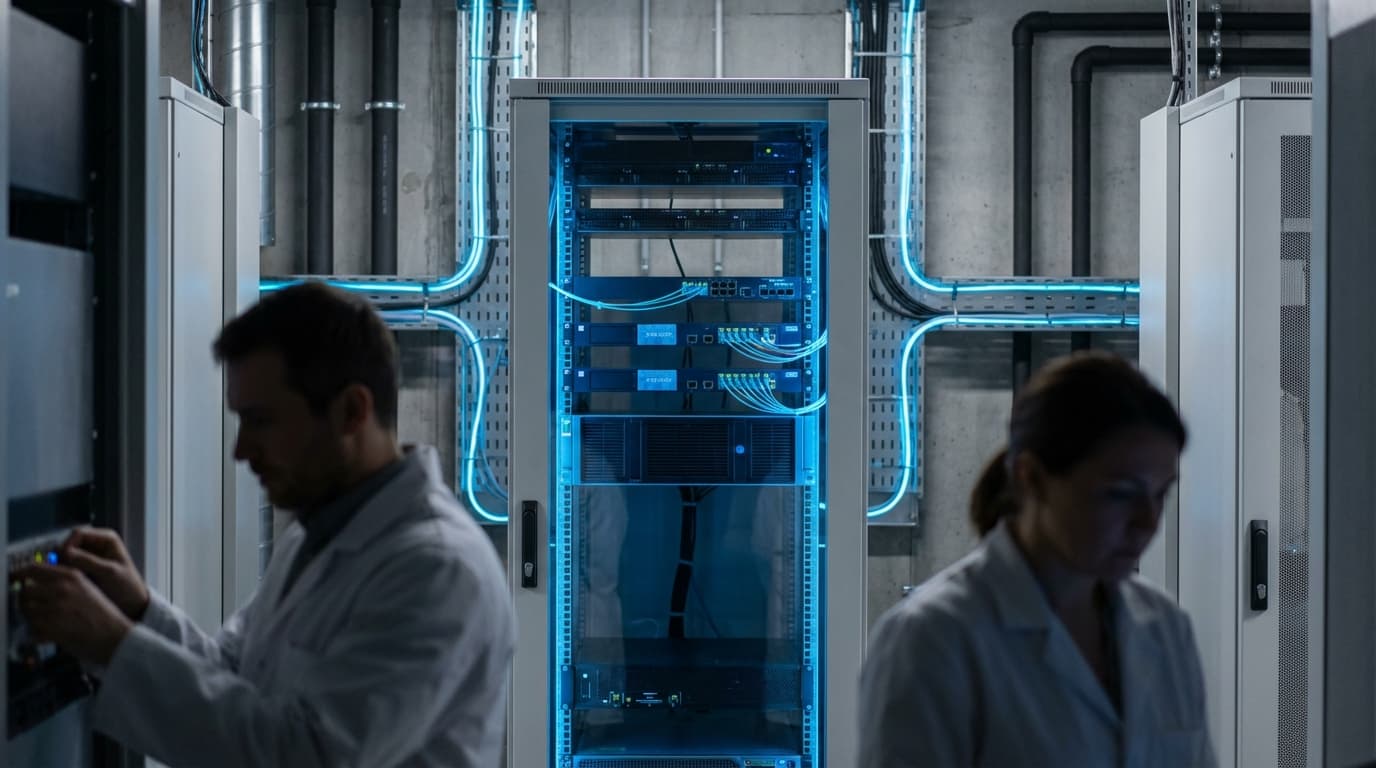
Major financial institutions and technology providers have begun implementing hybrid cryptographic approaches that combine classical and post-quantum algorithms, providing security against both current and future threats while allowing gradual system migration. Payment networks are exploring quantum-resistant protocols for card transactions and digital wallets, while blockchain platforms are developing quantum-safe consensus mechanisms and wallet architectures. Regulatory bodies are increasingly recognizing quantum computing as a material cybersecurity risk, with some jurisdictions beginning to establish timelines for post-quantum cryptography adoption in critical financial infrastructure. The technology connects to broader industry trends around cryptographic agility—the ability to rapidly update security protocols as threats evolve—and zero-trust architecture principles that assume potential compromise at every layer. As quantum computing capabilities advance and become more accessible, post-quantum cryptography will transition from a forward-looking precaution to an essential component of financial security infrastructure, ensuring that the digital foundations of modern finance remain secure in an era of unprecedented computational power.
Related Organizations
US federal agency that sets standards for technology, including facial recognition vendor tests (FRVT).
International financial institution owned by central banks that fosters international monetary and financial cooperation.
A spinout from Oxford University providing hardware and software IP for PQC, including side-channel analysis tools to test resistance.
Spun out of Alphabet, they provide a Security Suite that discovers cryptographic vulnerabilities and manages the migration to PQC.
Develops crypto-agile solutions and tools to test and migrate systems to quantum-safe standards.
Provides 'QuProtect', a software platform that monitors network traffic to detect and upgrade vulnerable cryptographic connections.
Co-founded by Michele Mosca, offering 'Quantum Risk Assessment' services and tools to evaluate organizational vulnerability to quantum decryption.
A global leader in quantum cybersecurity solutions, specifically known for their Quantis QRNG chips and appliances.
Integrated quantum computing company formed by Honeywell and CQC.
Prime contractor for the TeQuantS project and a key partner in ESA's quantum satellite initiatives.




















