Post-Quantum Cryptography
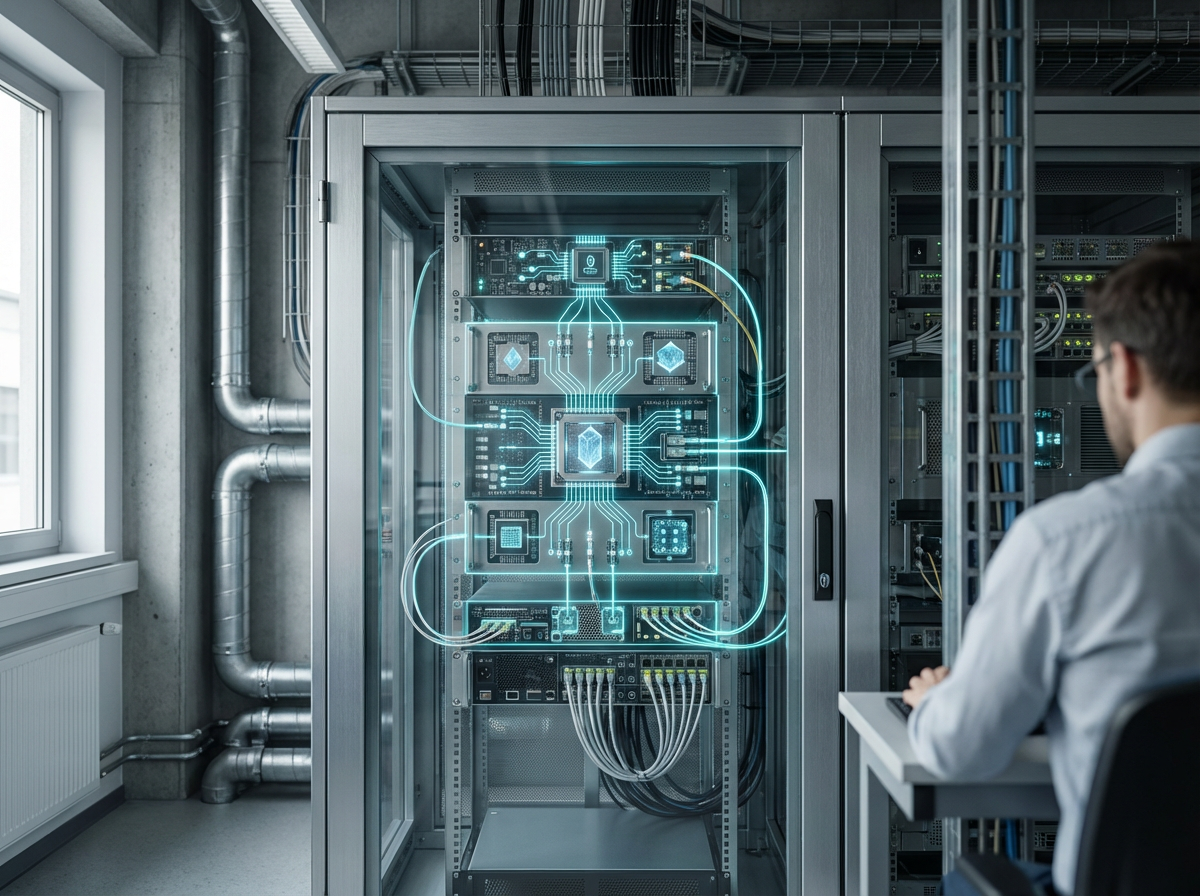
Post-quantum cryptography represents a fundamental shift in how we protect digital information, addressing the looming threat that quantum computers pose to current encryption standards. Traditional cryptographic systems, such as RSA and elliptic curve cryptography, rely on mathematical problems that are computationally difficult for classical computers to solve—specifically, factoring large numbers or solving discrete logarithm problems. However, quantum computers leveraging algorithms like Shor's algorithm could theoretically break these encryption methods in a fraction of the time required by conventional machines. Post-quantum cryptography encompasses several families of algorithms designed to resist such attacks, including lattice-based cryptography, which relies on the hardness of finding short vectors in high-dimensional lattices; hash-based signatures that build security on the collision resistance of cryptographic hash functions; code-based systems derived from error-correcting codes; and multivariate polynomial cryptography that uses systems of multivariate quadratic equations. These approaches are grounded in mathematical problems believed to remain intractable even for quantum computers, providing a foundation for secure communications in a post-quantum world.
The urgency of transitioning to post-quantum cryptography stems from what security experts call the "harvest now, decrypt later" threat, where adversaries collect encrypted data today with the intention of decrypting it once sufficiently powerful quantum computers become available. This poses existential risks to institutions managing sensitive information with long confidentiality requirements—government records, healthcare data, financial transactions, and classified communications could all be retroactively compromised. For critical infrastructure, the stakes are even higher: power grids, water treatment facilities, transportation networks, and telecommunications systems increasingly rely on encrypted control signals and authentication protocols. A successful quantum attack on these systems could enable unauthorized access, manipulation of industrial processes, or complete operational disruption. Similarly, blockchain-based governance systems and digital identity frameworks depend on cryptographic integrity; their compromise could undermine trust in decentralized institutions, digital currencies, and emerging models of civic participation. Post-quantum cryptography addresses these vulnerabilities by providing encryption methods that maintain security guarantees regardless of quantum computational advances, enabling organizations to protect both current operations and archived data against future threats.
Major standardization efforts are already underway, with the National Institute of Standards and Technology having selected several post-quantum algorithms for standardization after years of evaluation, signaling the technology's transition from research to practical deployment. Financial institutions are beginning pilot implementations to protect long-term investment records and transaction histories, while government agencies are developing migration roadmaps for classified communications systems. The technology is particularly critical for infrastructure with long operational lifespans—embedded systems in satellites, industrial control networks, and secure communication hardware that cannot be easily updated may remain vulnerable for decades without proactive cryptographic upgrades. Early adopters are implementing hybrid approaches that combine classical and post-quantum algorithms, providing defense-in-depth while the new standards mature. As quantum computing capabilities advance and the timeline for cryptographically relevant quantum computers becomes clearer, post-quantum cryptography will evolve from a precautionary measure to an essential component of civilizational resilience, ensuring that the digital foundations of modern society remain secure across generational timescales and technological paradigm shifts.
Related Organizations
US federal agency that sets standards for technology, including facial recognition vendor tests (FRVT).
Spun out of Alphabet, they provide a Security Suite that discovers cryptographic vulnerabilities and manages the migration to PQC.
Long-standing leader in neuro-symbolic AI, combining neural networks with logical reasoning for enterprise applications.
A spinout from Oxford University providing hardware and software IP for PQC, including side-channel analysis tools to test resistance.
Provides 'QuProtect', a software platform that monitors network traffic to detect and upgrade vulnerable cryptographic connections.
A web infrastructure and security company that has already enabled PQC support for a significant portion of the internet.
Develops crypto-agile solutions and tools to test and migrate systems to quantum-safe standards.
Co-founded by Michele Mosca, offering 'Quantum Risk Assessment' services and tools to evaluate organizational vulnerability to quantum decryption.
A major semiconductor manufacturer developing secure chips with hardware support for PQC algorithms.
A major European satellite manufacturer leading the ASCEND feasibility study.