Post-Quantum Government Cryptography
The advent of quantum computing poses an unprecedented threat to the cryptographic foundations that secure government communications, classified archives, and national identity systems. Traditional encryption methods, such as RSA and elliptic curve cryptography, rely on mathematical problems that are computationally infeasible for classical computers to solve. However, quantum computers leverage principles of quantum mechanics to perform certain calculations exponentially faster, rendering these once-secure algorithms vulnerable. This creates a critical vulnerability known as "harvest now, decrypt later," where adversaries can collect encrypted government data today and store it until quantum computers become powerful enough to break the encryption, potentially exposing state secrets that must remain confidential for decades. Post-quantum government cryptography addresses this existential threat by implementing encryption algorithms based on mathematical problems that remain difficult even for quantum computers to solve, such as lattice-based cryptography, hash-based signatures, and code-based systems.
Government institutions face unique challenges that make this transition particularly urgent. Unlike commercial entities that can rotate encryption keys frequently, state agencies manage information with secrecy requirements spanning 25, 50, or even 75 years—timelines that extend well beyond the anticipated arrival of cryptographically-relevant quantum computers. Intelligence agencies, diplomatic communications, nuclear command and control systems, and national identity databases all contain information whose compromise could threaten national security for generations. The migration to quantum-resistant algorithms solves the fundamental problem of ensuring that today's encrypted government data remains secure throughout its entire classification period, regardless of future advances in quantum computing. This transition also addresses the challenge of maintaining trust in digital government services, as citizens and international partners must have confidence that their interactions with state systems will remain confidential despite evolving technological threats.
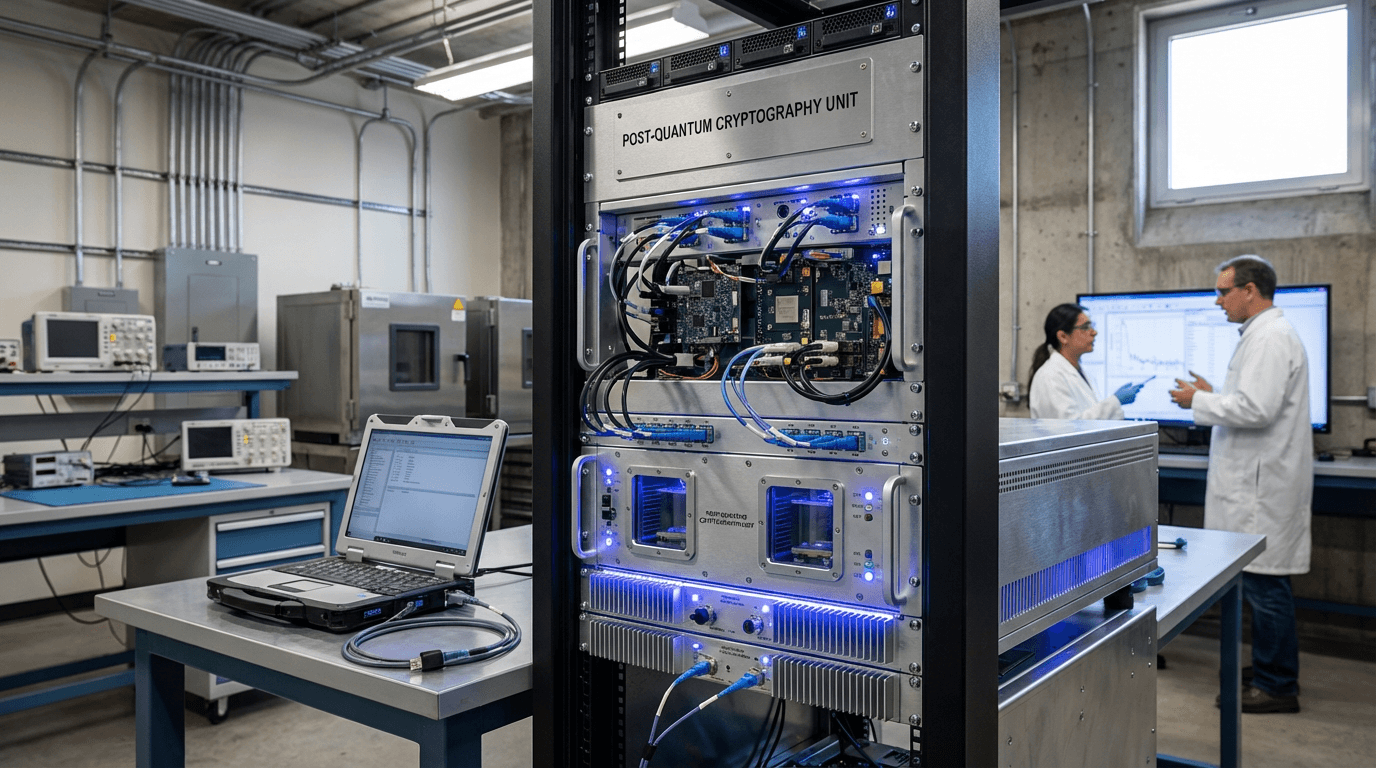
Following the National Institute of Standards and Technology's (NIST) standardisation of post-quantum cryptographic algorithms in 2024, government agencies worldwide have begun systematic migration efforts. Early implementations focus on the most sensitive systems first, including classified communications networks and long-term archival storage. The transition involves not only deploying new algorithms but also establishing hybrid approaches that combine classical and post-quantum methods during the migration period, ensuring backward compatibility while building quantum resistance. This technology represents a critical component of broader governmental digital transformation initiatives, as agencies must balance the urgency of protecting against future quantum threats with the practical challenges of updating legacy systems, training personnel, and maintaining operational continuity. As quantum computing capabilities continue to advance, post-quantum cryptography will become the standard foundation for all government digital infrastructure, ensuring that the state's most sensitive information remains secure in an era of unprecedented computational power.
Related Organizations
US federal agency that sets standards for technology, including facial recognition vendor tests (FRVT).
US federal agency responsible for guiding the government's migration to post-quantum cryptography.
Spun out of Alphabet, they provide a Security Suite that discovers cryptographic vulnerabilities and manages the migration to PQC.
A spinout from Oxford University providing hardware and software IP for PQC, including side-channel analysis tools to test resistance.
Provides 'QuProtect', a software platform that monitors network traffic to detect and upgrade vulnerable cryptographic connections.
Develops crypto-agile solutions and tools to test and migrate systems to quantum-safe standards.
Integrated quantum computing company formed by Honeywell and CQC.
Multinational company designing and building electrical systems and providing services for the aerospace, defence, transportation and security markets.
Co-founded by Michele Mosca, offering 'Quantum Risk Assessment' services and tools to evaluate organizational vulnerability to quantum decryption.
A major semiconductor manufacturer developing secure chips with hardware support for PQC algorithms.













