Post-Quantum Cryptography
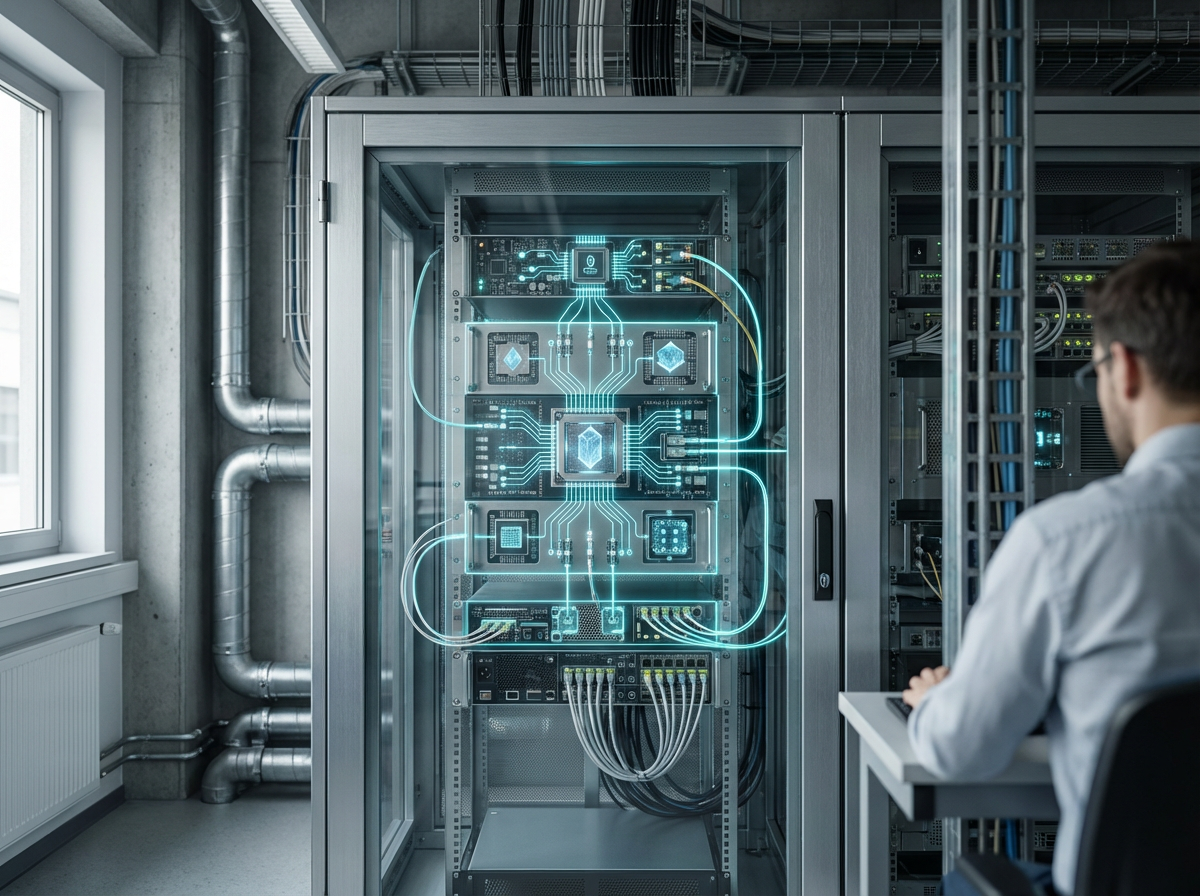
Post-quantum cryptography (PQC) refers to cryptographic algorithms designed to be secure against attacks from both classical and quantum computers. Current cryptographic systems like RSA and elliptic curve cryptography rely on mathematical problems that quantum computers could solve efficiently using algorithms like Shor's algorithm, potentially breaking encryption and digital signatures that protect sensitive data, financial transactions, and digital infrastructure. Post-quantum algorithms use different mathematical foundations—such as lattice-based, hash-based, or code-based cryptography—that are believed to resist quantum attacks.
The technology addresses the existential threat that quantum computing poses to current cryptographic security. As quantum computers advance, they could break the encryption protecting everything from financial transactions to government communications to blockchain systems. Post-quantum cryptography provides a migration path to algorithms that will remain secure even when powerful quantum computers exist. Applications include securing financial systems, protecting government communications, securing blockchain and cryptocurrency systems, and ensuring long-term security of data that needs protection for decades. Standards bodies like NIST are standardizing post-quantum algorithms, and organizations are beginning migration.
At TRL 4, post-quantum cryptography algorithms have been selected and standardized, though migration and deployment are in early stages. The technology faces challenges including transitioning existing systems to new algorithms, ensuring interoperability, managing larger key sizes and computational requirements, and the need to migrate before quantum computers become a threat (since encrypted data can be stored now and decrypted later). However, as quantum computing advances, migration becomes urgent. The technology is essential for maintaining security in a post-quantum world, potentially protecting critical infrastructure, financial systems, and sensitive data from future quantum attacks, though the transition requires careful planning and coordination across industries and systems.
Related Organizations
The US federal agency leading the global competition to select and standardize post-quantum cryptographic algorithms.
Long-standing leader in neuro-symbolic AI, combining neural networks with logical reasoning for enterprise applications.
A spinout from Oxford University providing hardware and software IP for PQC, including side-channel analysis tools to test resistance.
Spun out of Alphabet, they provide a Security Suite that discovers cryptographic vulnerabilities and manages the migration to PQC.
Develops crypto-agile solutions and tools to test and migrate systems to quantum-safe standards.
Provides 'QuProtect', a software platform that monitors network traffic to detect and upgrade vulnerable cryptographic connections.
Co-founded by Michele Mosca, offering 'Quantum Risk Assessment' services and tools to evaluate organizational vulnerability to quantum decryption.
A major semiconductor manufacturer developing secure chips with hardware support for PQC algorithms.
Integrated quantum computing company formed by Honeywell and CQC.
A major European satellite manufacturer leading the ASCEND feasibility study.
A web infrastructure and security company that has already enabled PQC support for a significant portion of the internet.