Hardware Security Modules
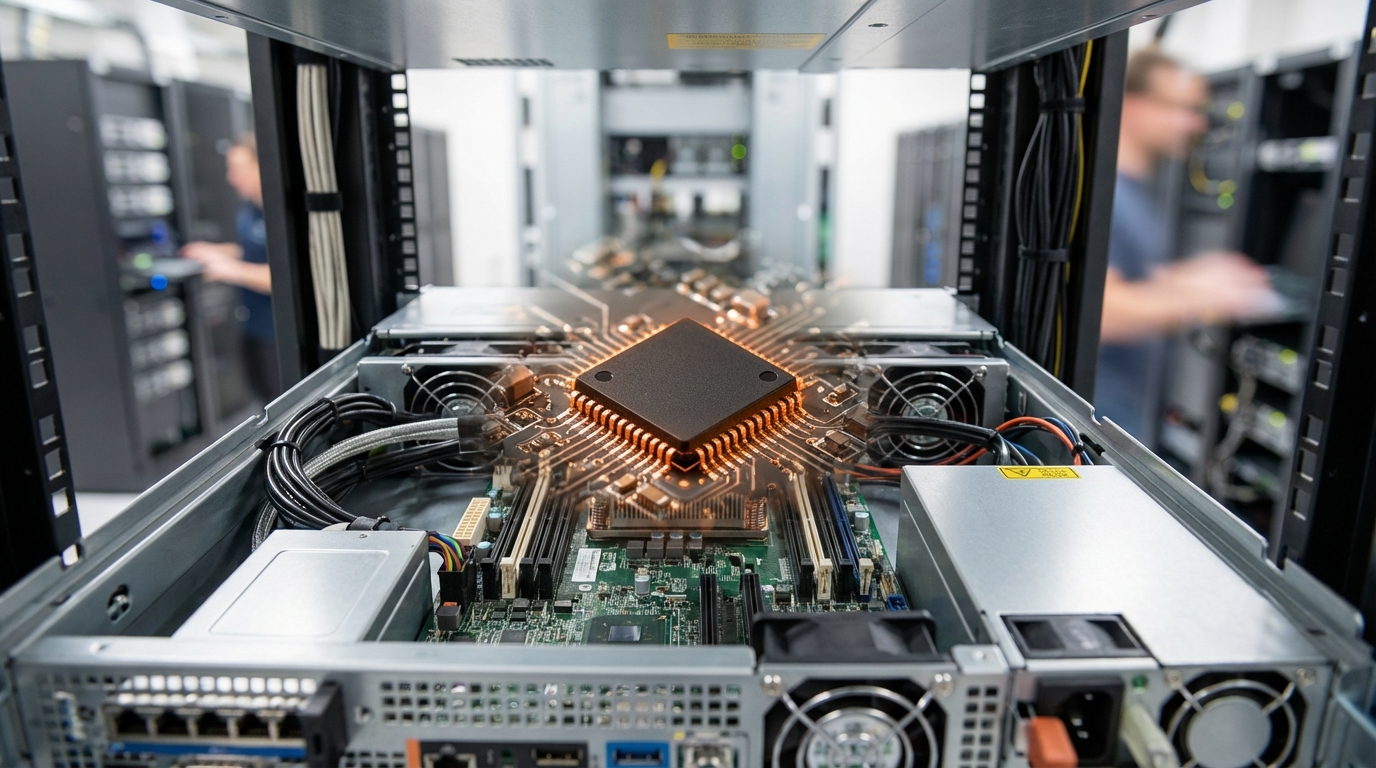
Hardware Security Modules represent purpose-built cryptographic processors designed to safeguard the most sensitive operations in digital trust infrastructure. Unlike software-based key storage, HSMs employ dedicated tamper-resistant hardware that physically protects cryptographic material from extraction or unauthorized access. These devices typically feature hardened enclosures with active defenses that detect and respond to physical intrusion attempts, often by zeroing sensitive memory or triggering irreversible destruction of key material. Inside, specialized secure cryptoprocessors perform encryption, decryption, digital signing, and key generation operations without ever exposing private keys to external systems or even to the host applications that invoke them. This architectural separation ensures that even if the surrounding infrastructure is compromised, the cryptographic keys themselves remain protected within the HSM's secure boundary. Modern HSMs support a range of cryptographic algorithms and standards, from traditional RSA and elliptic curve cryptography to emerging post-quantum algorithms, while maintaining strict compliance with security standards such as FIPS 140-2 Level 3 or Common Criteria EAL 4+.
The fundamental challenge these systems address is the concentration of trust in digital ecosystems. Certificate authorities must sign thousands of digital certificates daily, payment networks process millions of transactions requiring cryptographic validation, and government identity systems issue credentials that citizens rely upon for decades. In each case, the compromise of a single master signing key could cascade into systemic failure, invalidating entire trust chains or enabling widespread fraud. HSMs mitigate this risk by enforcing role-based access controls, requiring multi-person authorization for sensitive operations, and maintaining comprehensive audit logs that track every cryptographic operation. They also enable secure key lifecycle management, from initial generation through backup, rotation, and eventual retirement, ensuring that no single point of failure or human error can compromise the integrity of the trust infrastructure. For industries facing stringent regulatory requirements around data protection and financial security, HSMs provide the demonstrable assurance that cryptographic operations meet compliance standards and that key material is managed according to best practices.
HSMs have become standard infrastructure in sectors where trust and identity verification are paramount. Major certificate authorities deploy them to sign SSL/TLS certificates that secure web traffic, while payment card networks use HSMs to generate and protect the keys that authenticate billions of transactions annually. Cloud service providers increasingly offer HSM-as-a-service options, allowing organizations to leverage hardware-backed key protection without maintaining physical appliances. Government agencies employ HSMs to secure national identity programs, digital signature frameworks, and secure communication systems. As digital identity becomes more central to both commerce and civic life, the role of HSMs continues to expand into emerging domains such as blockchain networks, where they protect validator keys and signing operations, and Internet of Things ecosystems, where they anchor device identity and secure firmware updates. The convergence of stricter data protection regulations, growing sophistication of cyber threats, and the proliferation of zero-trust security architectures ensures that hardware-backed cryptographic assurance will remain a cornerstone of digital trust infrastructure for the foreseeable future.
Related Organizations
Prime contractor for the TeQuantS project and a key partner in ESA's quantum satellite initiatives.

Entrust
United States · Company
A global leader in identities, payments, and data protection.
Provides watsonx.governance for managing AI risk and compliance.
Specializes in enterprise-class HSMs for payment processing and general data encryption, offering both on-prem and cloud HSM services.
Develops high-speed data infrastructure semiconductors, including CXL technologies and PAM4 DSPs for interconnects.
Develops quantum-ready Hardware Security Modules (HSMs) and security platforms.
Brazilian cryptography company that developed the HSMs used in Brazil's electronic voting machines (Urna Eletrônica).
A leading Chinese provider of HSMs and cryptographic infrastructure.
Specializes in HSMs for the financial sector, particularly for the PIX payment system in Brazil.