Hardware Security Modules for Election Ops
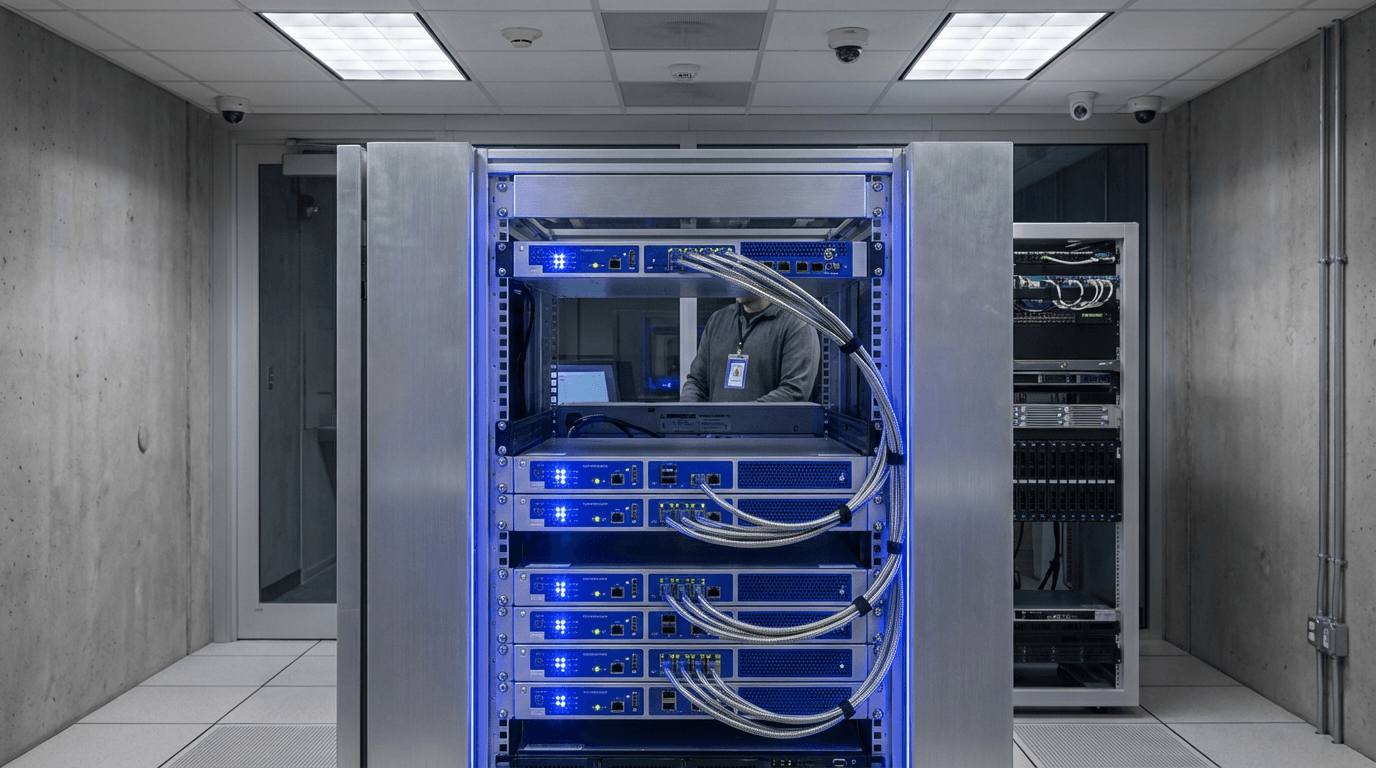
Hardware Security Modules (HSMs) for election operations are tamper-resistant physical devices designed to safeguard the most sensitive cryptographic operations underpinning democratic processes. Unlike software-based security measures that can be compromised through malware or unauthorised access, HSMs provide a hardware root of trust—a physically isolated environment where cryptographic keys are generated, stored, and used without ever being exposed to potentially vulnerable systems. These devices enforce strict access controls and operational policies at the hardware level, ensuring that critical operations such as digitally signing election firmware updates, encrypting vote tallies during transmission, or managing authentication credentials for voter registration databases occur within a protected boundary. The HSM itself typically includes physical tamper-detection mechanisms that can destroy key material if unauthorised access is attempted, and it maintains detailed, cryptographically signed audit logs of every operation performed, creating an immutable record of who accessed what keys and when.
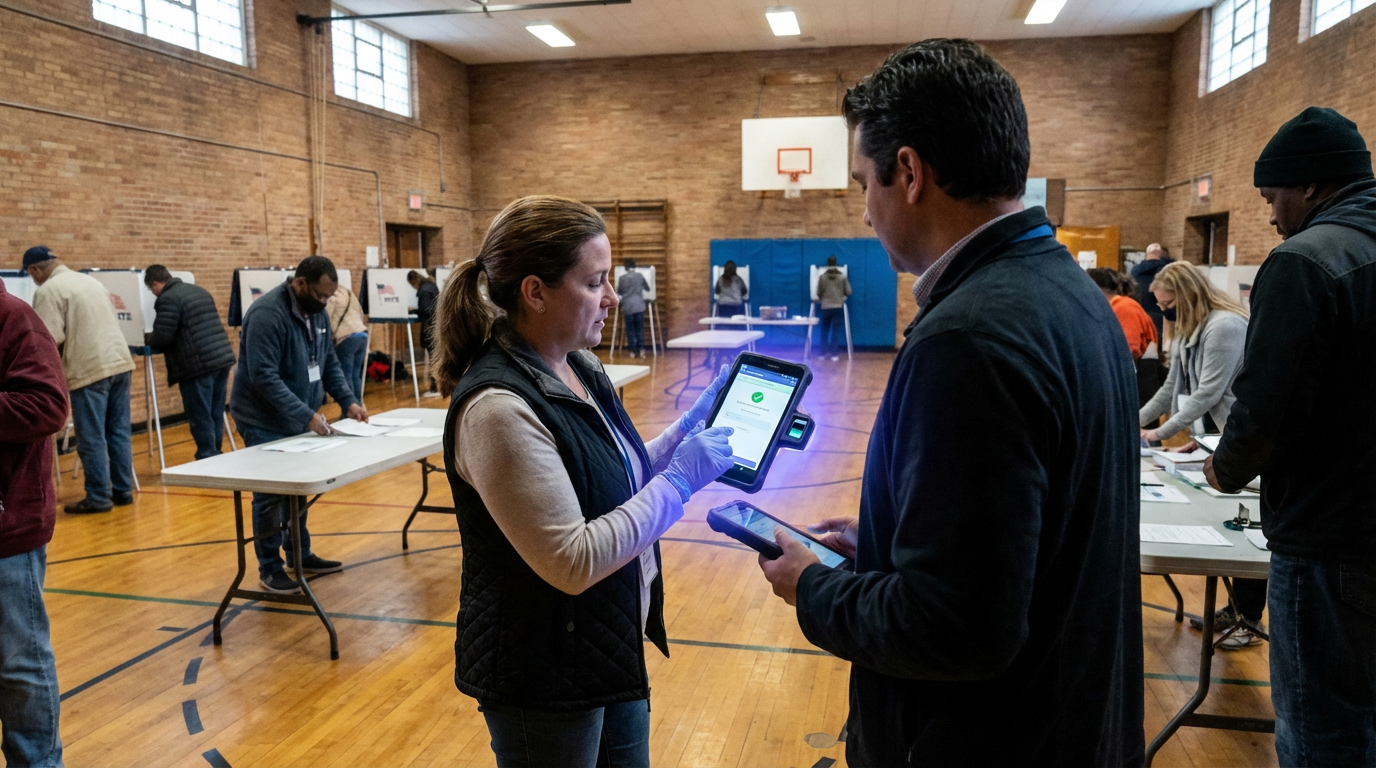
In the context of election administration, HSMs address several critical vulnerabilities that have historically plagued electoral systems. Election infrastructure must balance accessibility—enabling thousands of poll workers and administrators to perform their duties—with security, preventing any single individual or small group from manipulating results or compromising voter privacy. Traditional key management approaches, where cryptographic keys might be stored on general-purpose computers or even written down, create insider risk scenarios where malicious or coerced election officials could potentially alter vote counts, forge authentication credentials, or decrypt sensitive voter information. HSMs mitigate these risks by implementing multi-party authorisation schemes, where multiple election officials must physically authenticate to the device before sensitive operations can proceed, and by ensuring that keys never leave the protected hardware environment. This separation of duties makes it exponentially more difficult for any single actor to compromise election integrity, while the detailed audit trails provide forensic evidence that can be examined during post-election reviews or investigations.
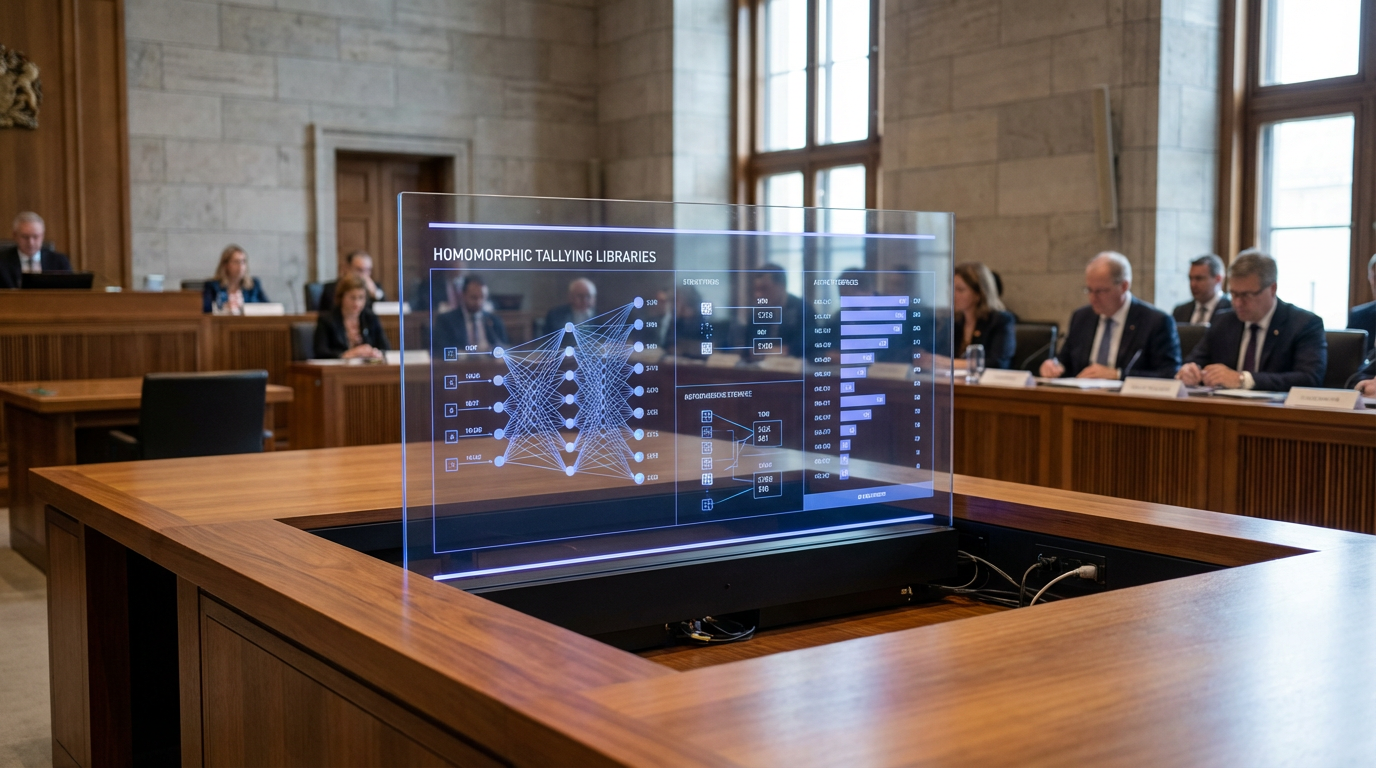
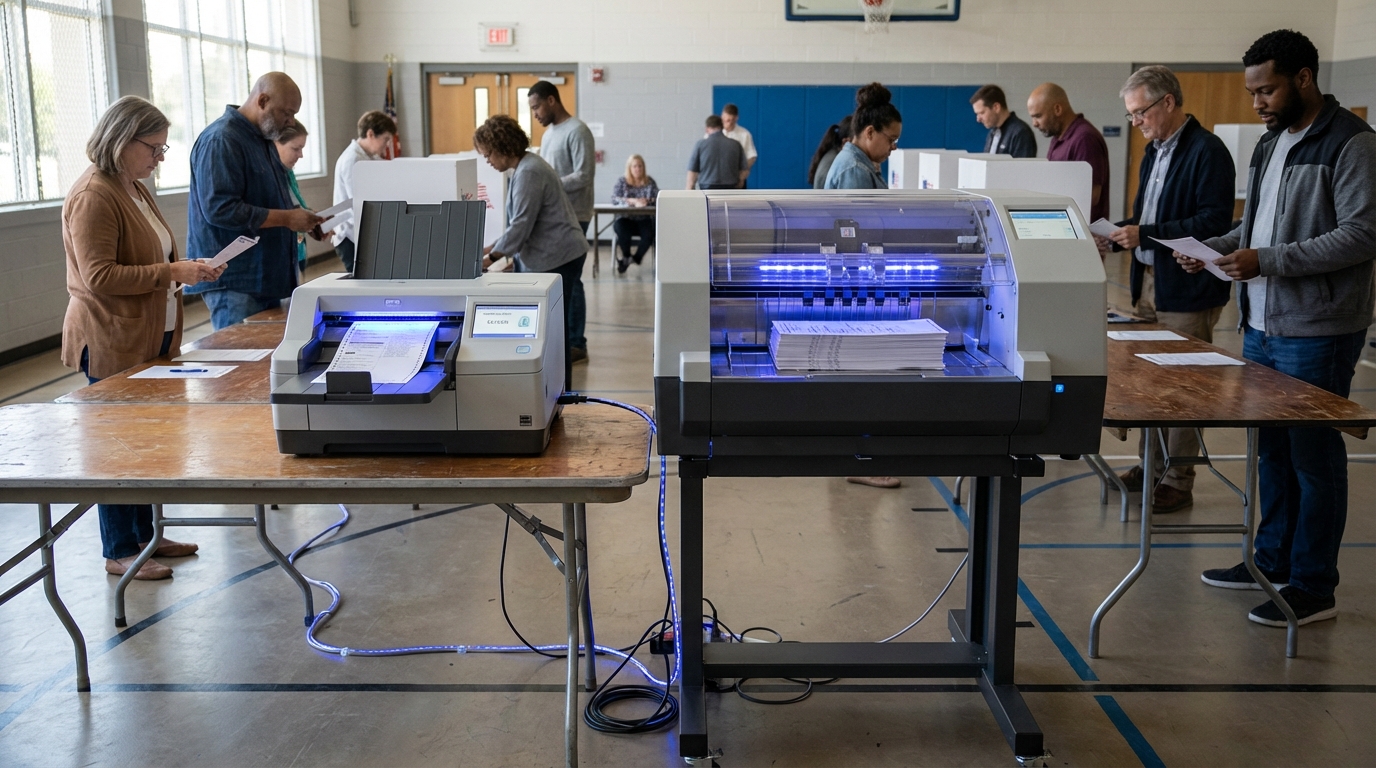
Several election jurisdictions have begun piloting HSM deployments for specific high-risk operations, particularly in securing the chain of custody for electronic vote tallies as they move from polling places to central tabulation facilities. Research in election security suggests that hardware-based key protection significantly reduces the attack surface compared to software-only approaches, particularly against sophisticated adversaries with access to election systems. As concerns about election security intensify globally, and as more jurisdictions adopt electronic systems for voter registration, ballot marking, or results reporting, the role of HSMs in establishing verifiable trust anchors becomes increasingly important. The technology aligns with broader movements toward defense-in-depth security architectures and zero-trust models in critical infrastructure, where no single component or individual is implicitly trusted. Looking forward, the integration of HSMs into election operations represents a maturation of electoral cybersecurity practices, moving beyond perimeter defenses to protect the cryptographic foundations that enable secure, auditable, and trustworthy democratic processes in an increasingly digital age.
Related Organizations

Entrust
United States · Company
A global leader in identities, payments, and data protection.
Brazilian cryptography company that developed the HSMs used in Brazil's electronic voting machines (Urna Eletrônica).
Prime contractor for the TeQuantS project and a key partner in ESA's quantum satellite initiatives.
US federal agency that sets standards for technology, including facial recognition vendor tests (FRVT).
Independent agency of the US government focused on election administration.

Smartmatic
United Kingdom · Company
A multinational company that builds and implements electronic voting systems.
Maker of the YubiKey and YubiHSM, a small form-factor hardware security module.
A major semiconductor manufacturer developing secure chips with hardware support for PQC algorithms.