FIDO Security Keys
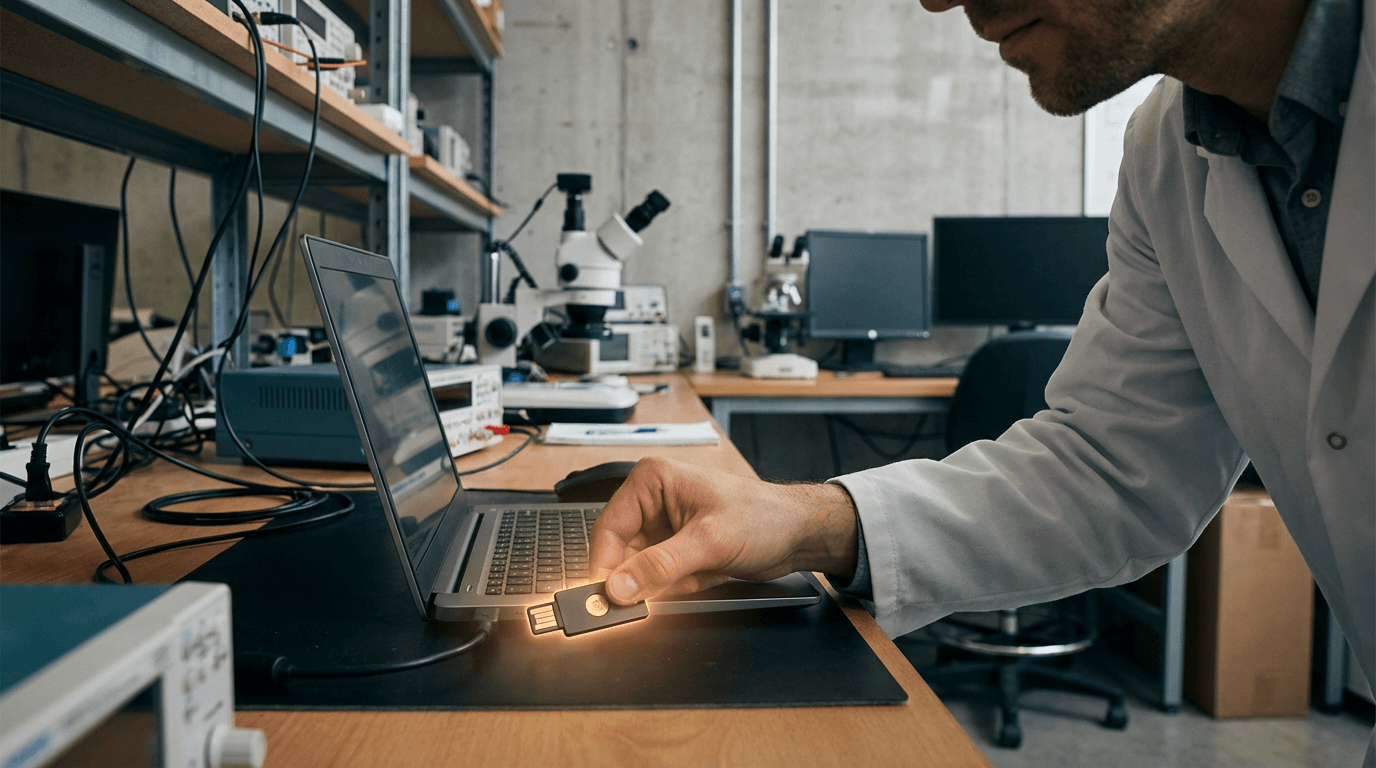
FIDO Security Keys represent a fundamental shift in digital authentication, moving away from traditional password-based systems toward hardware-backed cryptographic verification. These physical devices—typically small USB dongles, NFC-enabled tokens, or Bluetooth authenticators—store private cryptographic keys that never leave the device itself. When a user attempts to log in to a service, the security key performs a cryptographic challenge-response exchange, proving possession of the correct credential without transmitting any secret information over the network. This approach is built on public-key cryptography, where the private key remains secured within the hardware token's tamper-resistant chip, while the corresponding public key is registered with the service provider. Critically, FIDO credentials are domain-bound, meaning they only work with the specific website or service they were registered to, creating an inherent defense against phishing attempts that try to impersonate legitimate sites.
The authentication landscape has long struggled with fundamental vulnerabilities inherent to password-based systems. Passwords can be stolen through data breaches, guessed through brute-force attacks, intercepted through man-in-the-middle exploits, or simply tricked out of users through sophisticated phishing campaigns. Even multi-factor authentication methods like SMS codes or authenticator apps remain vulnerable to real-time phishing attacks and SIM-swapping schemes. FIDO Security Keys address these systemic weaknesses by requiring physical possession of the hardware token and eliminating any shared secrets that could be compromised remotely. This makes credential stuffing attacks—where attackers use stolen username-password combinations from one breach to access accounts elsewhere—completely ineffective. For organizations, this translates to dramatically reduced risk of account takeovers, lower support costs associated with password resets, and simplified compliance with security frameworks that mandate strong authentication. The technology also enables true passwordless experiences, where users can authenticate with just the security key and a simple PIN or biometric, removing the cognitive burden of managing complex passwords across dozens of services.
Major technology platforms have increasingly embraced FIDO authentication, with widespread support now available across consumer services, enterprise identity systems, and government applications. Financial institutions have deployed security keys to protect high-value transactions and administrative access, while technology companies offer them as optional or required authentication factors for account recovery and sensitive operations. In the public sector, agencies handling classified information or critical infrastructure have adopted FIDO keys as part of zero-trust security architectures. The technology has also found applications in healthcare settings, where protecting patient data requires robust authentication that doesn't impede clinical workflows. As the FIDO Alliance continues to expand its specifications—including newer passkey standards that extend the same cryptographic principles to built-in device authenticators—the distinction between dedicated hardware tokens and integrated platform authenticators is evolving. This convergence points toward a future where phishing-resistant authentication becomes the default rather than the exception, fundamentally reshaping how individuals and organizations approach digital identity verification in an increasingly threat-laden environment.
Related Organizations
Open industry association developing standards for passwordless authentication (Passkeys) that keep biometric data local to the device.
Maker of the YubiKey and YubiHSM, a small form-factor hardware security module.
A major global supplier of FIDO-certified hardware tokens, smart cards, and OEM security keys for large technology companies.
A developer of open-source hardware FIDO2 security keys, offering transparent firmware and hardware designs.
Specializes in fingerprint-enabled FIDO2 security keys, combining biometrics with hardware token security.
Manufactures the G-series FIDO2 security keys, formerly part of eWBM, focusing on high-security hardware authenticators.
A security technology company producing uTrust FIDO2 NFC security keys alongside physical access control systems.
Swiss manufacturer of programmable hardware tokens and FIDO2 security keys.
Produces the VeriMark line of fingerprint security keys that support FIDO2/WebAuthn.