Secure Elements & eSIMs
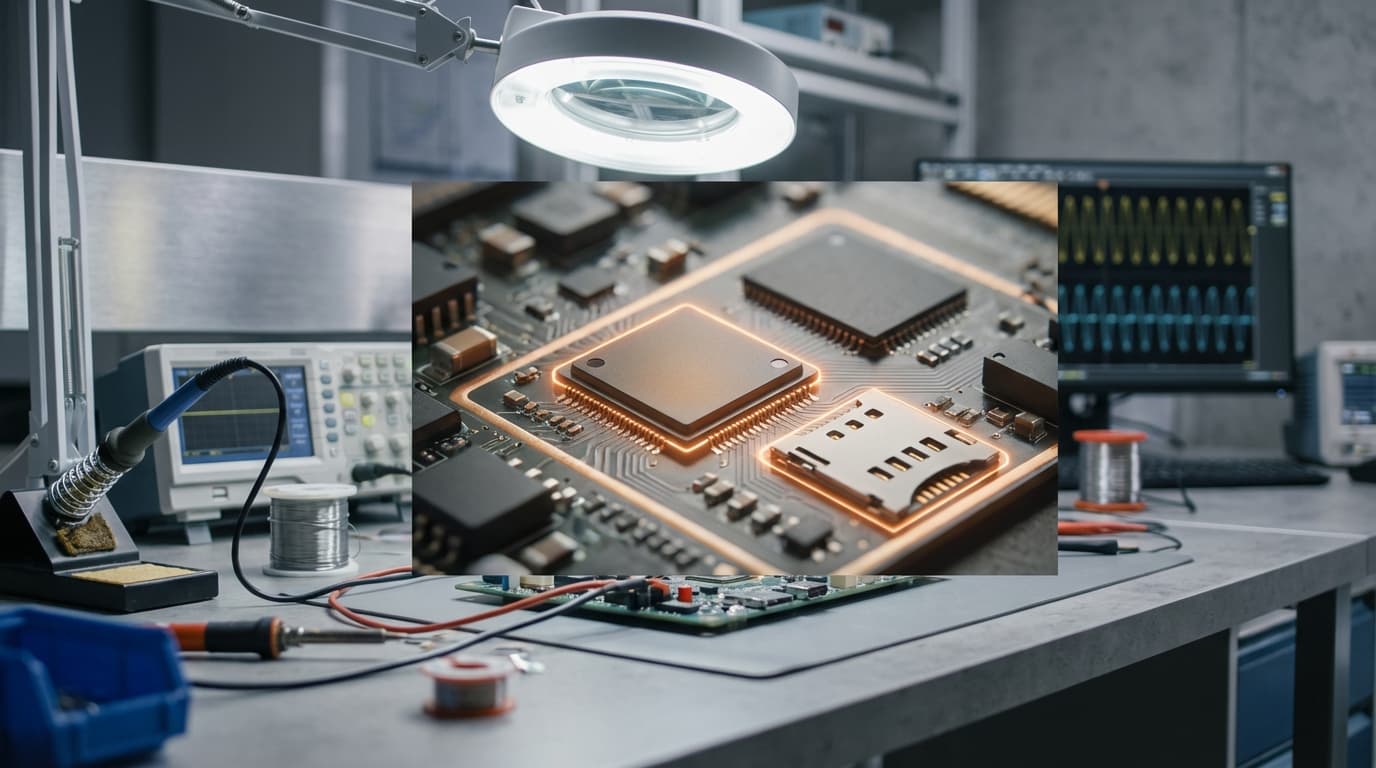
Secure Elements represent a critical hardware-based security architecture designed to protect sensitive cryptographic material and digital credentials from both software and physical attacks. These dedicated chips, typically certified to rigorous standards such as Common Criteria EAL5+ or FIPS 140-2 Level 3, create an isolated execution environment separate from a device's main processor. Within this protected enclave, cryptographic operations occur in a manner that prevents extraction of private keys even if the host device is compromised. The technology encompasses several implementations, including discrete chips soldered onto circuit boards, embedded Secure Elements integrated into system-on-chip designs, and eSIMs (embedded Subscriber Identity Modules) that replace traditional removable SIM cards. The fundamental mechanism relies on multiple layers of protection: physical tamper-detection circuits that can erase sensitive data if intrusion is detected, secure boot processes that verify code integrity, and cryptographic co-processors optimised for operations like signing, encryption, and key generation. Unlike software-based security solutions that depend on the integrity of the operating system, Secure Elements provide a hardware root of trust that remains resilient even when surrounding systems are compromised.
The telecommunications and financial services industries face persistent challenges in protecting user credentials and transaction data across billions of distributed devices. Traditional approaches relying solely on software security have proven vulnerable to sophisticated attacks, including malware that can extract credentials from device memory or intercept authentication tokens. Secure Elements address these vulnerabilities by ensuring that critical secrets never leave the protected hardware boundary in unencrypted form. For mobile network operators, eSIM technology solves the logistical complexity of physical SIM distribution while enabling remote provisioning of subscriber profiles, facilitating seamless carrier switching and supporting devices too small for traditional SIM slots. In the payments ecosystem, these chips enable contactless transactions by securely storing payment credentials and performing cryptographic operations required for tokenisation, allowing smartphones and wearables to function as payment instruments without exposing actual card numbers. The technology also unlocks new business models in IoT deployments, where devices require long-term authentication credentials that must remain secure throughout extended operational lifetimes in potentially hostile physical environments. By providing hardware-enforced security boundaries, Secure Elements enable service providers to meet stringent regulatory requirements for data protection while reducing fraud losses associated with credential theft.
Secure Element technology has achieved widespread commercial deployment across multiple sectors, with billions of chips currently in circulation worldwide. Major smartphone manufacturers have integrated these components as standard features, supporting applications ranging from mobile payments to digital car keys and government-issued digital identity credentials. The eSIM variant has gained particular momentum, with telecommunications standards bodies establishing interoperable provisioning protocols that allow users to activate cellular service without physical SIM cards—a capability now standard in flagship smartphones, smartwatches, and connected tablets. Financial institutions have embraced Secure Elements for tokenised payment solutions, while automotive manufacturers increasingly rely on them for vehicle access control and secure vehicle-to-infrastructure communication. Looking forward, the technology is positioned to play an expanding role as digital identity systems mature and governments explore hardware-backed credentials for services like digital driver's licenses and health records. Industry analysts note growing interest in integrating Secure Elements with emerging technologies such as decentralised identity frameworks and blockchain-based authentication systems, where hardware-protected private keys could anchor self-sovereign identity models. As cyber threats continue to evolve and regulatory frameworks demand stronger protection for personal data, the combination of hardware security and flexible remote provisioning offered by Secure Elements and eSIMs represents an increasingly essential foundation for trustworthy digital services across connected ecosystems.
Related Organizations
The standard body responsible for the specifications of Secure Elements and Trusted Execution Environments (TEE).

GSMA
United Kingdom · Consortium
The industry organization for mobile operators, which runs the 'Connected Women' and 'Mobile for Development' programs supporting m-learning.
Leading manufacturer of Near Field Communication (NFC) and Secure Element chips used in offline payment hardware.
A major semiconductor manufacturer developing secure chips with hardware support for PQC algorithms.
Creator of FlightSense time-of-flight (ToF) sensors widely used in Android smartphones for depth sensing.
German security technology group specializing in currency and asset protection.

Kigen
United Kingdom · Company
A spin-out from Arm specializing in iSIM (Integrated SIM) and eSIM operating systems.
Offers the AI Stack which includes tools for hardware-aware model efficiency and architecture search.
A global provider of secure solutions, including eSIMs and secure elements for banking and mobile.