Trusted Device Attestation for Field Staff
In democratic systems, the integrity of electoral processes depends not only on secure voting machines but also on the trustworthiness of the devices used by poll workers, election inspectors, and field staff who manage voter registration, provisional ballots, and incident reporting. Traditional approaches to device security have relied primarily on software-based protections, which can be circumvented by sophisticated attacks that compromise the operating system or firmware. Trusted Device Attestation addresses this vulnerability by leveraging hardware-based security mechanisms embedded directly into the device's processor and secure elements. These mechanisms include secure boot processes that verify the integrity of firmware and operating system components during startup, measured boot protocols that create cryptographic records of each stage of the boot process, and runtime attestation capabilities that can prove to remote verification services that the device remains in a known-good state. By anchoring trust in tamper-resistant hardware rather than software alone, this approach creates a verifiable chain of trust from the device's initial power-on through the execution of critical election applications.
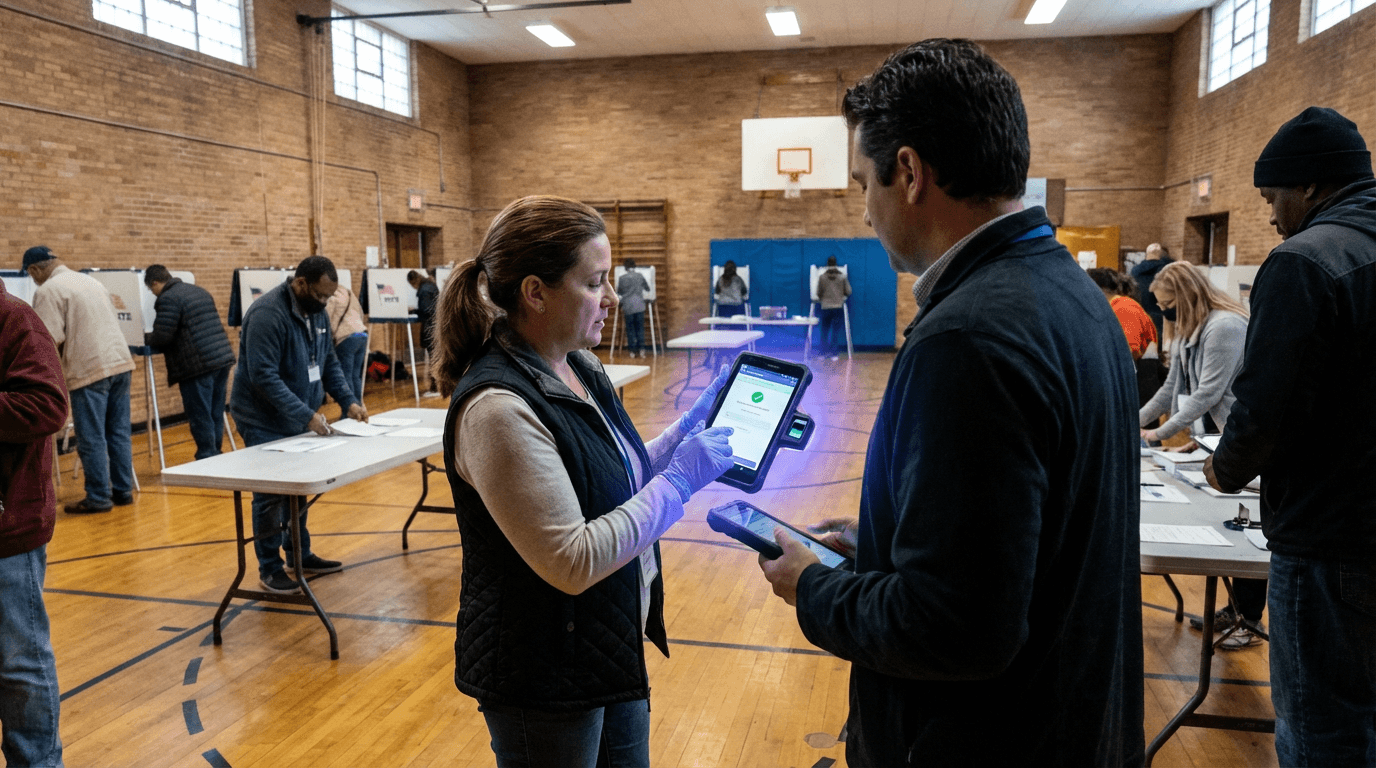
The deployment of trusted attestation in electoral contexts addresses several critical challenges that have emerged as jurisdictions increasingly rely on mobile technology for field operations. Poll workers often use tablets to check voter registration, process provisional ballots, update voter rolls in real-time, and document irregularities or equipment failures. If these devices are compromised—whether through malware, physical tampering, or supply chain attacks—the consequences could range from data breaches exposing voter information to the manipulation of provisional ballot records or the suppression of incident reports. Hardware-backed attestation enables election authorities to continuously verify that devices are running authorised software configurations and have not been altered since their last verification. This capability is particularly valuable in scenarios where devices must be distributed to numerous polling locations, potentially leaving them vulnerable to tampering during transport or storage. Furthermore, attestation mechanisms can generate cryptographic proof of device integrity that can be logged and audited, creating an additional layer of transparency and accountability in election administration.
While comprehensive deployment of trusted attestation for electoral field devices remains in early stages, research initiatives and pilot programs have begun exploring its application in high-stakes civic contexts. Industry analysts note that the technology builds upon existing hardware security features already present in many commercial mobile devices, such as Trusted Platform Modules and secure enclaves, making adoption more feasible than entirely new infrastructure would require. Early deployments indicate that attestation workflows can be integrated into existing election management systems, allowing central servers to verify device integrity before permitting access to sensitive voter databases or ballot processing applications. As concerns about election security continue to intensify globally, trusted device attestation represents a convergence of hardware security advances with the specific requirements of democratic governance. The approach aligns with broader trends toward zero-trust architectures in critical infrastructure, where continuous verification replaces assumptions of inherent trustworthiness. Looking forward, the maturation of this technology could extend beyond elections to other civic functions requiring verified device integrity, from census operations to emergency response coordination, establishing new standards for how governments ensure the authenticity of field operations in an increasingly digital civic landscape.





