Threat Modeling & Security Testing for Election Systems
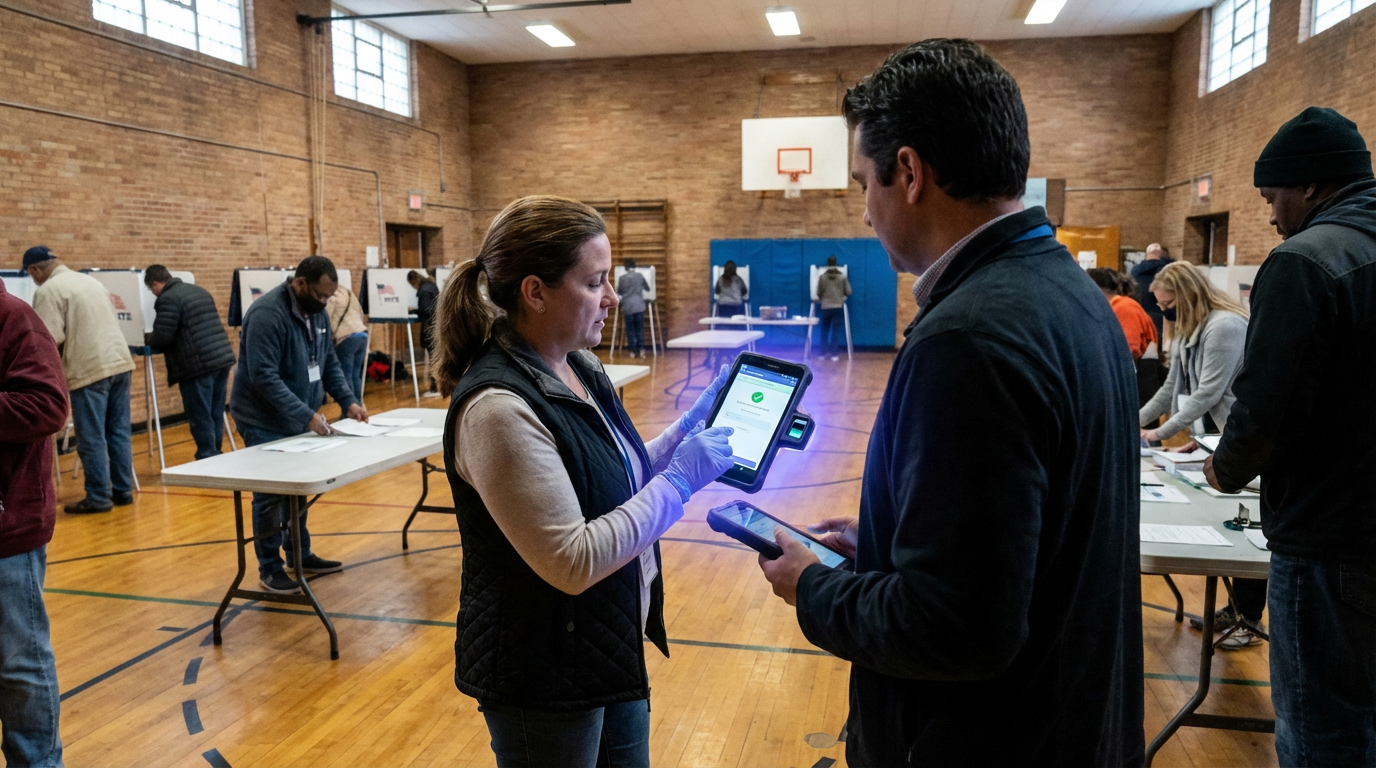
Democratic institutions rest on the public's confidence that votes are counted accurately and that election outcomes reflect the genuine will of the electorate. Yet modern voting infrastructure—spanning electronic poll books, ballot-marking devices, tabulation systems, and voter registration databases—presents a complex attack surface vulnerable to manipulation, disruption, or data compromise. Threat modeling and security testing for election systems address this challenge through systematic adversary analysis and continuous hardening protocols. At its technical core, this approach applies formal security engineering methodologies to civic infrastructure: structured threat modeling frameworks identify potential attack vectors and adversary capabilities, penetration testing simulates real-world intrusion attempts against voting hardware and software, firmware reviews examine low-level code for backdoors or vulnerabilities, supply-chain audits trace components from manufacture through deployment, and tabletop exercises rehearse incident response under realistic scenarios. These techniques draw from cybersecurity practices developed for critical infrastructure protection but are adapted to the unique constraints of election systems, which must balance security with transparency, auditability, and accessibility requirements that differ markedly from traditional IT environments.
The stakes of election security extend beyond technical robustness to encompass democratic legitimacy itself. A single undetected vulnerability or successful intrusion can undermine public trust even when vote tallies remain accurate, while the perception of insecurity—whether justified or manufactured—can delegitimise electoral outcomes and destabilise governance. Formal security testing addresses both dimensions by systematically hardening systems against nation-state adversaries with sophisticated capabilities and insider threats with privileged access, while simultaneously generating credible, transparent evidence of resilience that election officials can present to the public. This dual function proves especially valuable in contexts where disinformation campaigns exploit technical complexity to sow doubt. By documenting security measures through independent audits and publishing sanitised findings, jurisdictions can counter baseless claims while demonstrating accountability. The approach also enables jurisdictions to prioritise limited security resources by identifying which components face the greatest risk and which mitigations deliver the most significant risk reduction, ensuring that hardening efforts focus on the most consequential vulnerabilities rather than pursuing theoretical perfection.
Adoption of rigorous security testing for election infrastructure has accelerated following high-profile incidents and growing awareness of sophisticated threats, with many jurisdictions now conducting pre-election penetration tests and post-election audits as standard practice. Research institutions and non-profit organisations have developed specialised frameworks tailored to voting systems, while some election authorities have established ongoing red-team exercises that continuously probe defences throughout the electoral cycle rather than limiting testing to pre-election windows. These efforts increasingly incorporate supply-chain verification, recognising that vulnerabilities introduced during manufacturing or distribution can persist undetected for years. Looking forward, the integration of threat modeling into the entire lifecycle of election technology—from procurement specifications through decommissioning—represents a maturation of election security from reactive patching to proactive resilience engineering. As geopolitical tensions intensify and adversarial capabilities evolve, the systematic application of security testing methodologies will likely become not merely best practice but a foundational requirement for maintaining democratic legitimacy in an era where the integrity of civic infrastructure can no longer be assumed but must be continuously demonstrated and defended.
Related Organizations
Nonprofit responsible for the CIS Controls and the Elections Infrastructure Information Sharing and Analysis Center (EI-ISAC).
US federal agency responsible for guiding the government's migration to post-quantum cryptography.
A nonprofit election technology research and development institute.
A computer science R&D firm specializing in formal verification and cryptography.
A non-partisan organization advocating for legislation and regulation that promotes accuracy, transparency, and verifiability of elections.
A non-partisan non-profit building open-source, verifiable voting machines.

Dominion Voting Systems
United States · Company
A major North American vendor of electronic voting hardware and software.
The largest manufacturer of voting machines in the United States.
Through Copilot and the 'Recall' feature in Windows, Microsoft is integrating persistent memory and agentic capabilities directly into the operating system.
A security testing platform that combines human intelligence with AI to find vulnerabilities.