End-to-End Verifiable Voting (E2E-V) Protocols
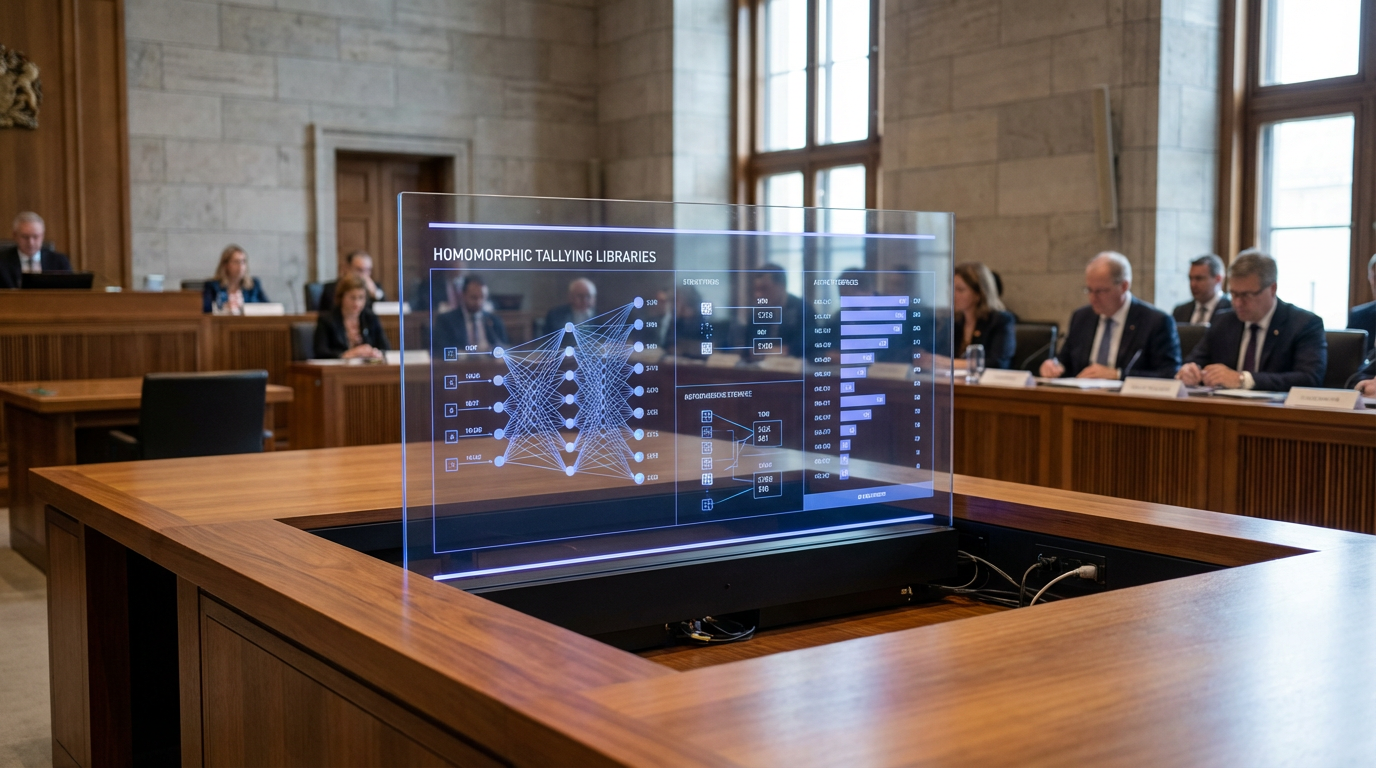
End-to-End Verifiable Voting (E2E-V) protocols represent a sophisticated cryptographic approach to electoral systems that addresses fundamental tensions between ballot secrecy and election integrity. Unlike traditional voting methods where voters must trust election officials and equipment without independent verification, E2E-V systems provide mathematical proofs that allow voters to confirm their individual votes were correctly recorded while simultaneously enabling anyone to verify that the final tally accurately reflects all cast ballots. These protocols typically employ one of two core cryptographic architectures: mixnet-based systems, which shuffle encrypted ballots through a series of servers to break the link between voters and their choices, or homomorphic encryption schemes, which allow votes to be tallied while still encrypted. Both approaches generate zero-knowledge proofs—cryptographic evidence that computations were performed correctly without revealing the underlying data. Voters receive a tracking code or receipt that allows them to verify their encrypted ballot appears in the public bulletin board, while the cryptographic properties ensure that even with this verification capability, no one can prove how they voted to a third party, preserving ballot secrecy and preventing vote buying or coercion.
The democratic challenges these protocols address are profound and increasingly urgent. Traditional electronic voting systems have faced persistent concerns about software vulnerabilities, insider manipulation, and the impossibility of meaningful audits when votes exist only as bits in proprietary systems. Even paper-based systems, while auditable, require voters to trust that their ballots are handled correctly after submission. E2E-V protocols fundamentally transform this trust model by making the entire electoral process transparent to mathematical verification rather than institutional authority. This shift is particularly valuable in contexts where electoral legitimacy is contested or where public confidence in democratic institutions has eroded. The technology enables a new form of civic participation where technically inclined observers, civil society organisations, or political parties can independently verify election outcomes using publicly posted cryptographic evidence, without requiring access to sealed ballot boxes or proprietary vote-counting software. This public verifiability can help resolve electoral disputes through mathematical proof rather than institutional decree, potentially reducing post-election conflicts.
Several democracies have begun deploying E2E-V systems in binding elections, with notable implementations in municipal elections in Takoma Park, Maryland, and trials in countries including Estonia, Switzerland, and Australia. Research institutions and election authorities continue to refine these protocols, addressing practical challenges such as usability for non-technical voters, accessibility for people with disabilities, and integration with existing electoral infrastructure. The technology faces a critical adoption threshold: while cryptographic security is well-established, voter understanding and trust remain essential for legitimacy. Current development efforts focus on creating intuitive verification interfaces and educational frameworks that allow ordinary citizens to benefit from cryptographic guarantees without requiring expertise in mathematics. As concerns about election security intensify globally and as digital governance becomes more prevalent, E2E-V protocols represent a promising pathway toward electoral systems that are simultaneously more secure, more transparent, and more resistant to both technical attacks and institutional manipulation, potentially reshaping how democratic societies establish and maintain electoral legitimacy in an increasingly digital age.
Related Organizations
A non-partisan non-profit building open-source, verifiable voting machines.
Through Copilot and the 'Recall' feature in Windows, Microsoft is integrating persistent memory and agentic capabilities directly into the operating system.
A non-partisan organization advocating for legislation and regulation that promotes accuracy, transparency, and verifiability of elections.
A computer science R&D firm specializing in formal verification and cryptography.
An open-source, web-based open-audit voting system.
A nonprofit election technology research and development institute.
The national postal service of Switzerland, which operates a state-approved e-voting system.
Provides secure digital voting solutions for associations, municipalities, and parties.

Smartmatic
United Kingdom · Company
A multinational company that builds and implements electronic voting systems.