Autonomous Cyber Defense Agents
Modern cybersecurity teams face an overwhelming challenge: the volume and velocity of cyber threats have far outpaced human capacity to respond. Traditional security operations centers rely on analysts to investigate alerts, determine appropriate responses, and execute remediation steps—a process that can take hours or days while attackers move laterally through networks in minutes. This gap between detection and response creates a critical vulnerability, particularly in environments with limited security staff, during off-hours, or when sophisticated adversaries employ automated attack tools that operate at machine speed. Autonomous cyber defense agents address this fundamental asymmetry by deploying AI-driven systems that can perceive threats, make decisions, and take protective actions without human intervention, operating continuously across endpoints, servers, cloud infrastructure, and operational technology networks.
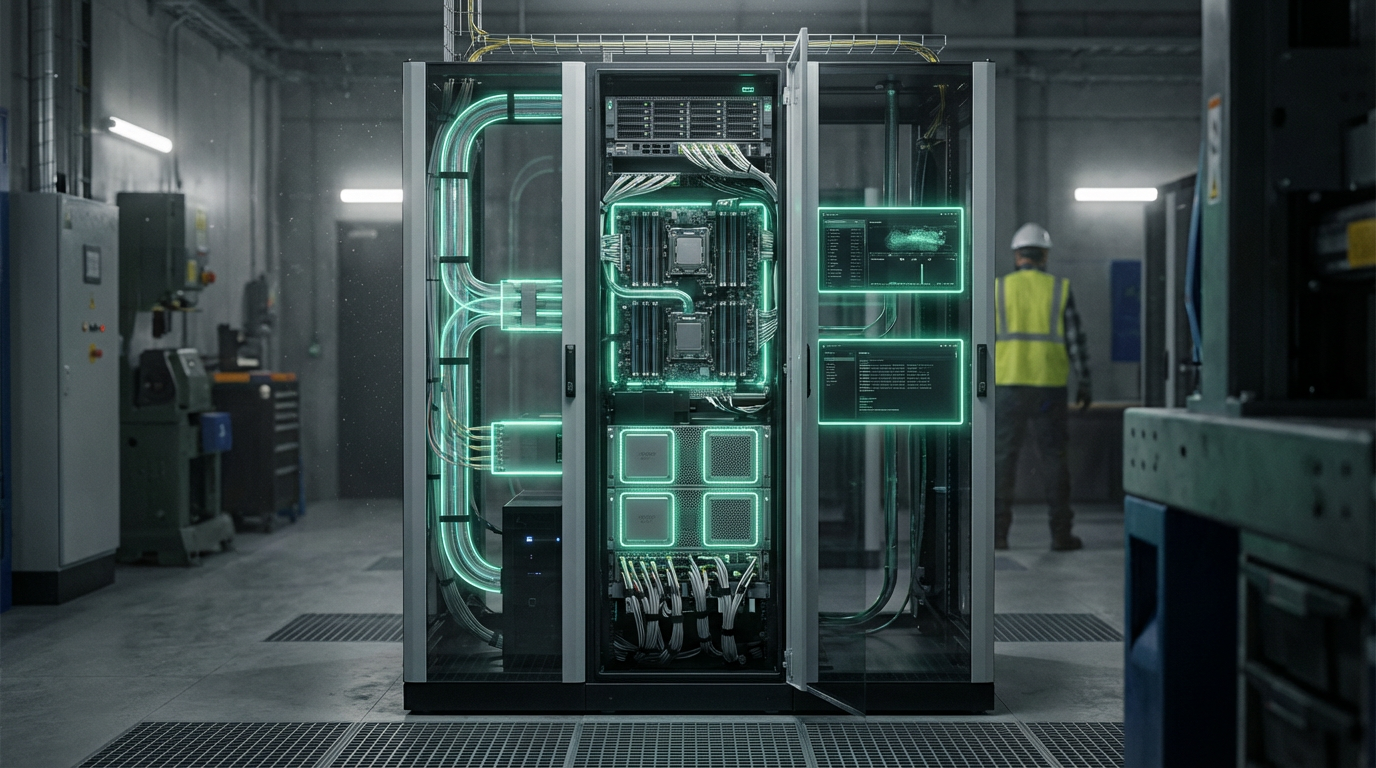
These agents function through a combination of behavioral analysis, anomaly detection, and predefined response playbooks encoded within strict policy boundaries. Rather than simply generating alerts for human review, they autonomously execute containment actions such as isolating compromised endpoints from the network, terminating malicious processes, blocking suspicious network connections, or reverting unauthorized configuration changes. The systems continuously learn normal patterns of network traffic, user behavior, and system operations, enabling them to identify deviations that may indicate intrusion attempts, malware execution, or insider threats. Crucially, these agents operate within carefully defined guardrails that prevent them from taking actions that could disrupt critical business operations—for instance, they might quarantine a suspicious file but require human approval before shutting down a production server. This bounded autonomy allows organizations to achieve rapid threat containment while maintaining oversight of high-impact decisions.
Early deployments in critical infrastructure sectors and large enterprises indicate that autonomous defense agents can reduce mean time to containment from hours to seconds, significantly limiting the damage from successful intrusions. Financial institutions are using these systems to protect against credential theft and fraudulent transactions, while manufacturing facilities deploy them to safeguard operational technology environments where traditional security tools often cannot operate. The technology represents a shift from purely detective security controls to autonomous protective systems that can match the speed and persistence of modern cyber threats. As attack sophistication continues to escalate and the cybersecurity workforce shortage persists, autonomous defense agents are becoming essential components of resilient security architectures, enabling organizations to maintain effective protection even when human defenders are unavailable or overwhelmed by alert fatigue.
Related Organizations
Uses self-learning AI to detect and respond to cyber threats across IT and OT/industrial environments.
A research and development agency of the United States Department of Defense.
Provides the Singularity Platform which uses on-device AI to autonomously detect and remediate threats.
Offers Cortex XSIAM, an autonomous security operations platform driven by AI.
The Falcon platform utilizes AI for automated threat detection and real-time response.
Specializes in AI-driven Attack Signal Intelligence to automate threat detection and response across hybrid clouds.
Applies deep learning to cybersecurity to predict and prevent attacks before execution.
Through Copilot and the 'Recall' feature in Windows, Microsoft is integrating persistent memory and agentic capabilities directly into the operating system.
Global leader in broad, integrated, and automated cybersecurity solutions.

BlueVoyant
United States · Company
Provides internal and external cyber defense capabilities with automated remediation.