Fully Homomorphic Encryption (FHE)
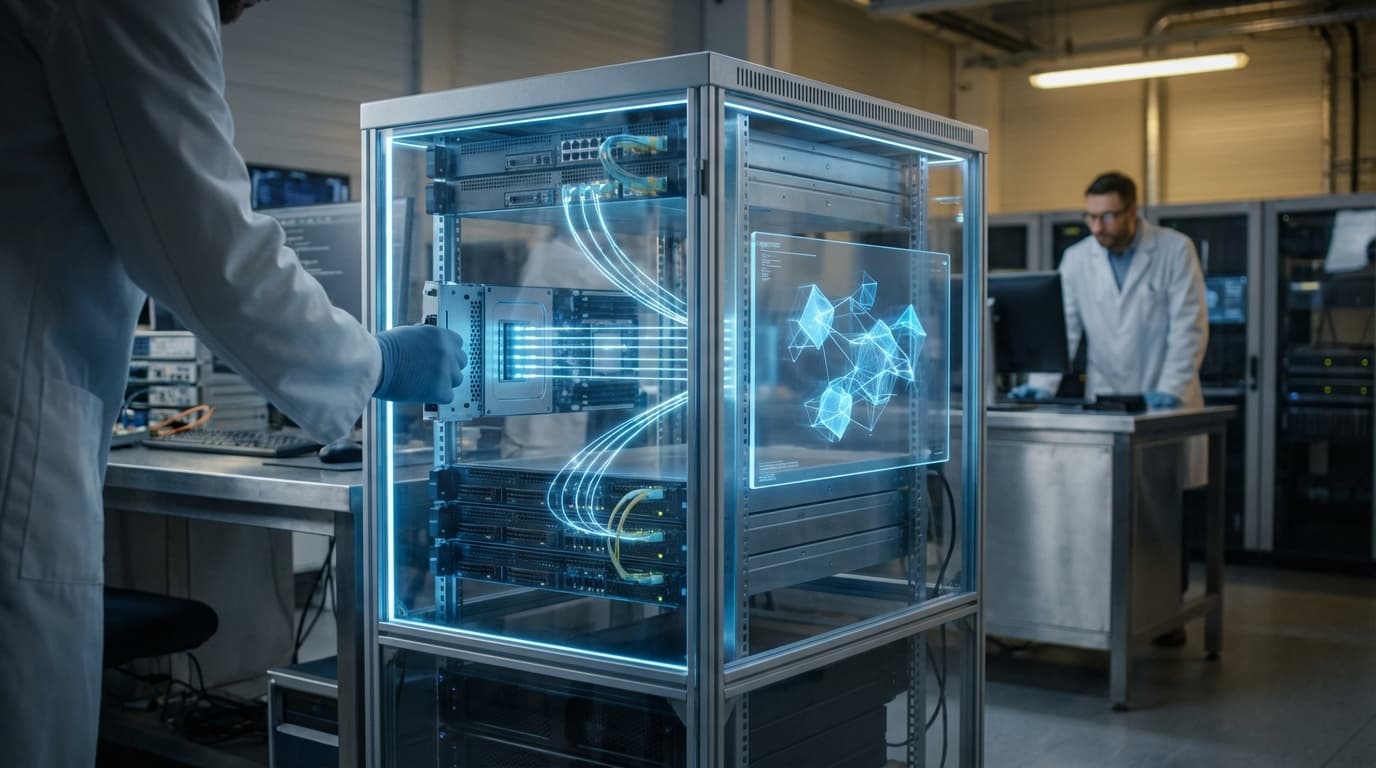
Fully Homomorphic Encryption represents a fundamental advancement in cryptographic technology that enables mathematical operations to be performed directly on encrypted data without ever exposing the underlying information. Unlike traditional encryption methods that require data to be decrypted before any computation can occur, FHE maintains data in its encrypted state throughout the entire processing lifecycle. The technology works through sophisticated mathematical lattice-based cryptographic schemes that preserve the structural relationships within data even when encrypted, allowing addition, multiplication, and other operations to produce encrypted results that, when decrypted, match what would have been obtained from performing the same operations on plaintext data. This capability addresses a critical limitation in cloud computing and data sharing: the fundamental tension between leveraging powerful external computational resources and maintaining absolute data confidentiality.
For financial institutions, this technology solves a persistent dilemma that has constrained innovation and operational efficiency. Banks and insurance companies possess vast troves of sensitive customer data—transaction histories, credit scores, medical records, investment portfolios—that could yield valuable insights through advanced analytics and machine learning. However, regulatory requirements, privacy concerns, and competitive considerations have traditionally prevented these institutions from fully leveraging third-party cloud services or collaborative data analysis. FHE eliminates this barrier by enabling banks to outsource computationally intensive tasks such as fraud detection algorithms, credit risk modeling, portfolio optimization, and AI model training to external providers or cloud platforms without ever exposing the actual customer data. The cloud provider processes encrypted information and returns encrypted results, never gaining access to sensitive details. This capability also facilitates secure data sharing between financial institutions for anti-money laundering efforts or consortium-based risk assessment while maintaining each institution's data sovereignty.
Research implementations have demonstrated FHE's viability in financial contexts, though computational overhead remains a practical consideration. Early deployments focus on specific high-value use cases where the privacy guarantees justify the additional processing time, such as regulatory compliance reporting, secure multi-party credit scoring, and privacy-preserving fraud detection across institutional boundaries. As hardware acceleration techniques and algorithmic optimizations continue to mature, industry analysts note that FHE is transitioning from theoretical possibility to practical tool. The technology aligns with broader trends toward privacy-enhancing technologies in finance, including zero-knowledge proofs and secure enclaves, collectively enabling a future where financial institutions can harness the full power of cloud computing and collaborative analytics without compromising the fundamental privacy guarantees that customers and regulators demand.
Related Organizations
Open-source cryptography company building state-of-the-art Fully Homomorphic Encryption (FHE) tools and libraries.
Provides a platform for secure data collaboration using Homomorphic Encryption.
Pioneered the use of Homomorphic Encryption for 'Data in Use' security, allowing secure search over encrypted data.
Secret Computing company using Multi-Party Computation and FHE for privacy-preserving analytics.
Developing specialized hardware (accelerators) designed to handle the massive computational load of Fully Homomorphic Encryption.
A cybersecurity company providing fully encrypted data-in-use solutions.
European deep tech startup providing a platform for encryption-in-use based on FHE and MPC.
Through Copilot and the 'Recall' feature in Windows, Microsoft is integrating persistent memory and agentic capabilities directly into the operating system.
Developing optical computing hardware to accelerate FHE operations.











