Trusted Execution Environments
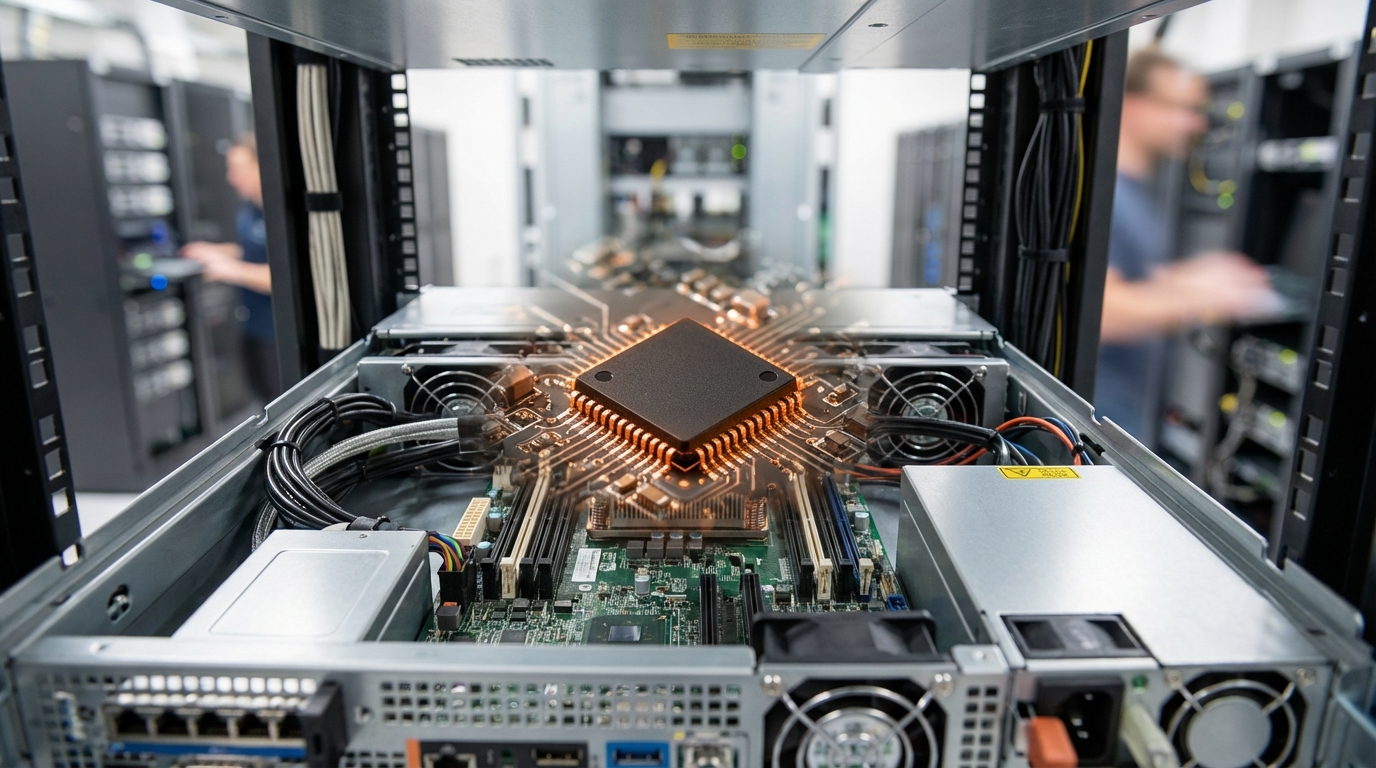
Trusted Execution Environments (TEEs) represent a fundamental shift in how processors handle sensitive data and operations. At the hardware level, TEEs create isolated execution spaces within a processor's architecture, using dedicated security mechanisms to ensure that code and data running inside these protected zones remain confidential and tamper-proof, even if the main operating system or other applications are compromised. This isolation is achieved through a combination of hardware-enforced memory encryption, secure boot processes, and attestation mechanisms that verify the integrity of the execution environment. Modern processor architectures from major manufacturers incorporate TEE capabilities through various implementations, each providing cryptographic guarantees that sensitive operations occur in a verifiable, protected context. The technology operates by partitioning the processor's resources into a "normal world" for standard applications and a "secure world" for sensitive operations, with strictly controlled interfaces between these domains that prevent unauthorized access or data leakage.
The critical problem TEEs address is the fundamental vulnerability of traditional computing systems, where a single breach in the operating system or hypervisor can expose all data and operations running on that machine. This vulnerability has become particularly acute in identity verification and authentication systems, where biometric data, cryptographic keys, and personal credentials must be processed and stored with absolute security guarantees. TEEs solve this by ensuring that even administrators with root access to a system cannot inspect or manipulate the data being processed within the secure enclave. This capability has proven essential for mobile payment systems, where financial credentials must be protected during transactions, and for biometric authentication, where fingerprint or facial recognition data requires processing in an environment immune to malware or system-level attacks. The extension of TEE principles to cloud computing through Confidential Computing initiatives addresses the longstanding challenge of processing sensitive data in shared infrastructure, enabling organizations to leverage cloud resources without exposing confidential information to cloud providers or other tenants.
Current adoption of TEE technology spans from billions of mobile devices using secure enclaves for payment authentication and device unlocking to enterprise deployments protecting cryptographic operations and sensitive workloads. Financial institutions increasingly rely on TEEs to secure transaction processing and key management, while healthcare organizations use them to enable privacy-preserving analytics on patient data without exposing individual records. The technology has become foundational for zero-trust security architectures, where verification of identity and authorization must occur in demonstrably secure environments. Looking forward, the convergence of TEEs with emerging privacy-enhancing technologies suggests a future where sensitive computations can be distributed across untrusted infrastructure while maintaining cryptographic proof of security. As regulatory frameworks increasingly mandate stronger protections for personal data and digital identities, TEEs are evolving from a specialized security feature into a standard requirement for any system handling authentication, verification, or sensitive personal information, fundamentally reshaping how trust is established in digital systems.
Related Organizations
Develops silicon spin qubits using advanced 300mm wafer manufacturing processes.
Develops the RDNA architecture with Ray Accelerators, powering ray tracing on PC and current-gen consoles (PS5, Xbox Series X).
Provides a data security platform that decouples security from infrastructure using confidential computing enclaves.
The standard body responsible for the specifications of Secure Elements and Trusted Execution Environments (TEE).
Offers the AI Stack which includes tools for hardware-aware model efficiency and architecture search.
Software that enables applications to run in secure enclaves (AWS Nitro, Azure, etc.) without code modifications.
An open-source project for building customizable TEEs.
Blockchain platform integrating secure enclaves to enable privacy-preserving smart contracts.

Trusted Computing Group
United States · Consortium
A standards organization for hardware-based trust.
A coprocessor for blockchains offering off-chain compute.