WebAuthn & Passkeys
WebAuthn (Web Authentication) represents a fundamental shift in how users authenticate to online services, moving away from traditional password-based systems toward cryptographic key pairs. Developed by the World Wide Web Consortium (W3C) and the FIDO Alliance, this standard enables users to log in using biometric sensors, security keys, or device PINs instead of memorizing passwords. The technology operates through asymmetric cryptography: a private key remains securely stored on the user's device—within dedicated hardware security modules, Trusted Platform Modules (TPMs), or secure enclaves—while a corresponding public key is registered with the online service. During authentication, the service sends a challenge that can only be correctly signed by the private key, proving the user's identity without ever transmitting the secret itself. Passkeys extend this foundation by enabling credentials to be synchronized across a user's devices through encrypted cloud services, addressing the traditional concern that hardware-bound credentials could be lost if a device is damaged or replaced.
The authentication landscape has long been plagued by password-related vulnerabilities that impose significant costs on both organizations and users. Phishing attacks, which trick users into revealing credentials on fake websites, have proven remarkably effective even against sophisticated users. Credential stuffing attacks, where attackers use leaked password databases to gain unauthorized access across multiple services, exploit the widespread practice of password reuse. Traditional multi-factor authentication methods, while adding security layers, often introduce friction that degrades user experience and can still be circumvented through sophisticated phishing techniques. WebAuthn addresses these challenges at an architectural level: because credentials are cryptographically bound to specific domain names, a phishing site cannot trick users into authenticating, as the browser will refuse to use credentials registered for a different domain. This domain-binding property, combined with the elimination of shared secrets that could be stolen from service providers during data breaches, fundamentally changes the threat model for online authentication.
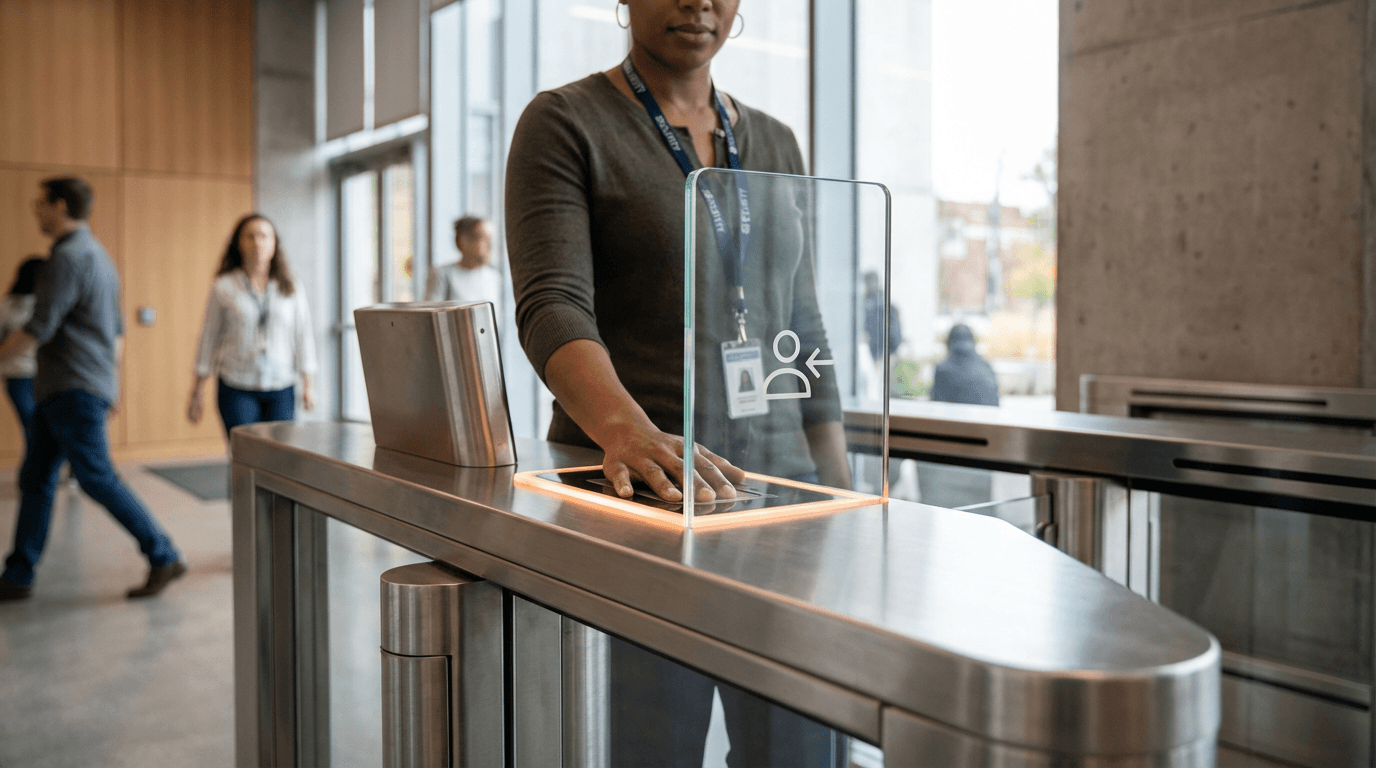
Major technology platforms have begun implementing passkey support across their ecosystems, with industry observers noting accelerating adoption among both consumer-facing services and enterprise identity providers. Financial institutions have shown particular interest given the technology's resistance to account takeover attacks, while healthcare organizations value its compliance-friendly approach to authentication security. Early deployments indicate that users appreciate the streamlined login experience, particularly when biometric authentication is available, though some adjustment period is required for those accustomed to password managers. The technology aligns with broader industry movements toward zero-trust security architectures and passwordless authentication frameworks. As regulatory pressure increases around data protection and as organizations seek to reduce help desk costs associated with password resets, WebAuthn and passkeys are positioned to become the dominant authentication method for web services. The transition represents not merely an incremental security improvement but a structural transformation in how digital identity verification operates, with implications for everything from consumer e-commerce to critical infrastructure access control.
Related Organizations
Open industry association developing standards for passwordless authentication (Passkeys) that keep biometric data local to the device.
Maker of the YubiKey and YubiHSM, a small form-factor hardware security module.
A password manager that includes 'Emergency Kit' features to facilitate digital access transfer to next of kin.
















