Dual-Use Monitoring Frameworks
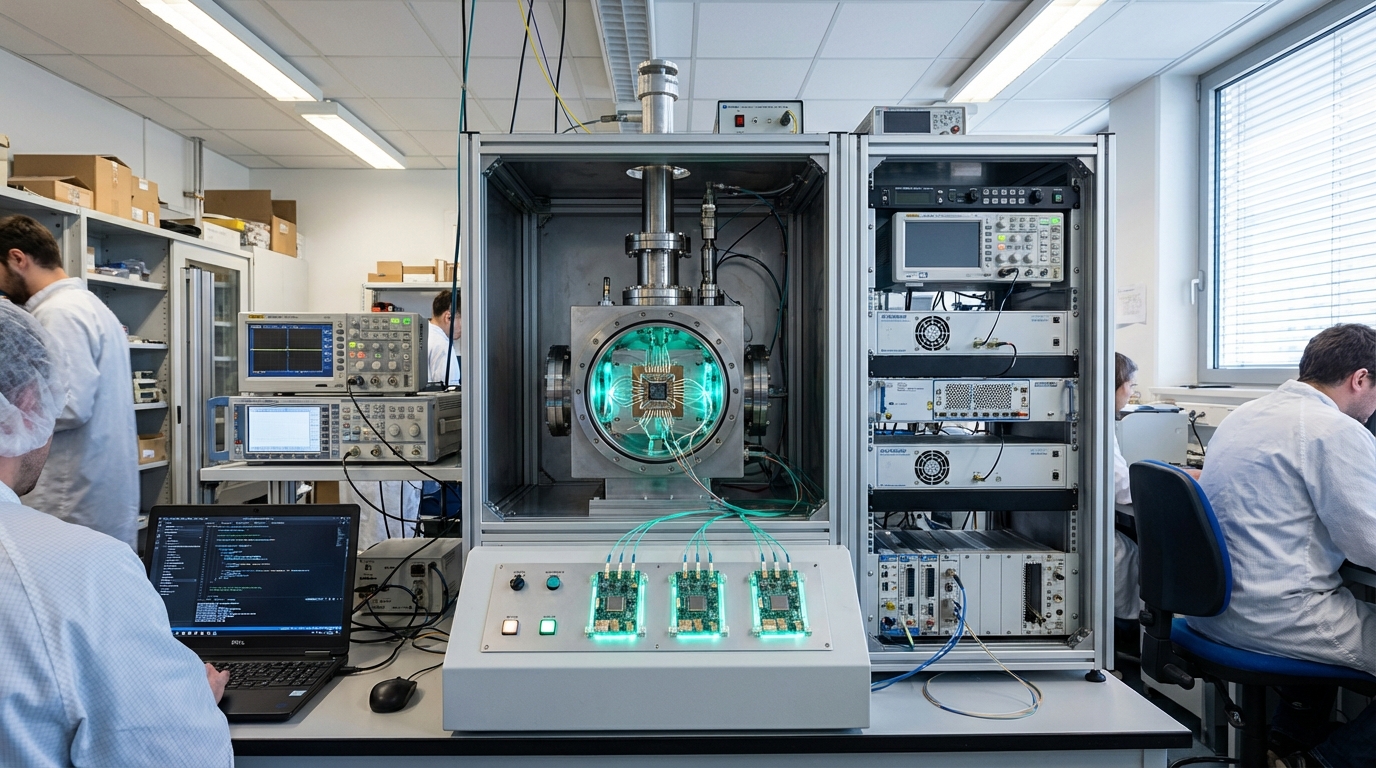
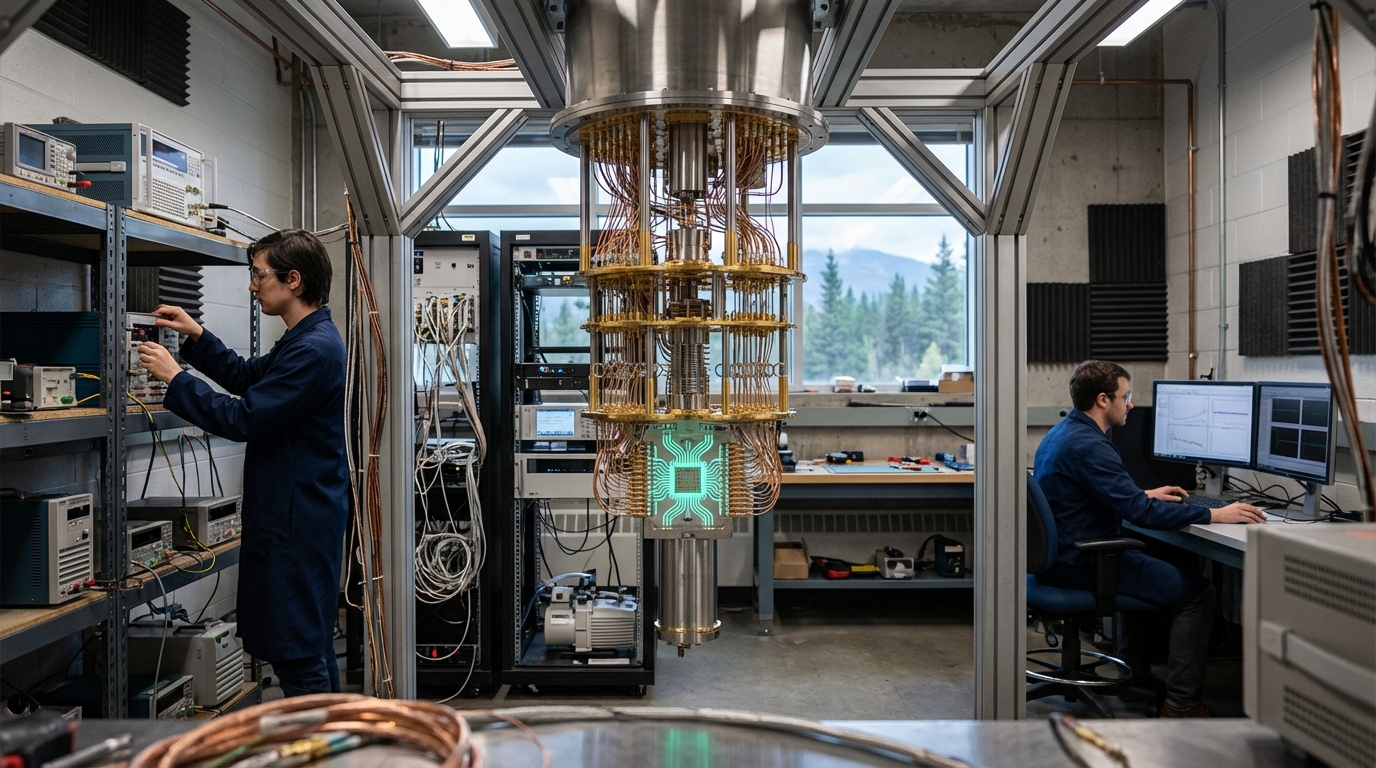
Dual-use monitoring frameworks are governance protocols to detect malicious quantum computations (quantum computing used for harmful purposes) without violating privacy (protecting legitimate users' information), where as quantum computers become capable of breaking encryption (cracking codes) or designing toxins (creating harmful chemicals), we face a 'dual-use' dilemma (technology that can be used for both good and harmful purposes). New governance frameworks (policies and systems) are exploring how to monitor cloud-based quantum jobs (computations run on cloud quantum computers) for malicious signatures (patterns indicating harmful use, like Shor's algorithm structure, which is used for breaking encryption) while preserving the intellectual property of legitimate users (protecting the privacy and secrets of people using quantum computers for legitimate purposes), creating a balance between security (preventing harmful use) and privacy (protecting legitimate users), addressing the challenge of preventing misuse of quantum computing while maintaining user privacy.
This innovation addresses the dual-use challenge of quantum computing, where powerful technology can be used for harm. By providing monitoring frameworks, these systems can detect misuse while protecting privacy. Policy researchers, security experts, and governance organizations are developing these frameworks.
The technology is important for ensuring responsible use of quantum computing, where monitoring could prevent harm. As quantum computing becomes more powerful, dual-use concerns become increasingly important. However, ensuring privacy, managing complexity, and achieving consensus remain challenges. The technology represents an important area of governance research, but requires careful design to balance competing objectives. Success could enable responsible quantum computing, but the frameworks must balance security and privacy. Dual-use monitoring is an active area of policy research with significant importance for the future of quantum computing.