Blind Quantum Computing Protocols
Blind quantum computing protocols are cryptographic protocols allowing clients (users) to compute on remote quantum servers (quantum computers accessed over a network) without revealing data (keeping information secret), where blind quantum computing enables a user with limited quantum capability (someone who doesn't have their own quantum computer) to delegate a computation (send a problem to be solved) to a powerful quantum server while keeping input (the data being processed), algorithm (the computation being performed), and output (the results) completely private (hidden from the server operator). This is crucial for cloud-based quantum computing privacy (protecting user data when using cloud quantum services), ensuring that users can use powerful quantum computers without revealing their data or what they're computing, addressing a critical privacy concern for cloud quantum computing.
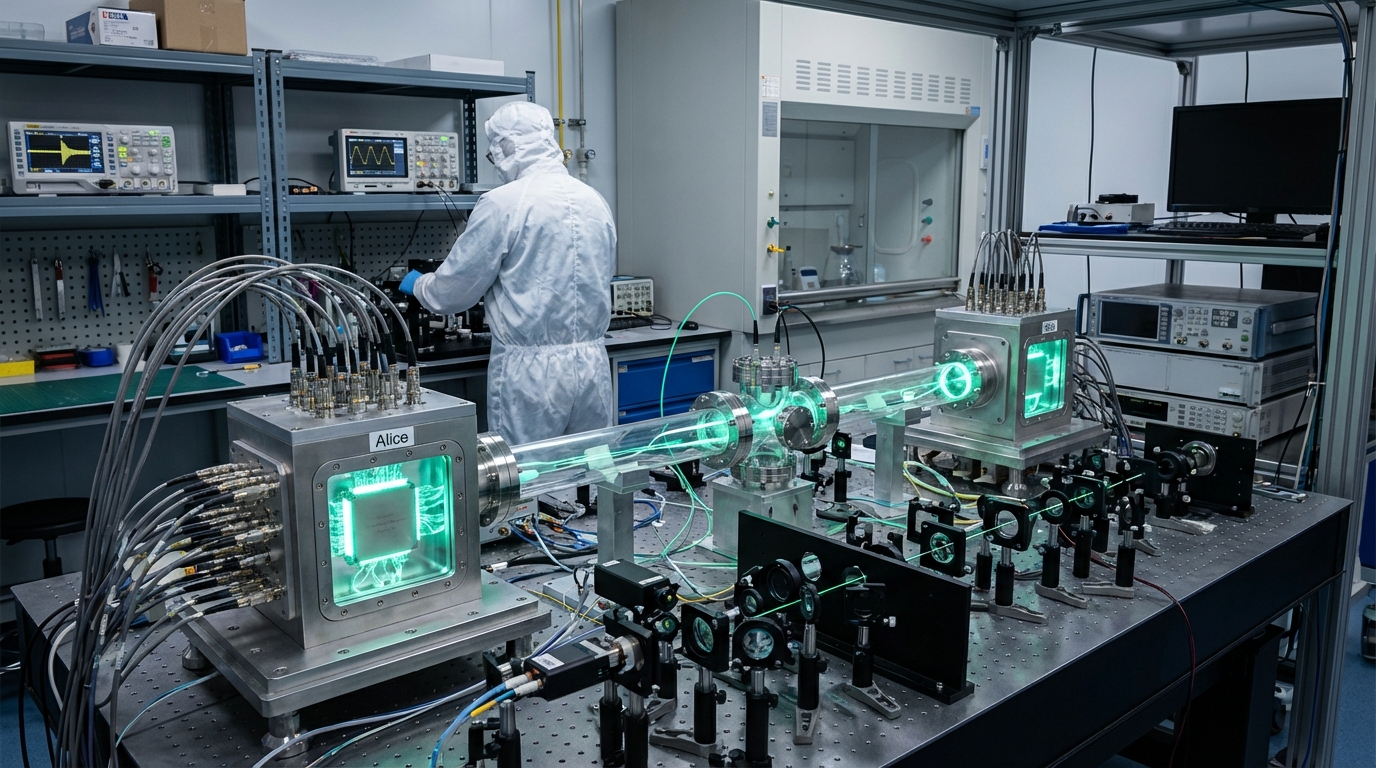
This innovation addresses the privacy challenge in cloud quantum computing, where users must trust service providers. By providing blind computing, these protocols protect user privacy. Research institutions are developing these protocols.
The technology is particularly significant for cloud quantum computing, where privacy is essential for adoption. As cloud quantum computing expands, blind computing becomes increasingly important. However, ensuring practicality, managing complexity, and achieving deployment remain challenges. The technology represents an important direction for quantum computing privacy, but requires continued development to achieve practical use. Success could enable private cloud quantum computing, but the technology must overcome practical challenges. Blind quantum computing is an active area of research with significant privacy advantages but practical challenges.