Quantum-Secure Verification Protocols
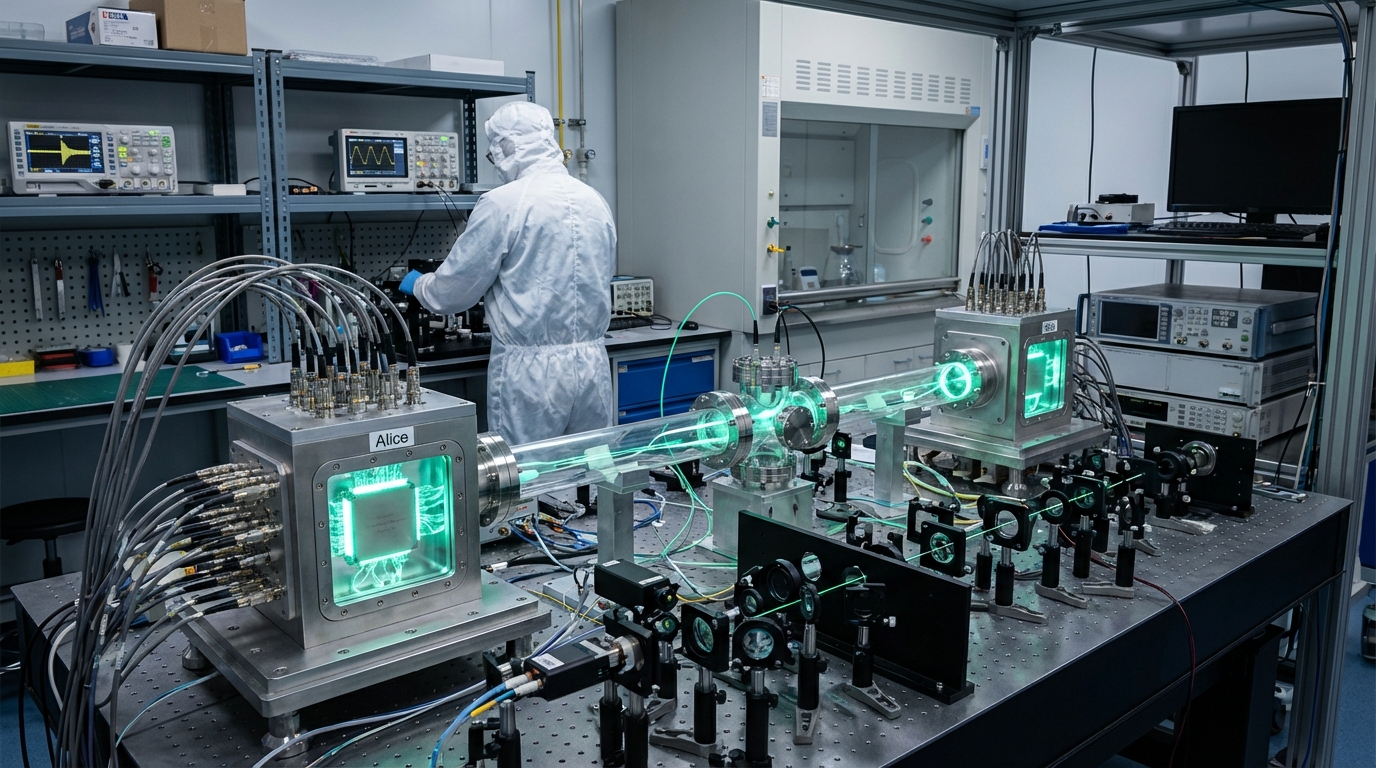
Quantum-secure verification protocols are security protocols for ensuring end-to-end integrity (verifying that data hasn't been tampered with) of quantum channels (quantum communication links) and repeaters (devices that extend the range of quantum communication), where for a future quantum internet (a network of quantum computers connected via quantum communication), we need protocols that verify entanglement has been distributed correctly (confirming that quantum entanglement was created and shared properly) across repeaters without being intercepted (ensuring that no one tampered with the quantum states), making these protocols essential for building a trusted quantum network infrastructure (quantum networks that can be relied upon for secure communication), ensuring that quantum networks provide the security guarantees they promise by detecting any tampering or interception.
This innovation addresses the need to verify quantum network integrity, where tampering could break security. By providing verification protocols, these systems ensure network security. Research institutions are developing these protocols.
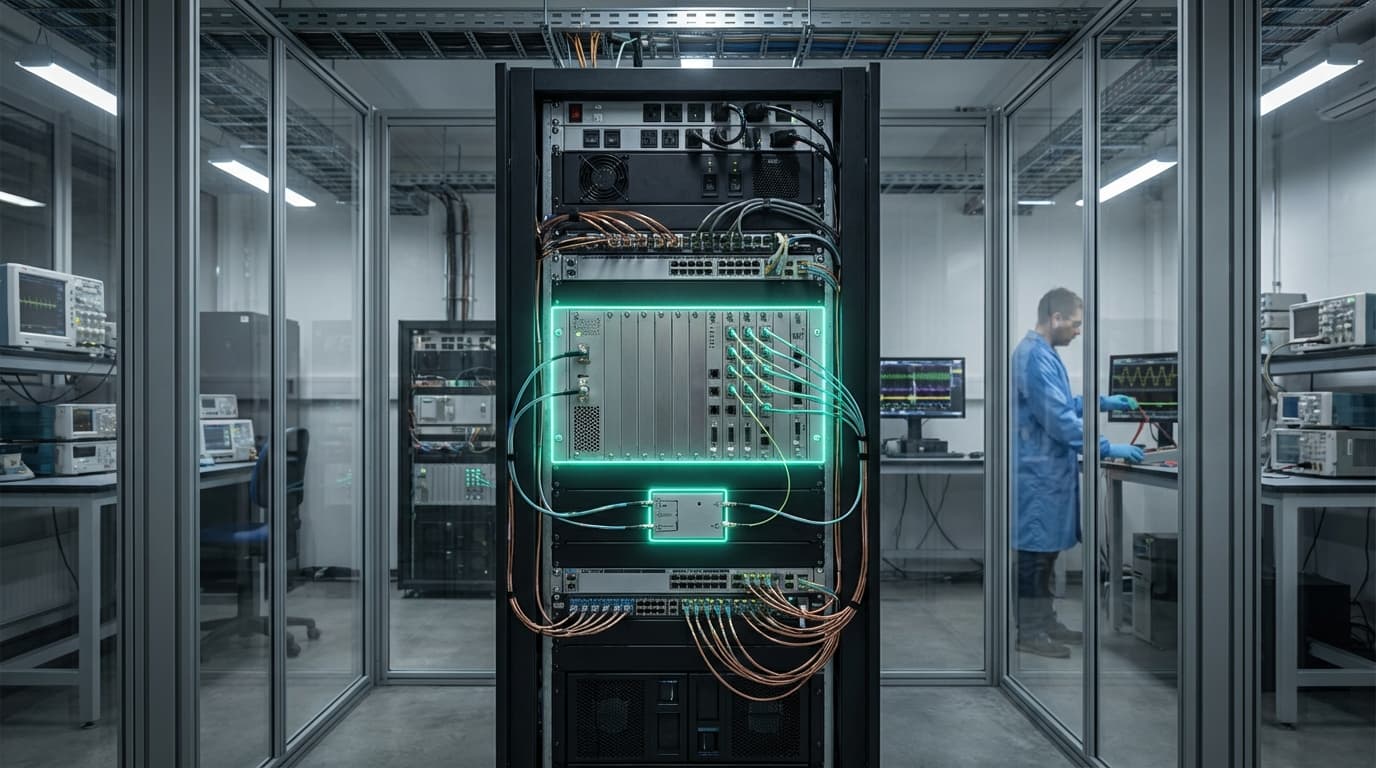
The technology is essential for building trusted quantum networks, where verification is necessary for security. As quantum networks expand, verification becomes increasingly important. However, ensuring effectiveness, managing complexity, and achieving practical deployment remain challenges. The technology represents important infrastructure for quantum networks, but requires continued development to achieve practical use. Success could enable trusted quantum networks, but the technology must overcome practical challenges. Quantum-secure verification is an active area of research with significant importance for quantum networks.