Cyber-Physical Security for Critical Logistics Infrastructure
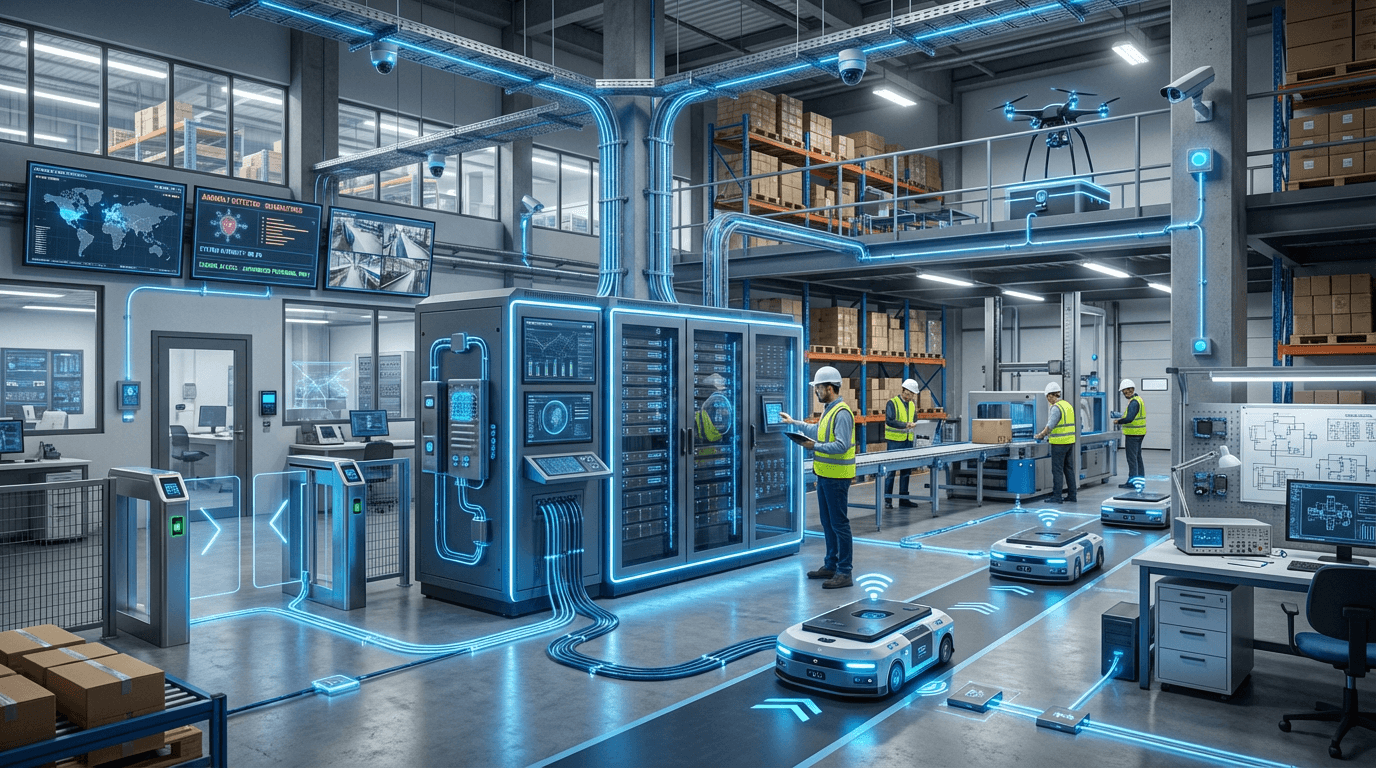
The convergence of digital networks and physical infrastructure in modern logistics has created unprecedented vulnerabilities where cyberattacks can trigger tangible, real-world consequences. Cyber-physical security represents a holistic approach to protecting these interconnected systems, recognizing that traditional cybersecurity measures alone are insufficient when digital breaches can directly manipulate physical operations. At its technical core, these frameworks integrate multiple layers of defense: network intrusion detection systems that monitor data flows for suspicious patterns, anomaly detection algorithms that identify deviations from normal operational parameters, physical access controls that restrict unauthorized entry to critical facilities, and real-time monitoring systems that correlate digital and physical events. The architecture typically employs a defense-in-depth strategy, where redundant security measures create multiple barriers against potential attackers. Advanced implementations incorporate machine learning models trained to recognize both known attack signatures and novel threat patterns, while secure communication protocols ensure that control signals between digital systems and physical actuators cannot be intercepted or manipulated.
The logistics industry faces unique security challenges due to its reliance on interconnected systems spanning vast geographic areas and multiple organizational boundaries. Port automation systems, warehouse robotics, autonomous delivery vehicles, and supply chain management platforms all present potential attack surfaces where malicious actors could disrupt operations, steal valuable cargo, or cause physical damage. Research suggests that coordinated attacks targeting both cyber and physical dimensions could paralyze critical supply chains, with cascading effects throughout the economy. Cyber-physical security frameworks address these vulnerabilities by creating unified visibility across digital and physical domains, enabling security teams to detect sophisticated attacks that might exploit the seams between these traditionally separate realms. This integrated approach also supports compliance with emerging regulatory requirements for critical infrastructure protection, while enabling logistics operators to maintain the operational efficiency that modern just-in-time supply chains demand.
Early deployments of comprehensive cyber-physical security systems are appearing in high-value logistics environments such as major container ports, pharmaceutical distribution centers, and defense supply chains. These implementations demonstrate the practical value of unified security architectures, where automated systems can respond to detected threats by simultaneously isolating compromised network segments and triggering physical lockdown procedures. Industry analysts note growing investment in security operations centers specifically designed for logistics environments, where specialists monitor both digital network traffic and physical sensor data from surveillance systems, access controls, and operational equipment. As supply chains become increasingly automated and interconnected, the adoption of robust cyber-physical security frameworks will likely transition from a competitive advantage to a fundamental operational requirement, particularly as insurance providers and regulatory bodies establish stricter standards for protecting critical logistics infrastructure against evolving threats.
Related Organizations
Specializes in securing the Extended Internet of Things (XIoT), bridging the gap between IT, OT, and IoT security.
Provides early warning systems for cyber attacks on maritime and critical national infrastructure assets.
Provides industrial cybersecurity platform for asset identification, threat detection, and response in OT environments.
Delivers OT and IoT visibility and security, using AI to detect anomalies in industrial control networks.
Delivers ship-wide cybersecurity protection, securing IT and OT networks on vessels.

Armis
United States · Startup
Asset intelligence platform that discovers and secures managed, unmanaged, and IoT/OT devices.
Develops unidirectional security gateways (data diodes) that physically prevent cyberattacks from entering industrial control networks.
Provides asset risk management focused on the physical layer (Layer 1), detecting rogue hardware devices.











