Verifiable Credentials & Decentralized Identifiers (VC/DID)
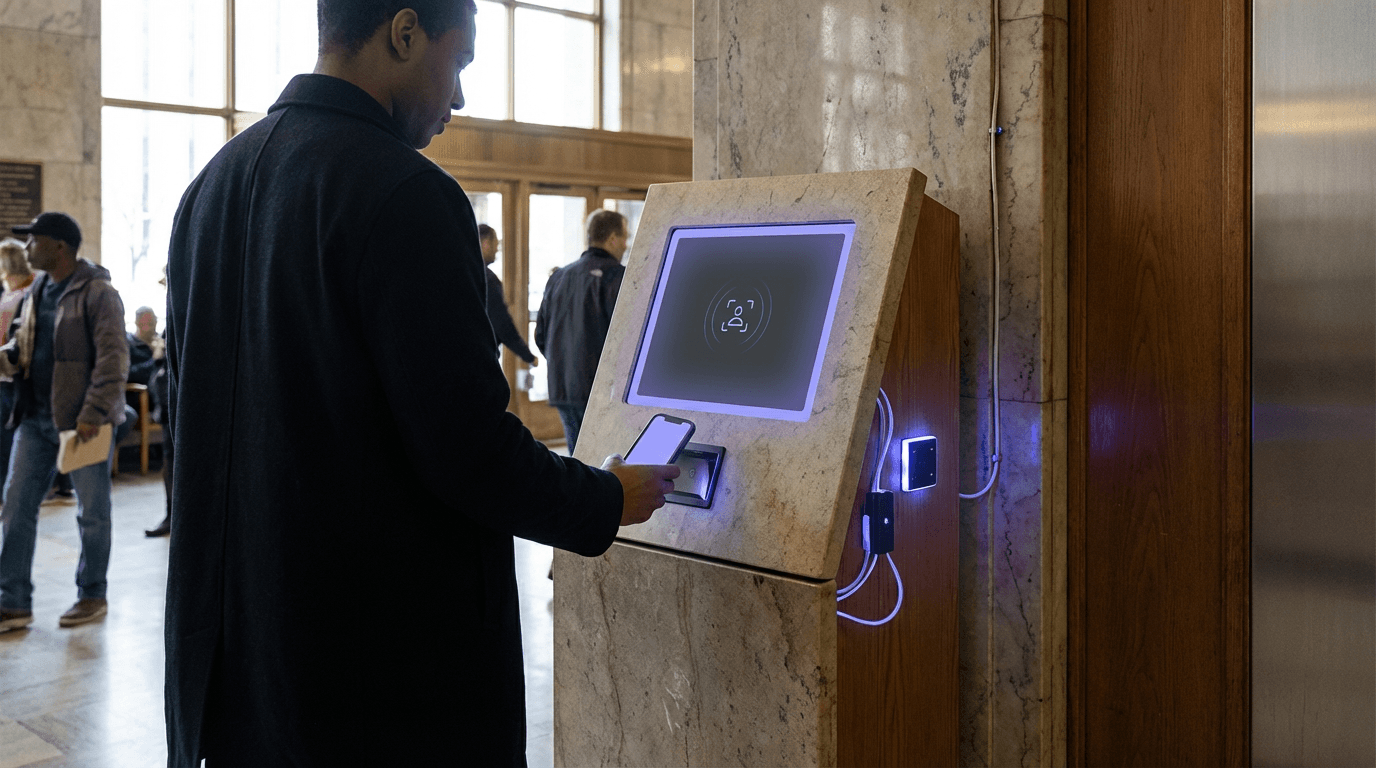
Verifiable Credentials and Decentralized Identifiers represent a fundamental shift in how individuals prove their identity and qualifications in digital civic systems. At their core, these technologies enable people to hold cryptographically secure credentials—such as proof of residency, professional licenses, voting eligibility, or benefit entitlements—in digital wallets they control directly, rather than relying on centralized databases managed by government agencies or third-party providers. The system operates through two complementary standards: Decentralized Identifiers (DIDs), which are unique identifiers that individuals or organizations control without requiring a central registry, and Verifiable Credentials (VCs), which are tamper-evident digital documents that can be cryptographically verified without contacting the issuing authority. When a citizen needs to prove eligibility for a service, they present only the specific credential attributes required—for instance, confirming they are over 18 without revealing their exact birthdate—through a process called selective disclosure. The verification happens through cryptographic validation rather than real-time database queries, meaning the issuing agency doesn't need to be online or even aware that verification is occurring, fundamentally decoupling identity assertion from centralized surveillance.
The traditional model of civic identity creates significant challenges for both governments and citizens. Centralized identity databases present attractive targets for cyberattacks and data breaches, exposing sensitive personal information of millions of residents simultaneously. Citizens must repeatedly submit the same documents to different agencies, creating administrative burden and increasing the surface area for identity theft. Furthermore, many civic services require real-time access to government databases for verification, creating single points of failure and raising privacy concerns as agencies track every instance of credential checking. Verifiable Credentials address these problems by shifting control to individuals while maintaining the cryptographic integrity that agencies require. This approach enables new models of civic service delivery where private vendors can verify eligibility for government programs without accessing centralized databases or learning unnecessary personal details. It also supports cross-jurisdictional recognition of credentials, allowing a professional license issued in one city to be verifiable in another without complex reciprocity agreements or database integrations.
Several governments and civic organizations have begun piloting VC/DID systems for specific use cases, with early implementations focusing on educational credentials, professional licenses, and proof of residency for accessing local services. Research from digital identity initiatives suggests that these systems can significantly reduce administrative overhead while improving privacy protections for citizens. The technology aligns with broader trends toward self-sovereign identity, where individuals maintain greater control over their personal data, and zero-knowledge proofs, which allow verification of claims without revealing underlying information. As concerns about data privacy, surveillance, and centralized control intensify in democratic societies, VC/DID systems offer a pathway toward civic infrastructure that preserves both security and individual autonomy. The challenge ahead lies in establishing interoperability standards across jurisdictions, ensuring accessibility for populations with limited digital literacy, and building public trust in systems that fundamentally reimagine the relationship between citizens and their credentials.
Related Organizations
An engineering-driven organization developing the technical specifications and standards for decentralized identity.
The international standards organization for the Web, responsible for the Decentralized Identifiers (DID) and Verifiable Credentials (VC) recommendations.
The executive branch of the EU, responsible for the AI Act.
A provincial government that launched the OrgBook BC, a verifiable organizations network based on Hyperledger Indy.
Provides a platform for creating and verifying digital credentials, contributing heavily to JSON-LD and BBS+ signature standards.
Develops decentralized identity software, including tools for verifiable credentials and ZK-based authentication.
A company specializing in decentralized identity software, maintaining the Universal Resolver for DIDs.
Hosts Hyperledger Indy and Aries, the open-source frameworks that power a significant portion of global SSI projects.
Formerly Polygon ID, providing Zero-Knowledge (ZK) identity infrastructure for verifiable credentials.
A company applying verifiable credentials and DIDs to supply chain security and trade documentation.
Provides a full stack for issuing and verifying decentralized identities and credentials.
Parent company of Avast, which acquired Evernym (the creator of Sovrin), consolidating key SSI technology.