Sybil-Resistance Mechanisms
Digital democracy platforms face a fundamental vulnerability: the ease with which malicious actors can create multiple fake identities to manipulate voting outcomes, distort public opinion, or unfairly claim resources. This attack vector, known as a Sybil attack, poses an existential threat to any system that relies on one-person-one-vote principles or fair resource distribution. Sybil-resistance mechanisms are technical and cryptographic solutions designed to ensure that each participant in a digital democratic system represents a unique, real human being. These systems employ various approaches, from biometric verification and social graph analysis to cryptographic proofs and stake-based validation. Some implementations, such as Proof of Humanity protocols, combine video verification with vouching systems where existing verified users attest to newcomers' authenticity. Others leverage the structure of social networks, analysing connection patterns to identify clusters of fake accounts that typically exhibit different relationship dynamics than genuine users. Blockchain-based approaches may require users to stake tokens or demonstrate computational work, raising the cost of creating multiple identities to economically prohibitive levels.
The challenge these mechanisms address extends beyond simple vote manipulation. In participatory budgeting systems, Sybil attacks could allow a single actor to claim multiple shares of public funds. In reputation-based governance, fake accounts can artificially inflate or suppress the standing of proposals or individuals. In quadratic voting systems, which give disproportionate weight to broad coalitions, Sybil attacks fundamentally undermine the mathematical principles that make such systems effective. Traditional digital platforms have relied on centralised identity verification, but this approach contradicts the decentralised ethos of many digital democracy initiatives and creates privacy concerns. Sybil-resistance mechanisms attempt to solve this tension by enabling identity uniqueness verification without requiring users to surrender personal data to central authorities. This balance between privacy preservation and identity assurance represents one of the core technical challenges in building trustworthy digital civic infrastructure.
Early implementations of these mechanisms are emerging across various digital governance experiments and decentralised autonomous organisations. Some blockchain governance platforms now require participants to complete multi-step verification processes before gaining voting rights, while others experiment with reputation systems that gradually grant influence based on sustained, authentic participation. Research in this domain continues to explore hybrid approaches that combine multiple verification methods to increase robustness against sophisticated attacks. The trajectory of these technologies will likely determine whether digital democracy can scale beyond small, trusted communities to encompass larger populations. As more civic functions move online and governments explore digital participation tools, the ability to reliably distinguish real citizens from manufactured personas becomes not just a technical requirement but a prerequisite for democratic legitimacy itself. The development of effective, privacy-preserving Sybil-resistance mechanisms may prove essential to realising the promise of more direct, participatory forms of governance in the digital age.
Related Organizations
A platform for funding and coordinating open source development.
A system combining social verification with video submission to create a Sybil-resistant registry of humans, linked to UBI.
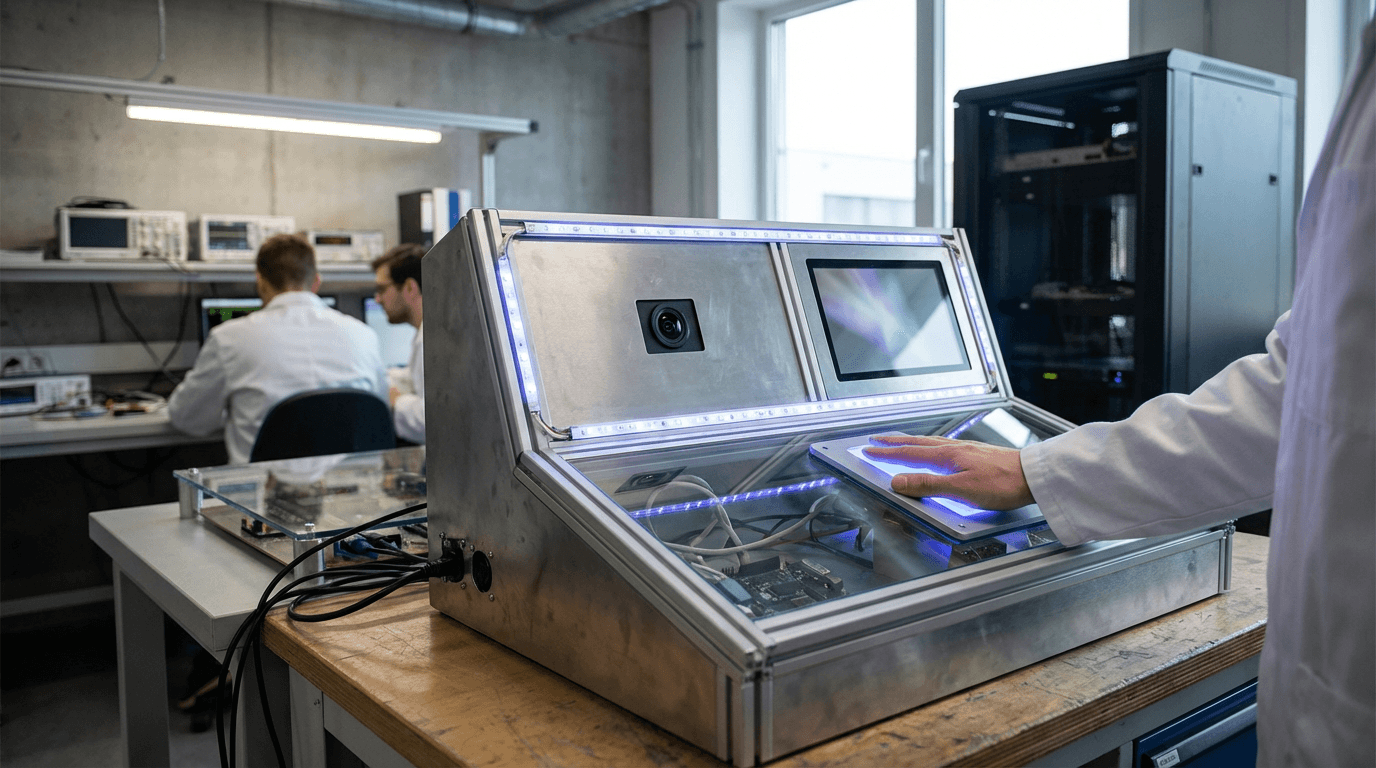
The developer behind Worldcoin and World ID, utilizing biometric iris scanning (The Orb) for Proof of Personhood.
A social identity network that allows people to prove they are unique humans without revealing personal data or paying fees.
Next-generation private access control based on Self-Sovereign Identity and zk-SNARKs.
Uses cryptographically secure biometric verification to link digital identities to physical humans without revealing the biometric data itself.
Long-standing identity verification company now focusing on Civic Pass, a tool for on-chain identity and access management.
A decentralized arbitration service for the disputes of the new economy, acting as a subjective oracle for governance decisions.
Develops decentralized identity software, including tools for verifiable credentials and ZK-based authentication.
The international standards organization for the Web, responsible for the Decentralized Identifiers (DID) and Verifiable Credentials (VC) recommendations.














