Surveillance, Privacy, and Civil Liberties
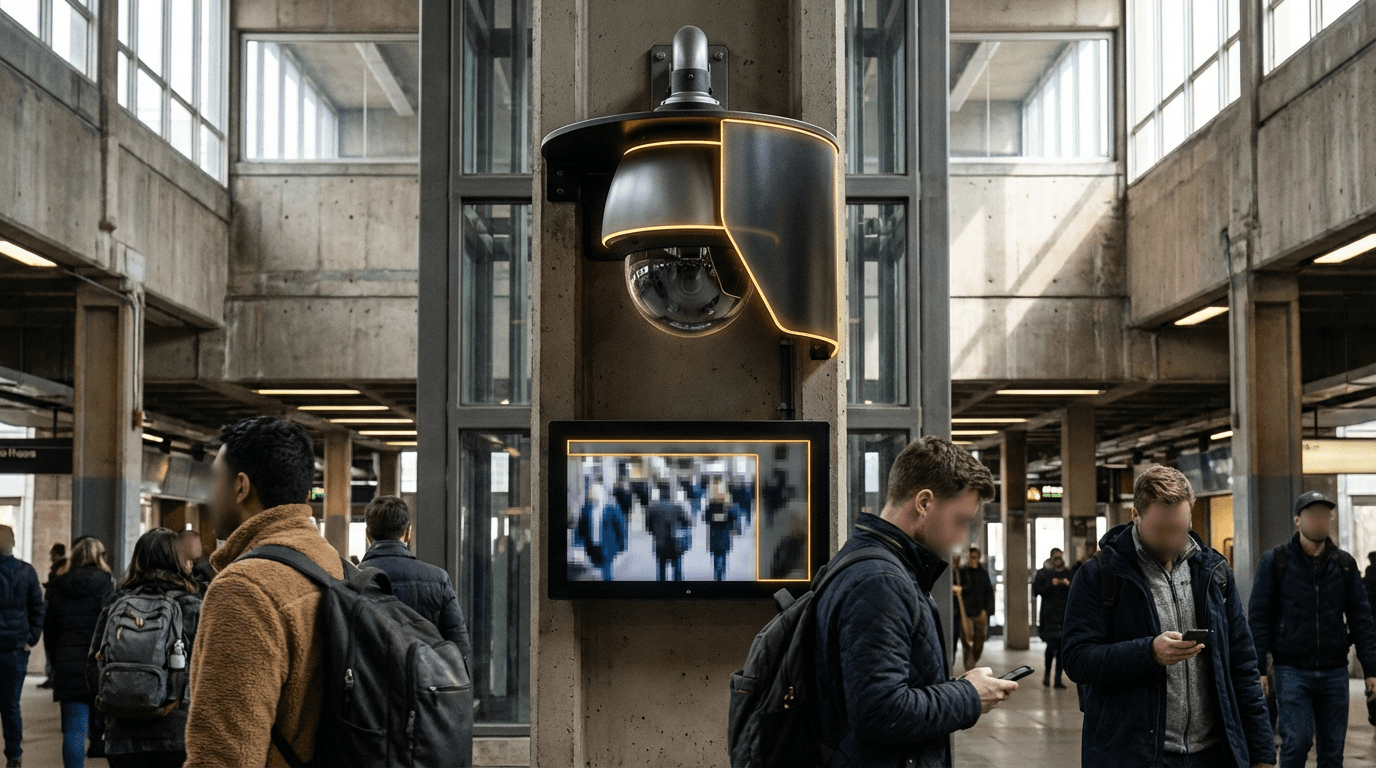
The proliferation of advanced surveillance technologies—ranging from facial recognition systems and biometric databases to real-time geolocation tracking and predictive analytics—has created an unprecedented capacity for persistent monitoring of civilian populations. While these technologies offer legitimate benefits for public safety and security operations, they simultaneously pose profound risks to fundamental civil liberties, including privacy, freedom of assembly, and protection against unreasonable search. The core challenge lies in establishing robust frameworks that enable security agencies and law enforcement to leverage these capabilities for legitimate purposes while preventing their misuse, overreach, or deployment in ways that disproportionately impact vulnerable communities. This involves developing technical safeguards, legal constraints, and oversight mechanisms that can adapt to rapidly evolving surveillance capabilities, from automated license plate readers and drone-based monitoring to sophisticated data fusion systems that aggregate information across multiple sources.
Effective governance of surveillance technologies requires a multi-layered approach that addresses both technical implementation and institutional accountability. This includes establishing clear legal standards for when and how biometric identification systems can be deployed, requiring judicial oversight for certain types of monitoring activities, and implementing technical measures such as data minimisation protocols, encryption requirements, and automated audit trails that document system access and usage. Research in this domain explores privacy-preserving alternatives to traditional surveillance methods, including differential privacy techniques that allow for aggregate analysis without exposing individual identities, federated learning approaches that keep sensitive data decentralised, and temporal limitations that automatically purge collected information after specified periods. Industry standards are emerging around transparency requirements, mandating that organisations disclose their surveillance capabilities and usage policies, while civil society organisations advocate for algorithmic accountability measures that allow independent auditing of automated decision-making systems for bias and discrimination.
Current implementations vary significantly across jurisdictions, with some regions adopting comprehensive frameworks like the European Union's General Data Protection Regulation (GDPR), which establishes strict consent requirements and data subject rights, while others pursue more permissive approaches. Cities worldwide are grappling with decisions about facial recognition deployment, with some implementing moratoriums or outright bans on government use of the technology, while others proceed with pilot programs subject to community oversight boards and regular impact assessments. The trajectory of this field increasingly points toward adaptive governance models that can respond to technological change through regular review processes, stakeholder engagement mechanisms that include affected communities in decision-making, and international cooperation on shared standards. As surveillance capabilities continue to advance through integration with artificial intelligence and ubiquitous sensor networks, the development of robust constraints becomes essential not only for protecting individual rights but also for maintaining public trust in security institutions and preventing the normalisation of authoritarian monitoring practices in democratic societies.
Related Organizations
Facial recognition company with a massive database of scraped images, used by law enforcement and private security.
Develops cyber intelligence tools like Pegasus, used by governments for mobile device surveillance.
Charity committed to fighting for the right to privacy across the world.
Deployed the PQXDH protocol, bringing post-quantum encryption to the initial key exchange for messaging and media sharing.
Maintains the Tor anonymity network, allowing users to browse the internet without being tracked.
Nonprofit legal organization defending civil rights.
Open-source cryptography company building state-of-the-art Fully Homomorphic Encryption (FHE) tools and libraries.
A civil liberties campaign group fighting against state surveillance and threats to privacy in the UK.
Provides a platform for secure data collaboration using Homomorphic Encryption.
Secret Computing company using Multi-Party Computation and FHE for privacy-preserving analytics.















