Device-Independent Quantum Cryptography
Device-independent quantum cryptography is an advanced form of cryptography that uses Bell test violations (tests that verify quantum entanglement, which can't be faked) to certify that a cryptographic key is secure, even if the quantum devices used to generate it were manufactured by an untrusted adversary (someone who might have tampered with the hardware), guaranteeing security based on physical laws (the laws of quantum mechanics) rather than trusting that hardware is secure. It represents the gold standard for future secure communications, where security doesn't depend on trusting hardware manufacturers, making it the most secure form of quantum cryptography because it provides security guarantees even when you can't trust the devices you're using, addressing a critical vulnerability in current quantum cryptography where compromised hardware could break security.
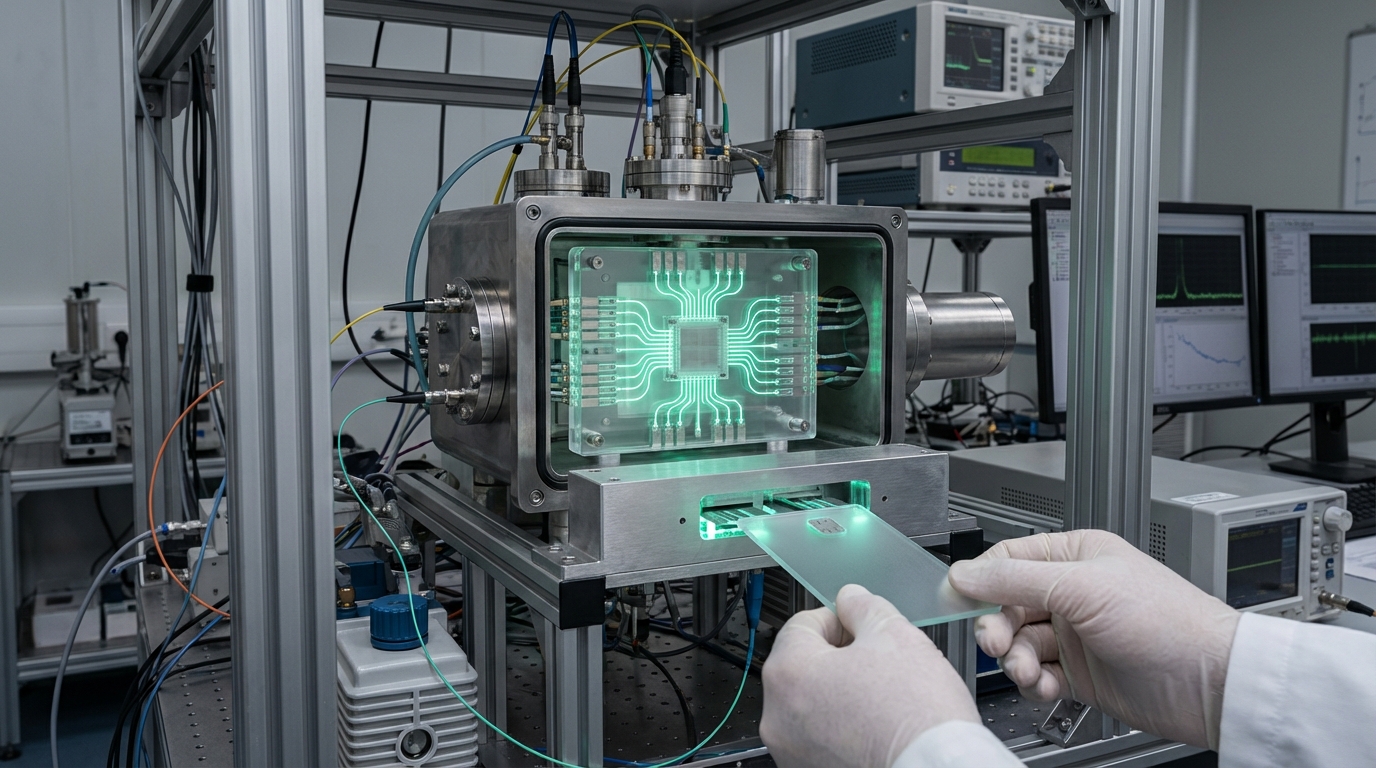
This innovation addresses the vulnerability of trusting hardware in quantum cryptography, where compromised devices could break security. By using Bell tests, these protocols provide security without trusting hardware. Research institutions are developing these protocols.
The technology is particularly significant for high-security applications, where device-independent security could be essential. As quantum cryptography expands, device-independent protocols become increasingly important. However, ensuring practicality, managing complexity, and achieving deployment remain challenges. The technology represents the ultimate in quantum cryptography security, but requires continued development to achieve practical use. Success could provide the most secure form of cryptography, but the technology must overcome practical challenges. Device-independent cryptography is an active area of research with significant security advantages but practical challenges.