Public Key Infrastructure & Certificate Transparency
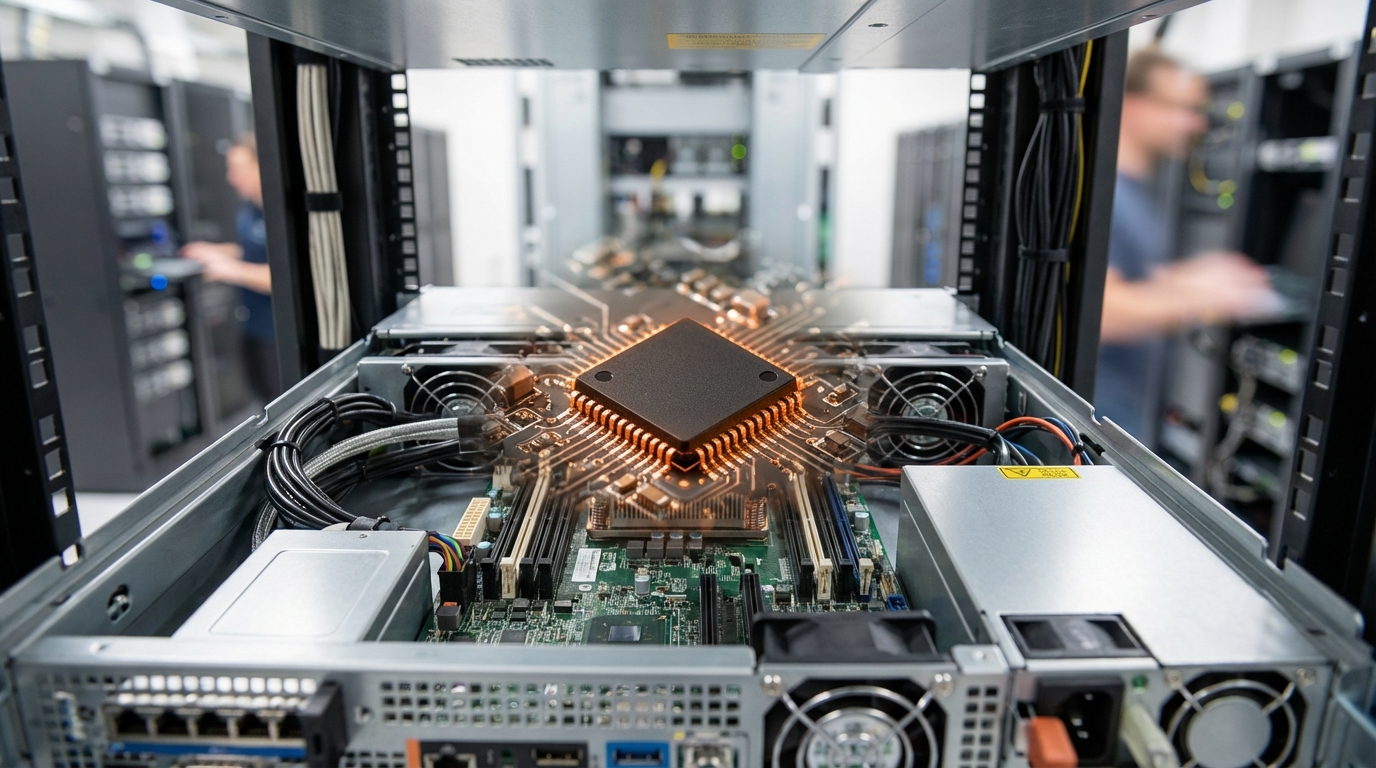
Public Key Infrastructure (PKI) serves as the foundational trust mechanism for secure digital communications, establishing cryptographic identities and enabling encrypted connections across the internet. At its core, PKI relies on digital certificates issued by Certificate Authorities (CAs)—trusted entities that verify the identity of websites, organizations, and individuals before binding their public keys to certificates. These certificates form hierarchical trust chains, where root CAs anchor the entire system and intermediate CAs issue end-entity certificates. However, traditional PKI faced a critical vulnerability: the system depended entirely on the trustworthiness of CAs, and a single compromised or negligent authority could issue fraudulent certificates undetected. Certificate Transparency addresses this weakness by introducing append-only, publicly auditable logs that record every certificate issuance. These cryptographic logs use Merkle tree structures to ensure that once a certificate is logged, it cannot be retroactively altered or removed. Browsers and other relying parties can verify that certificates appear in these public logs, while domain owners and security researchers can monitor the logs for unauthorized certificates issued for their domains.
The combination of PKI and Certificate Transparency solves several critical security challenges that have plagued internet communications. Before CT, malicious actors could obtain fraudulent certificates from compromised CAs and use them to intercept encrypted traffic, impersonate legitimate websites, or sign malicious code—all while remaining undetected for extended periods. Industry analysts note that several high-profile incidents involving mis-issued certificates exposed the fragility of pure CA-based trust models. Certificate Transparency transforms this opaque system into a transparent one, where any certificate issuance becomes a public event subject to scrutiny. This visibility enables rapid detection of mis-issuance, whether from compromised CAs, insider threats, or technical errors. Organizations can now monitor CT logs for unexpected certificates claiming their domain names, receiving alerts within hours rather than discovering breaches months later. The system also creates accountability, as CAs know their issuance practices are under constant public observation, incentivizing stricter validation procedures and operational security.
Major web browsers now require Certificate Transparency compliance for all publicly trusted certificates, making CT logs an essential component of internet infrastructure rather than an optional security enhancement. The technology extends beyond securing HTTPS connections to encompass code signing certificates, email encryption, and document authentication systems. Research suggests that CT has already prevented numerous potential security incidents by enabling early detection of suspicious certificate issuance patterns. Looking forward, the principles underlying Certificate Transparency are influencing broader discussions about transparency and auditability in digital trust systems. As organizations increasingly rely on digital certificates for identity verification, secure communications, and regulatory compliance, the combination of traditional PKI with transparent, publicly auditable logs represents a maturation of internet security architecture. This evolution reflects a broader industry trend toward zero-trust models and defense-in-depth strategies, where trust is continuously verified rather than implicitly assumed, positioning PKI and Certificate Transparency as enduring pillars of digital security infrastructure.
Related Organizations
The nonprofit behind Let's Encrypt, the free, automated, and open Certificate Authority.
Creators of CausalImpact, a package for causal inference using Bayesian structural time-series.
A leading commercial Certificate Authority and provider of automated certificate lifecycle management.
Specializes in machine identity management, automating the lifecycle of keys and certificates.
Provides PKI as-a-Service and crypto-agility solutions for enterprise and IoT security.
A web infrastructure and security company that has already enabled PQC support for a significant portion of the internet.
Developer of EJBCA, one of the most widely used open-source PKI software packages.
Offers automated certificate management and internal PKI for DevOps and modern infrastructure.
Provides certificate lifecycle management (CLM) and PKI automation.