Anonymous & Attribute-Based Credentials
Anonymous and Attribute-Based Credentials represent a fundamental shift in how digital identity verification can operate, addressing the growing tension between the need for trust in online interactions and the imperative to protect individual privacy. Traditional credential systems typically require users to present complete identity documents or profiles to verify a single attribute, creating unnecessary data exposure and enabling tracking across services. This technology solves this problem through cryptographic techniques that allow individuals to prove specific claims about themselves—such as age, professional qualifications, or membership status—without revealing any additional personal information. At the technical core are advanced cryptographic methods including zero-knowledge proofs, which enable one party to prove they possess certain information without revealing the information itself, and unlinkable presentation tokens that prevent different verifications from being correlated to track an individual's activities across platforms. The system works by issuing credentials that contain multiple attributes, each cryptographically signed by a trusted issuer, but structured in a way that allows the holder to selectively disclose only the relevant attributes for any given verification scenario.
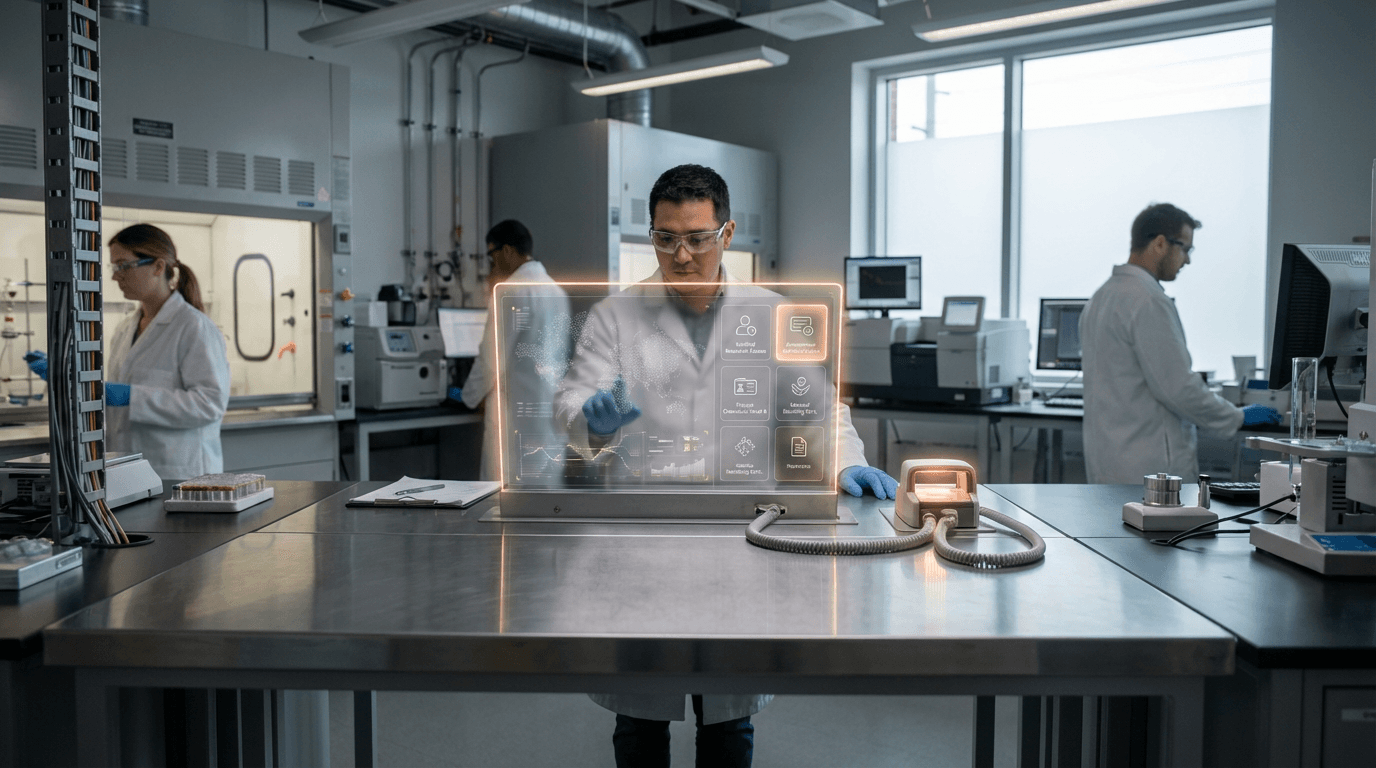
The implications for industries handling sensitive verification processes are profound. Financial services, healthcare providers, and government agencies currently face a difficult tradeoff between thorough identity verification and privacy protection, often collecting far more personal data than strictly necessary for a given transaction. This technology enables these organizations to verify only what they need to know—for instance, confirming that a customer meets age requirements for a service without learning their exact birthdate, or verifying professional credentials without accessing full employment history. This selective disclosure capability addresses regulatory pressures around data minimization principles embedded in frameworks like GDPR, while simultaneously reducing the liability and storage costs associated with maintaining extensive personal data repositories. For users, the unlinkability feature means that even if multiple service providers use the same credential system, they cannot collude to build comprehensive profiles of individual behavior, fundamentally disrupting the surveillance business models that have become prevalent in digital services.
Early implementations are emerging across sectors where privacy-preserving verification offers clear value propositions. Research institutions and technology consortia have developed prototype systems for educational credential verification, allowing graduates to prove their qualifications to employers without revealing grades or full academic records. In the public sector, some jurisdictions are exploring these systems for age verification in digital services, addressing concerns about minors accessing inappropriate content while avoiding the privacy risks of centralized age verification databases. The financial industry is investigating applications in anti-money laundering compliance, where institutions could verify that customers have been vetted by other banks without sharing detailed transaction histories. As digital identity systems become increasingly central to both online and offline interactions, anonymous and attribute-based credentials represent a crucial evolution toward what privacy advocates call "privacy-by-design" infrastructure. The technology aligns with broader movements toward user-centric identity models and zero-trust security architectures, suggesting that future verification systems will default to minimal disclosure rather than maximal data collection, fundamentally reshaping the relationship between identity, trust, and privacy in digital society.
Related Organizations
Long-standing leader in neuro-symbolic AI, combining neural networks with logical reasoning for enterprise applications.
Formerly Polygon ID, providing Zero-Knowledge (ZK) identity infrastructure for verifiable credentials.
Specialists in Self-Sovereign Identity (SSI) and decentralized identity wallets.
Develops enterprise-grade decentralized identity software and infrastructure.
Nonprofit consortium fostering open source innovation.
A research group within the Ethereum Foundation focused on zero-knowledge proofs and privacy.
A protocol for Proof of Personhood (World ID) using biometric verification to establish unique identity.
A layer-1 blockchain focused on compliant privacy and Zero-Knowledge KYC (zkKYC).
Contributor to the Internet Computer blockchain.