Cybersecurity Mesh
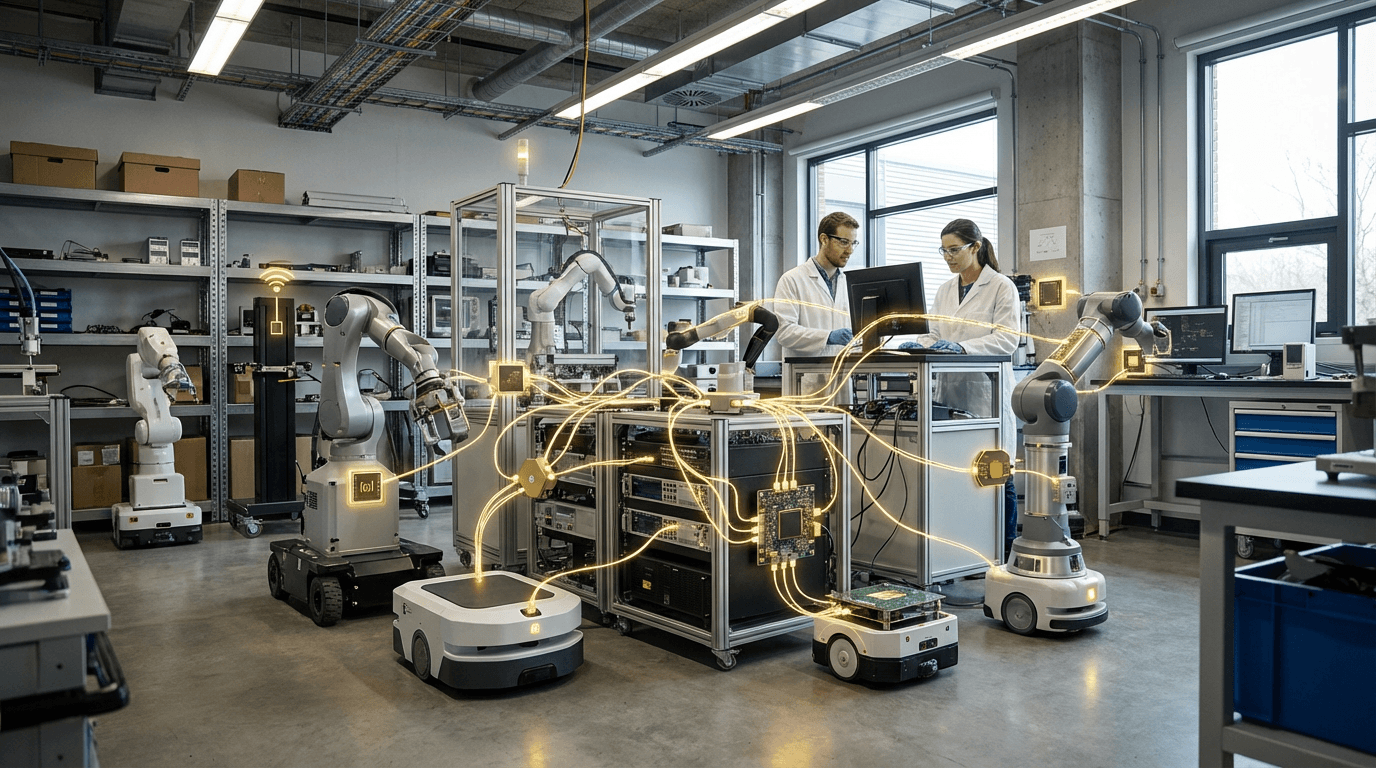
The rapid proliferation of connected devices in industrial environments has fundamentally challenged traditional perimeter-based security models. In the Fourth Industrial Revolution, where manufacturing facilities, supply chains, and critical infrastructure rely on thousands of interconnected sensors, controllers, and edge devices, the concept of a single, defensible network boundary has become obsolete. Cybersecurity Mesh addresses this challenge by implementing a distributed security architecture that treats each device, user, and data asset as its own protected entity. Rather than attempting to secure a monolithic network perimeter, this approach establishes individual security perimeters around each identity and endpoint, creating a flexible, scalable framework that can adapt to the dynamic nature of modern industrial operations. The architecture relies on distributed policy enforcement points that verify identity and assess risk at every access request, regardless of where the device or user is located. This shift from location-based to identity-based security is particularly crucial in environments where operational technology (OT) and information technology (IT) systems converge, and where legacy industrial equipment must coexist with modern IoT devices.
For industrial organizations grappling with the security implications of Industry 4.0 initiatives, Cybersecurity Mesh solves several critical problems. It enables secure connectivity across heterogeneous environments where devices may be manufactured by different vendors, operate on various protocols, and exist both on-premises and in cloud environments. This is especially valuable in smart manufacturing scenarios where production equipment, quality control systems, and supply chain partners must exchange data securely without creating vulnerability points. The modular nature of the architecture allows organizations to implement security controls incrementally, protecting new connected assets as they come online without requiring wholesale infrastructure replacement. This approach also addresses the challenge of securing remote and mobile access to industrial systems, a growing concern as maintenance technicians, engineers, and operators increasingly need to monitor and control equipment from distributed locations. By decoupling security services from the underlying infrastructure, Cybersecurity Mesh enables organizations to maintain consistent security policies even as their technology landscape evolves.
Early implementations in manufacturing and energy sectors demonstrate the practical value of this distributed approach. Industrial facilities are deploying mesh architectures to secure their expanding networks of programmable logic controllers, industrial robots, and predictive maintenance sensors while maintaining the real-time performance requirements critical to production operations. The technology aligns with broader industry movements toward zero-trust security models and edge computing, where processing and security decisions are pushed closer to where data is generated and consumed. As industrial environments become increasingly software-defined and cloud-connected, the ability to establish granular, identity-based security controls becomes not just advantageous but essential. Research suggests that organizations adopting mesh architectures can respond more rapidly to emerging threats and reduce the blast radius of potential security incidents by containing breaches at the individual asset level rather than allowing lateral movement across entire networks.
Related Organizations
Global leader in broad, integrated, and automated cybersecurity solutions.
A leader in cloud security that pioneered the Zero Trust Exchange platform, securing connections at the edge without backhauling traffic.
Specializes in securing the Extended Internet of Things (XIoT), bridging the gap between IT, OT, and IoT security.
Offers Cortex XSIAM, an autonomous security operations platform driven by AI.
Offers a cloud-native SASE platform that converges SD-WAN and network security into a global cloud service.
Delivers OT and IoT visibility and security, using AI to detect anomalies in industrial control networks.
Offers the 'Infinity' architecture, designed to provide consolidated security across networks, cloud, and mobile.
The Falcon platform utilizes AI for automated threat detection and real-time response.

HashiCorp
United States · Company
Provides identity-based security automation (Vault, Boundary, Consul) for dynamic infrastructure.
Offers Webex Hologram, an augmented reality meeting solution that projects photorealistic 3D holograms of participants into the room.











