Critical Infrastructure Failsafe Systems
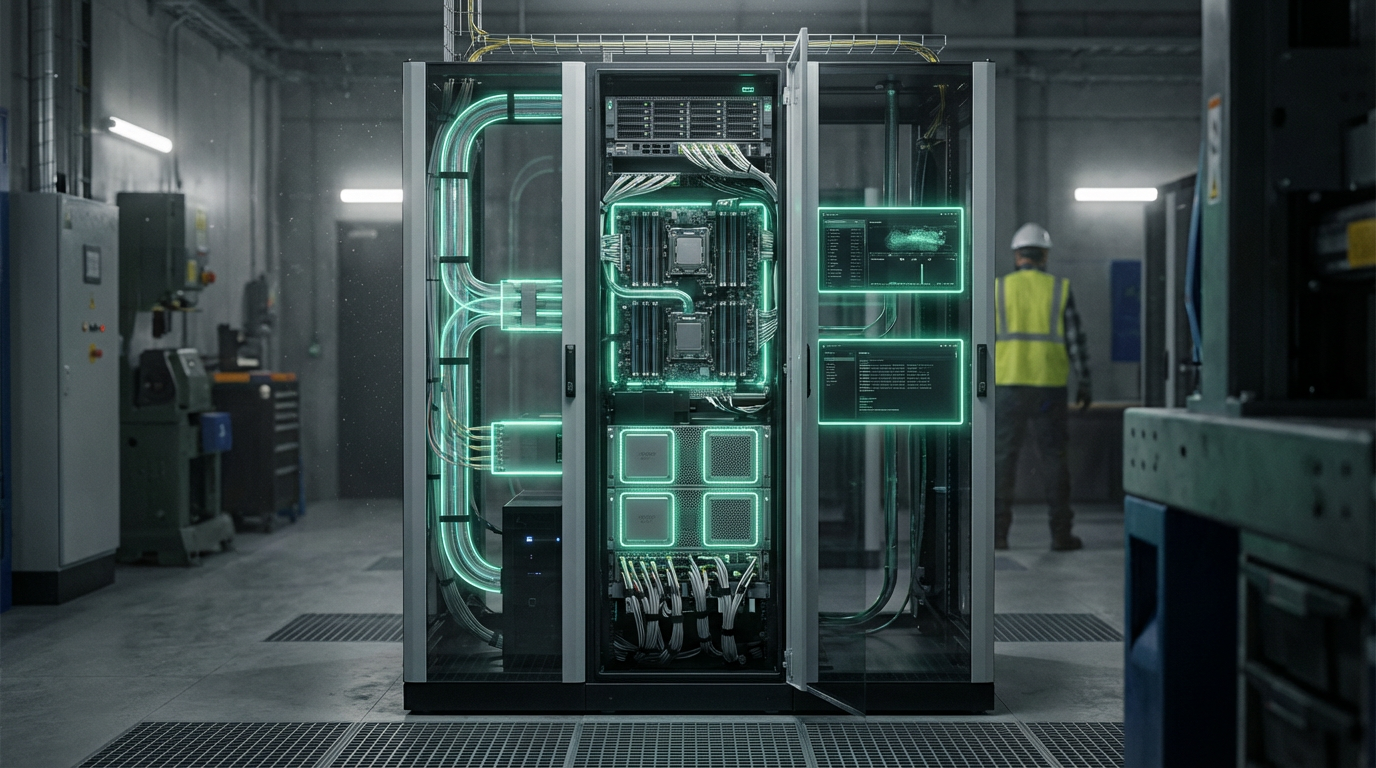
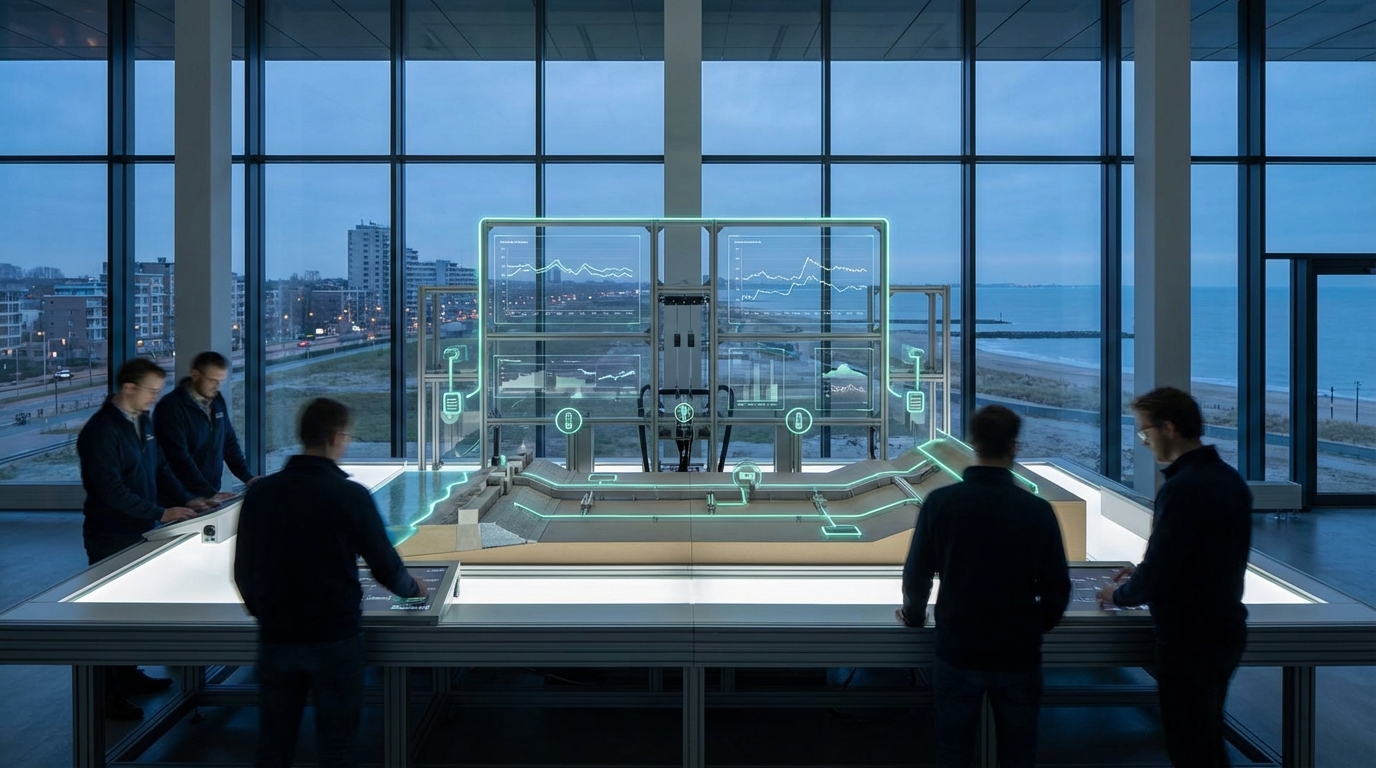
Critical infrastructure failsafe systems represent a fundamental shift in how essential services are designed to withstand both physical disruptions and sophisticated cyberattacks. These systems employ layered control architectures that separate critical functions into isolated domains, preventing a single point of failure from cascading across entire networks. At the technical core, they utilize redundant control loops, hardware-enforced safety boundaries, and embedded firmware designed with fail-safe defaults that automatically trigger when anomalous conditions are detected. Unlike traditional backup systems that simply duplicate functionality, failsafe architectures are built around the principle of graceful degradation—ensuring that when components fail or come under attack, the system transitions through predetermined safe states rather than experiencing sudden collapse. This involves real-time monitoring of system health, predefined fallback protocols, and the ability to partition networks to isolate compromised segments while maintaining essential operations in unaffected areas.
The growing sophistication of cyber threats targeting critical infrastructure has exposed a fundamental vulnerability in legacy systems: they were designed for reliability against physical failures, not adversarial attacks. Nation-state actors and criminal organizations have demonstrated the ability to penetrate industrial control systems, potentially causing widespread disruption to power grids, water treatment facilities, and transportation networks. Failsafe systems address this challenge by assuming breach scenarios from the outset, incorporating defense-in-depth strategies that limit the damage any single intrusion can cause. These architectures enable operators to maintain partial service delivery even when portions of the network are compromised, preventing the complete blackouts or service interruptions that could endanger public safety and economic stability. By building resilience into the fundamental design rather than adding security as an afterthought, these systems provide infrastructure operators with the ability to respond to attacks while keeping essential services running, buying critical time for incident response and recovery.
Early implementations of failsafe architectures are appearing in modernization projects for aging infrastructure, particularly in power distribution networks and water treatment facilities where the consequences of failure are most severe. Utilities are beginning to deploy segmented control systems that can island critical loads—maintaining power to hospitals and emergency services even when the broader grid experiences disruption. In transportation, failsafe principles are being integrated into railway signaling systems and traffic management platforms, ensuring that control failures default to safe states such as red signals or reduced speed limits. Industry analysts note that regulatory pressure, particularly in sectors deemed critical to national security, is accelerating adoption of these architectures. As geopolitical tensions intensify and the frequency of infrastructure-targeting cyberattacks increases, failsafe systems are transitioning from optional enhancements to essential requirements. The convergence of operational technology security, resilience engineering, and systems theory suggests that future critical infrastructure will be fundamentally architected around the assumption of partial failure, with graceful degradation becoming the baseline expectation rather than an aspirational goal.
Related Organizations
Provides industrial cybersecurity platform for asset identification, threat detection, and response in OT environments.

Idaho National Laboratory (INL)
United States · Research Lab
The US Department of Energy's lead laboratory for nuclear energy and critical infrastructure protection.
Designs and manufactures digital products and systems that protect power grids.
Specializes in securing the Extended Internet of Things (XIoT), bridging the gap between IT, OT, and IoT security.
Delivers OT and IoT visibility and security, using AI to detect anomalies in industrial control networks.
Global specialist in energy management and automation that integrates cybersecurity into its industrial hardware and software.
Provides HVDC Plus technology (VSC) and transformers for ultra-high-voltage transmission projects globally.
Develops unidirectional security gateways (data diodes) that physically prevent cyberattacks from entering industrial control networks.

OPSWAT
United States · Company
Critical infrastructure protection cybersecurity company.
Provides a blockchain-protected cybersecurity mesh for industrial operations and critical infrastructure.