Zero-Trust Edge Security
In the rapidly expanding landscape of edge computing and distributed networks, traditional perimeter-based security models have become increasingly inadequate. The fundamental challenge lies in the fact that edge devices—ranging from IoT sensors and industrial controllers to content delivery nodes and mobile base stations—are deployed in physically accessible, often uncontrolled environments far from centralized data centers. These devices face unique vulnerabilities: they can be tampered with, stolen, or compromised through physical access, yet they process sensitive data and make critical decisions in real-time. Zero-Trust Edge Security addresses this challenge by implementing a security paradigm that operates on the principle of "never trust, always verify," specifically adapted for the constraints and requirements of edge computing environments. Unlike traditional security models that assume everything inside a network perimeter is trustworthy, this approach treats every device, user, and network flow as potentially hostile, requiring continuous verification regardless of location or previous authentication status.
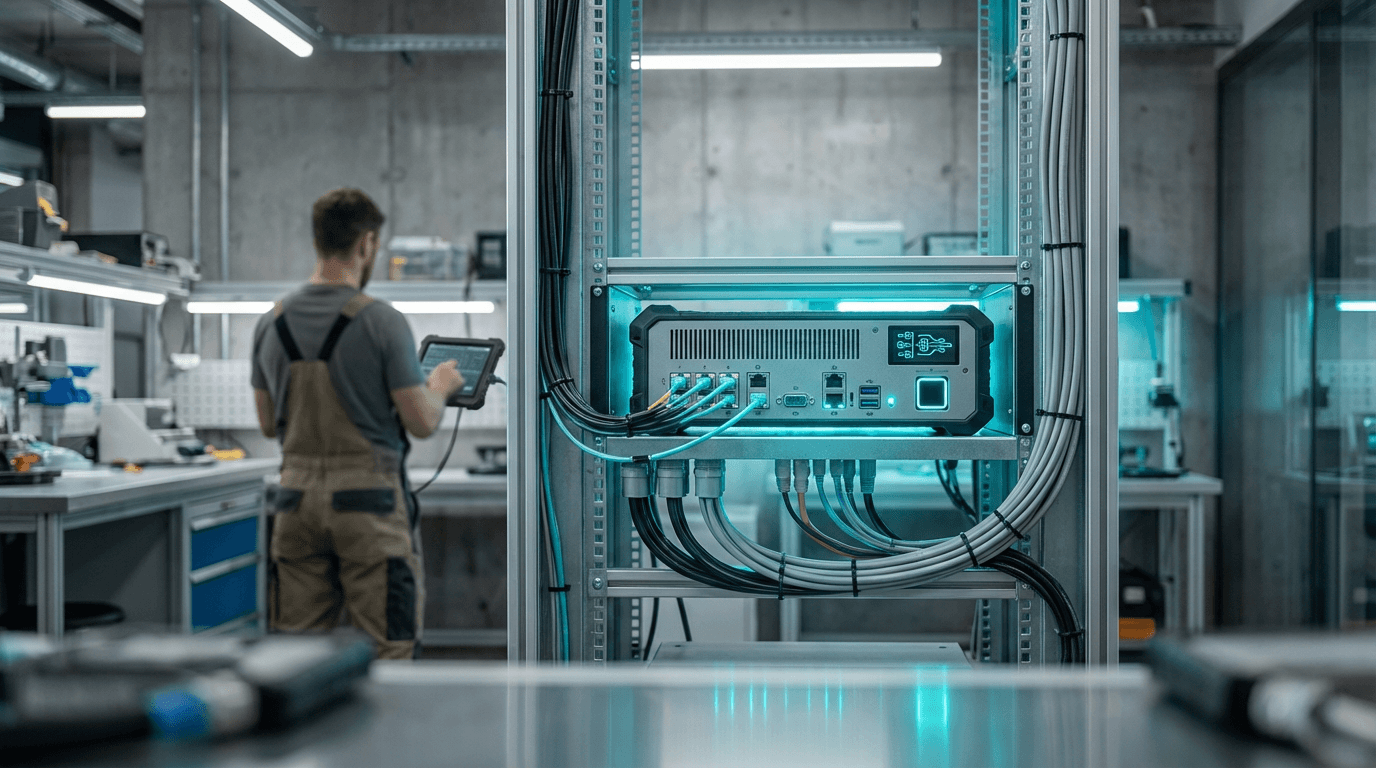
The architecture works by embedding security controls directly at the edge rather than relying on centralized security infrastructure. Each edge device or node implements its own authentication, authorization, and encryption mechanisms, verifying the identity and permissions of every request before granting access to resources or data. This verification process occurs continuously throughout a session, not just at initial connection, using techniques such as multi-factor authentication, device fingerprinting, and behavioral analysis to ensure that credentials haven't been compromised. The model enforces least-privilege access principles, meaning that users and devices receive only the minimum permissions necessary to complete their specific tasks, with access rights dynamically adjusted based on context such as device health, location, and threat intelligence. This distributed approach is particularly crucial for telecommunications infrastructure, where 5G and future 6G networks push computing capabilities to the network edge, creating thousands of potential attack surfaces that must be independently secured.
Industry deployments of Zero-Trust Edge Security are accelerating across sectors where edge computing is becoming critical infrastructure. Telecommunications providers are implementing these principles to secure their distributed radio access networks and mobile edge computing platforms, protecting both network operations and customer data processed at cell towers and base stations. Industrial facilities are adopting zero-trust frameworks for their operational technology environments, where edge devices control manufacturing processes and must be protected against both cyber and physical threats. Early implementations indicate that this approach significantly reduces the attack surface and limits the potential damage from breaches, as compromised devices remain isolated rather than providing attackers with broader network access. As edge computing continues to proliferate and regulatory frameworks increasingly mandate stronger security controls for distributed systems, Zero-Trust Edge Security is evolving from a best practice into a fundamental requirement for any organization deploying edge infrastructure at scale.
Related Organizations
The US federal agency leading the global competition to select and standardize post-quantum cryptographic algorithms.
Provides a blockchain-protected cybersecurity mesh for industrial operations and critical infrastructure.
A leader in cloud security that pioneered the Zero Trust Exchange platform, securing connections at the edge without backhauling traffic.
A web infrastructure and security company that has already enabled PQC support for a significant portion of the internet.
Provides a SASE platform that applies zero trust principles to web, cloud, and private application traffic at the network edge.
Offers a cloud-native SASE platform that converges SD-WAN and network security into a global cloud service.
An open-source project maintained by NetFoundry that provides a zero trust overlay network for embedding security directly into applications.
Provides a Unified SASE platform integrating SD-WAN and security at the edge.

Twingate
United States · Startup
Offers a modern Zero Trust Network Access (ZTNA) solution designed to replace corporate VPNs.









