Network Sovereignty & Cross-Border Data Control
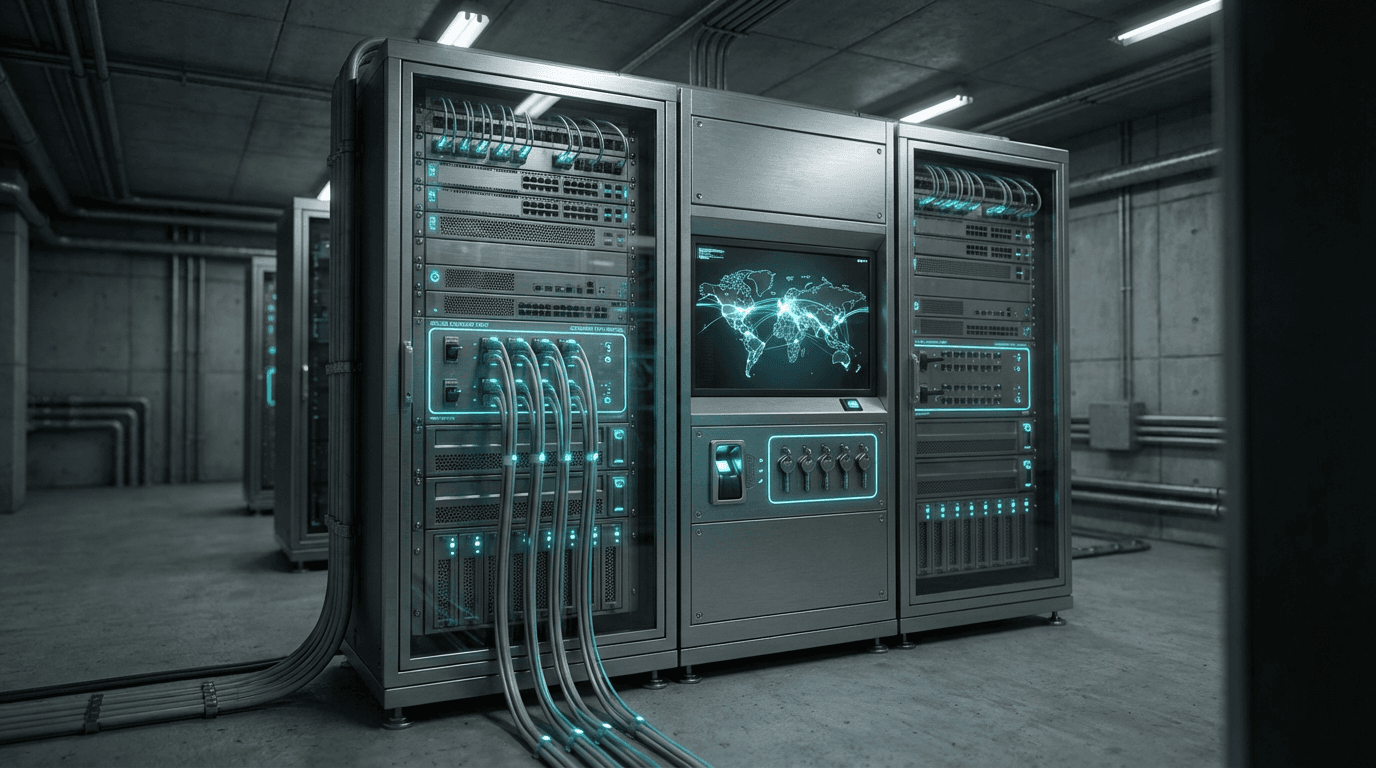
Network sovereignty and cross-border data control represent a fundamental shift in how nations and organizations manage the flow of digital information across borders. At its core, this approach involves implementing technical and policy mechanisms that enforce strict controls over data routing, storage locations, and jurisdictional access rights. The technical architecture typically combines several layers of control: geo-fencing technologies that restrict network traffic to specific geographic routes, regional data center infrastructures that ensure data residency within designated territories, and deep packet inspection systems that monitor and filter cross-border communications. These systems work in concert with policy frameworks that define lawful interception boundaries, determining which authorities can access telecommunications traffic and under what circumstances. The infrastructure often includes localized internet exchange points, domestic routing protocols, and encryption key management systems that remain under national control, effectively creating segmented portions of the global internet that operate according to specific territorial rules.
The rise of network sovereignty addresses several critical challenges facing both nations and enterprises in an increasingly interconnected world. For governments, concerns about national security, protection of critical infrastructure, and the ability to enforce local laws in cyberspace have driven the adoption of these controls. The traditional borderless nature of the internet has created jurisdictional ambiguities where data generated in one country might be stored in another and accessed from a third, complicating law enforcement, taxation, and regulatory oversight. For enterprises, particularly those in regulated industries like finance and healthcare, data sovereignty requirements have become a compliance imperative as different regions impose conflicting mandates about where customer information must reside. These controls also address economic concerns, as nations seek to ensure that the value generated by domestic digital activity—and the infrastructure supporting it—remains within their borders rather than flowing exclusively to foreign technology providers. Additionally, privacy advocates have pointed to data localization as a potential safeguard against mass surveillance by foreign intelligence agencies, though this remains a contested claim.
Current implementations of network sovereignty vary widely across regions, with countries like China, Russia, and India having established comprehensive frameworks that mandate local data storage and routing for certain categories of information. The European Union's approach through regulations like GDPR represents a different model, emphasizing data protection rights while maintaining some degree of cross-border flow within the bloc. Major telecommunications providers and cloud service operators have responded by establishing regional data centers and offering geo-specific routing options, though this fragmentation introduces new complexities and costs. Industry analysts note a growing tension between the efficiency gains of a globally integrated internet and the political and security imperatives driving digital balkanization. As geopolitical competition intensifies and concerns about technology dependence deepen, the trajectory points toward increasingly sophisticated technical controls that can enforce sovereignty at the network layer while attempting to maintain interoperability where needed. This evolution will likely reshape the fundamental architecture of global telecommunications, moving from a model of borderless connectivity toward one of controlled, conditional access between distinct digital territories.
Related Organizations
The central internet regulator, censor, and oversight and control agency for the People's Republic of China.
A European initiative developing a federated data infrastructure to ensure data sovereignty and availability across Europe.
The Federal Service for Supervision of Communications, Information Technology and Mass Media in Russia.
A web infrastructure and security company that has already enabled PQC support for a significant portion of the internet.
Promotes the Autonomous Driving Network (ADN) concept which relies heavily on network digital twins for self-optimization.
The IT services subsidiary of Deutsche Telekom, offering sovereign cloud solutions.
Prime contractor for the TeQuantS project and a key partner in ESA's quantum satellite initiatives.
Software corporation specializing in 3D design and digital mock-ups.
A leading European web hosting and cloud partner offering sovereign cloud solutions compliant with GDPR and German regulations.
A leading academic consortium based at Georgia Tech analyzing global internet governance.