Fully Homomorphic Encryption
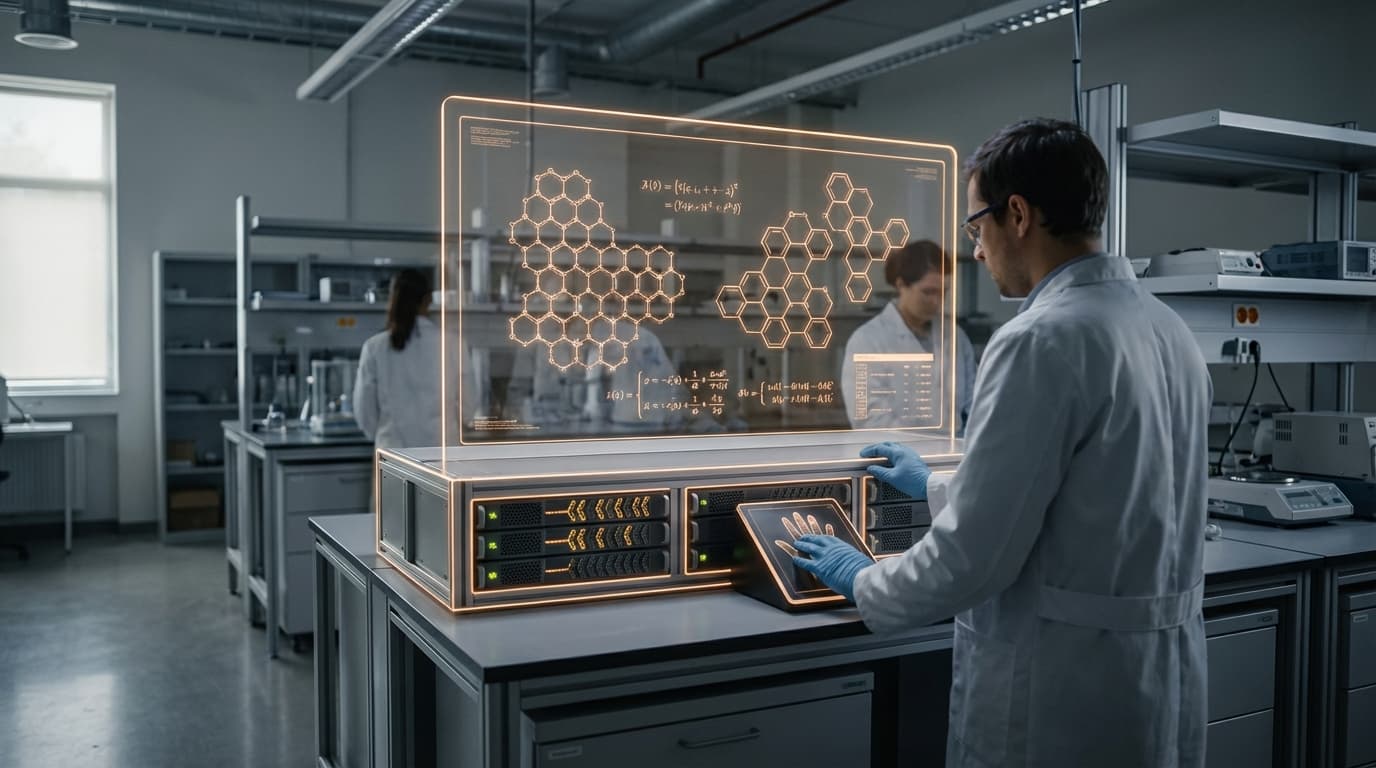
Fully Homomorphic Encryption represents a breakthrough in cryptographic techniques that enables computations to be performed directly on encrypted data without requiring decryption at any stage. Unlike traditional encryption methods that necessitate decrypting data before processing—creating vulnerability windows where sensitive information is exposed—FHE maintains data in its encrypted state throughout the entire computational process. The technology relies on mathematical lattice-based cryptographic schemes that preserve the algebraic structure of data even when encrypted, allowing operations like addition and multiplication to be performed on ciphertext. The results of these computations remain encrypted and can only be decrypted by the holder of the private key, revealing the same outcome as if the operations had been performed on the original plaintext data.
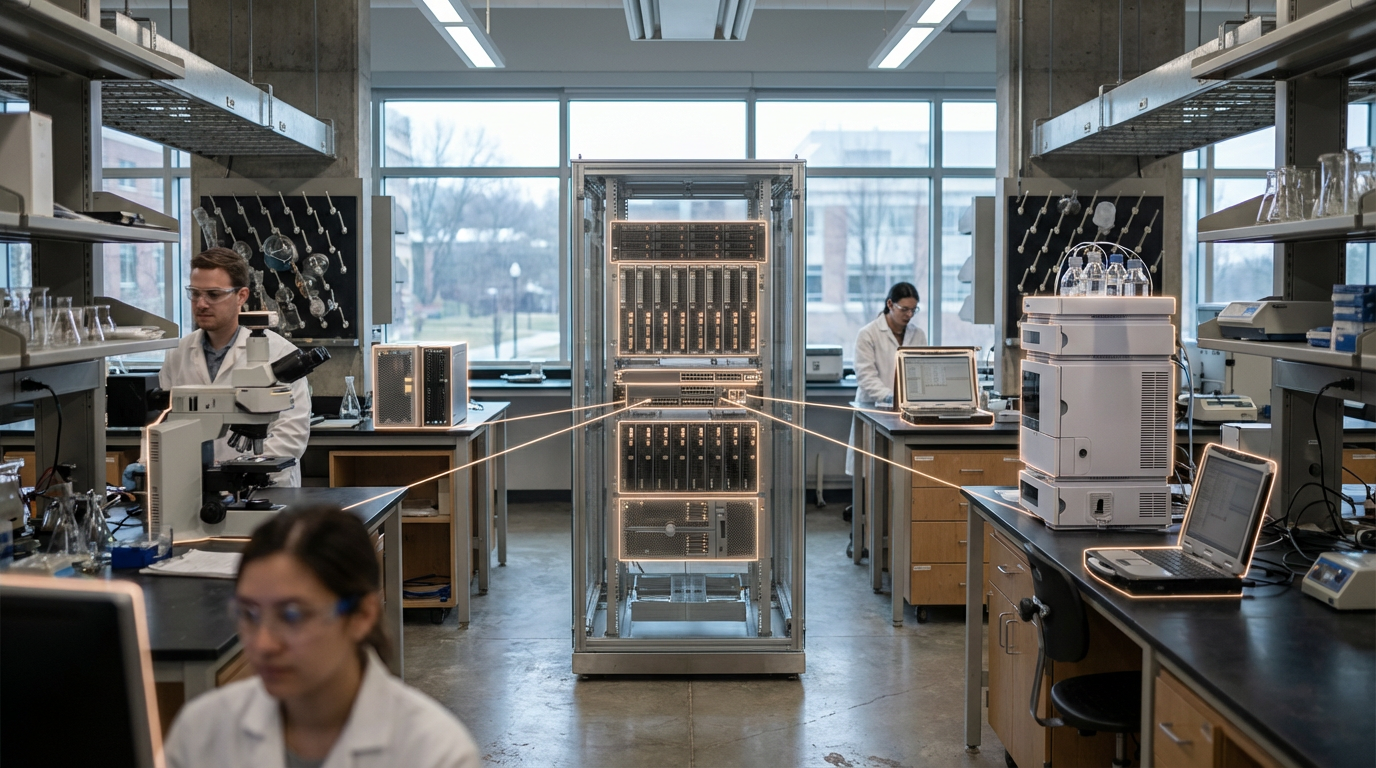
The fundamental problem this technology addresses is the inherent tension between data utility and data privacy in modern digital systems. Organizations increasingly rely on cloud computing and third-party services to process vast amounts of sensitive information, yet this outsourcing creates significant security risks. Traditional approaches force a choice between maintaining strict data privacy through encryption or enabling useful computation by exposing data to processing environments. This dilemma is particularly acute in identity verification systems, where databases containing personal information must be queried and analysed while remaining protected from both external attackers and potentially compromised service providers. FHE eliminates this trade-off by enabling verification checks, pattern matching, and authentication processes to run on encrypted databases without ever exposing the underlying user credentials, biometric data, or personal identifiers. This capability transforms how organizations can approach compliance with data protection regulations while still maintaining operational functionality.
Current implementations of FHE are emerging in sectors where privacy requirements are paramount, including healthcare data analysis, financial fraud detection, and secure multi-party computation scenarios. Research institutions and technology companies are actively developing optimised FHE schemes to address the computational overhead that has historically limited practical deployment, with recent advances showing significant performance improvements. In identity and verification contexts, early applications include privacy-preserving background checks, encrypted credential verification for access control systems, and secure authentication protocols that never expose user passwords or biometric templates to the verifying party. As quantum computing threats loom over traditional encryption methods, FHE's foundation in lattice-based cryptography also positions it as a quantum-resistant solution, making it increasingly relevant for future-proof security architectures. The technology represents a critical evolution in how trust can be established and maintained in digital systems, enabling verification without visibility and computation without compromise.