Decentralized Identity & eSIM Authentication
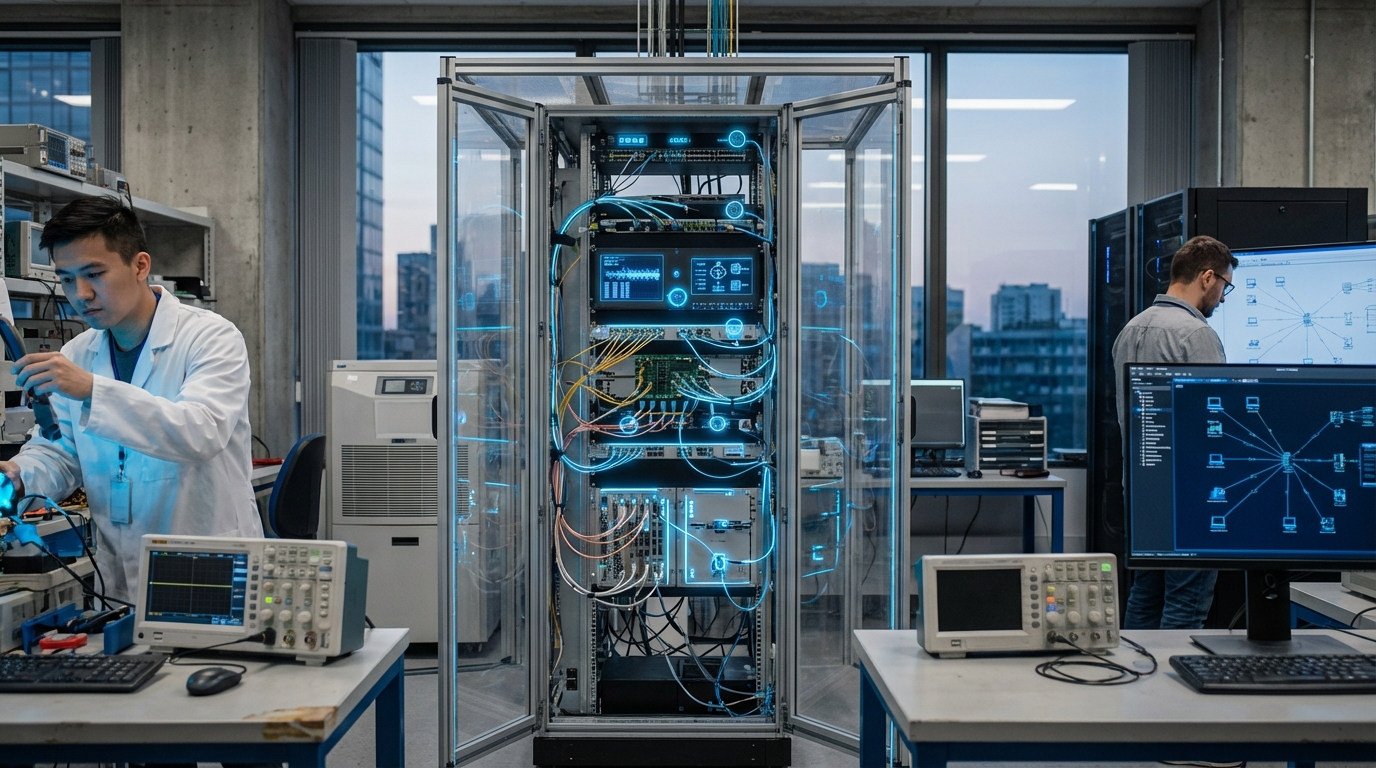
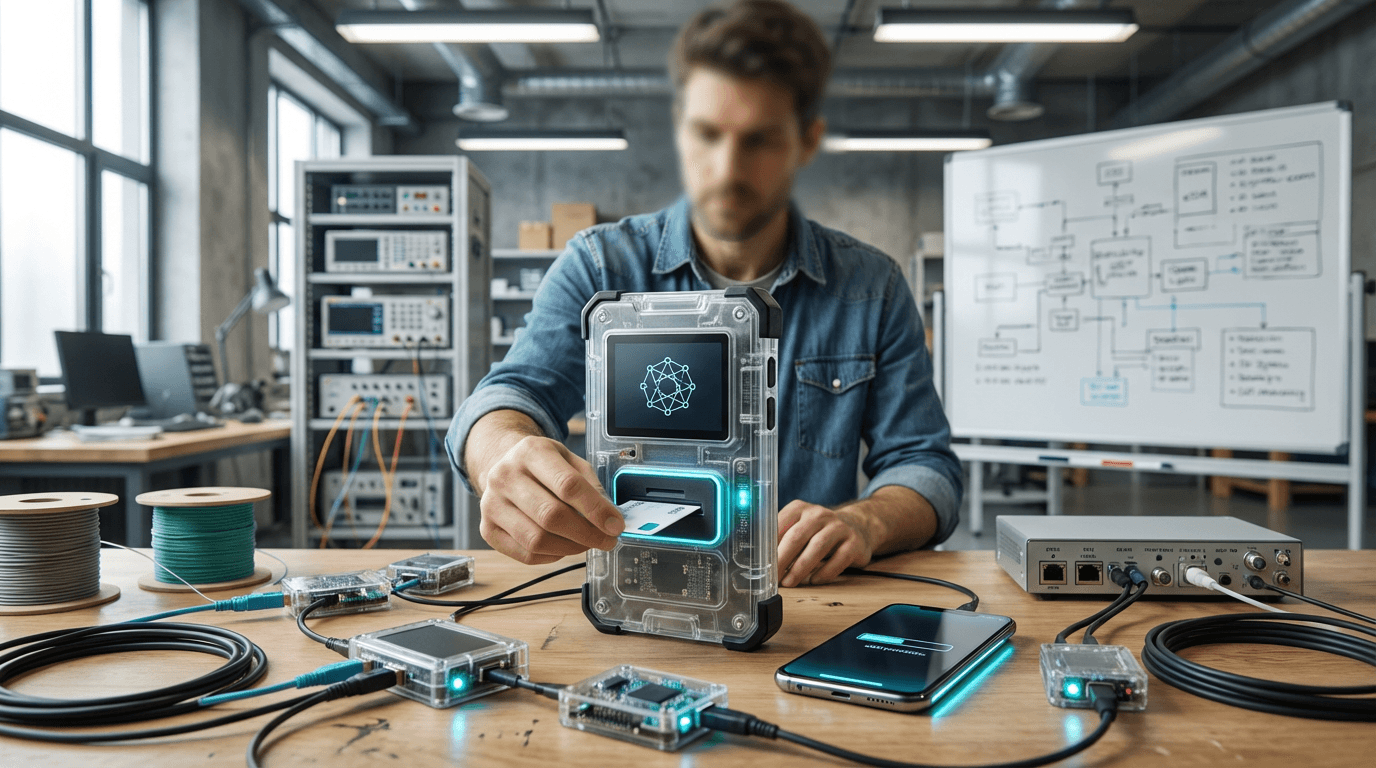
The convergence of decentralized identity frameworks and embedded SIM technology addresses a fundamental vulnerability in modern telecommunications: the centralized control of user identity and network access. Traditional mobile network authentication relies on physical SIM cards issued and managed by carriers, creating single points of failure susceptible to SIM-swap attacks, where malicious actors convince carriers to transfer a victim's phone number to a new device. Decentralized identity systems, built on blockchain protocols or W3C Decentralized Identifier (DID) standards, shift control of digital credentials to individual users rather than centralized authorities. When combined with eSIM (embedded SIM) and iSIM (integrated SIM) technologies—which allow remote provisioning and reprogramming of subscriber credentials directly onto device chipsets—this approach creates a self-sovereign authentication model. Users maintain cryptographic control over their network identity, storing verifiable credentials in secure enclaves on their devices rather than relying solely on carrier-managed databases. The technical mechanism leverages public-key cryptography and distributed ledger technology to create tamper-evident identity records that users can selectively share with network operators, application providers, or other services without surrendering permanent control.
For telecommunications providers and enterprises, this architecture solves critical challenges around security, operational efficiency, and user privacy. SIM-swap fraud has become a growing vector for account takeovers, particularly targeting cryptocurrency holders and high-value accounts, with attackers exploiting social engineering vulnerabilities in carrier customer service processes. Decentralized identity authentication eliminates this attack surface by requiring cryptographic proof of identity ownership rather than relying on call center verification. The integration with eSIM technology enables dynamic, instant switching between network operators without physical card swaps, addressing the longstanding problem of vendor lock-in and enabling true global roaming flexibility. For mobile virtual network operators (MVNOs) and Internet of Things deployments, this model dramatically reduces provisioning costs and time-to-market, as devices can be remotely configured with appropriate network credentials based on location, usage patterns, or contractual arrangements. Privacy-preserving authentication protocols allow users to prove eligibility for network services without revealing unnecessary personal information, addressing growing regulatory requirements around data minimization and user consent.
Several telecommunications consortiums and standards bodies are actively developing frameworks to operationalize these capabilities, with early pilots demonstrating feasibility in enterprise mobility management and IoT connectivity scenarios. The technology shows particular promise for international travelers, who could seamlessly authenticate to local networks without traditional roaming agreements or physical SIM purchases, and for devices requiring multi-network redundancy, such as connected vehicles or critical infrastructure sensors. Industry analysts note that the shift toward self-sovereign identity aligns with broader trends in zero-trust security architectures and user-centric data governance. As 5G networks expand and the number of connected devices multiplies, the combination of decentralized identity and programmable SIM provisioning represents a pathway toward more resilient, flexible, and privacy-respecting telecommunications infrastructure, potentially reshaping the relationship between users, devices, and network operators in fundamental ways.
Related Organizations
German security technology group specializing in currency and asset protection.
Identity and security company developing offline CBDC payment cards and secure elements.
Prime contractor for the TeQuantS project and a key partner in ESA's quantum satellite initiatives.
South Korea's largest wireless telecommunications operator.
Global mobile network and eSIM technology provider (formerly Truphone).
An engineering-driven organization developing specifications and standards for decentralized identity.
Nonprofit organization governing the Sovrin Network, a public service for self-sovereign identity.
Long-standing identity verification company now focusing on Civic Pass, a tool for on-chain identity and access management.
eSIM solutions provider for mobile virtual network operators (MVNOs).