Digital Executor Authentication
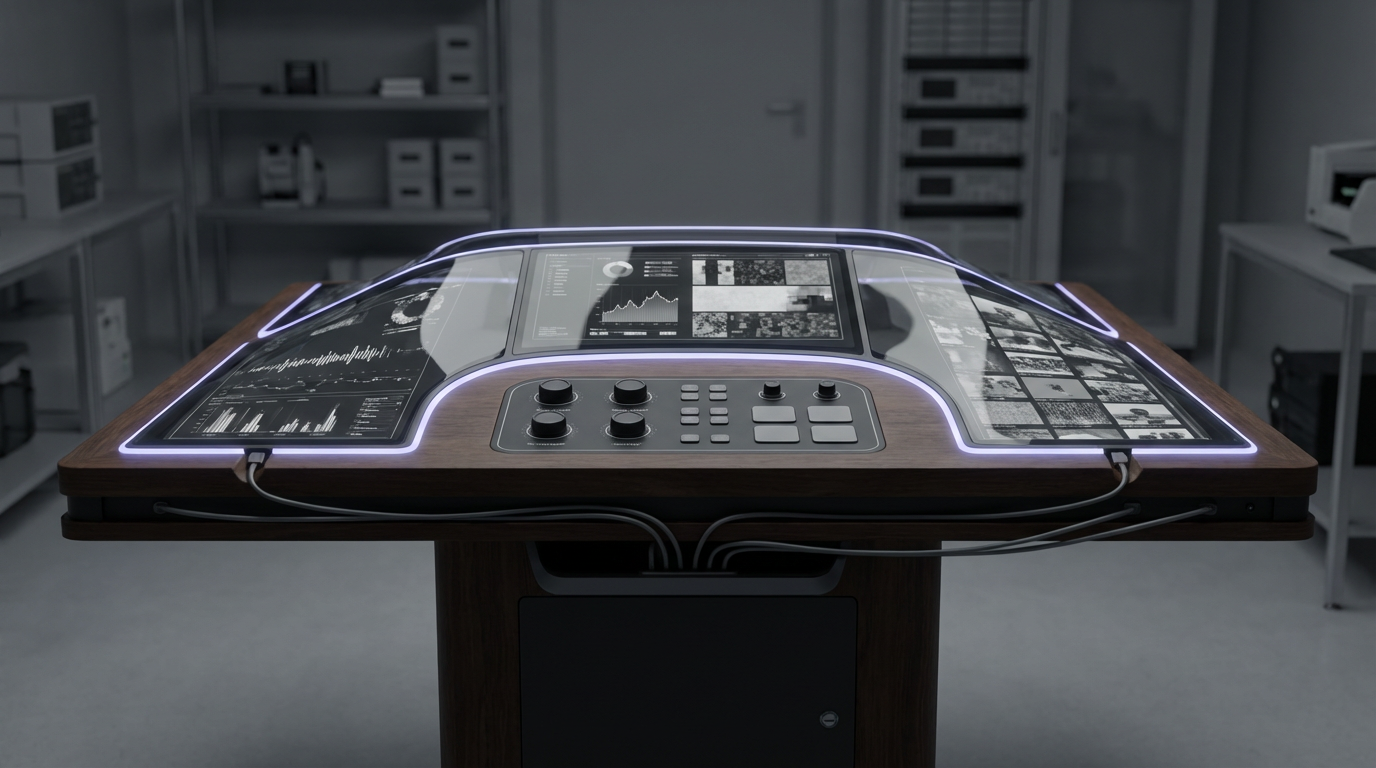
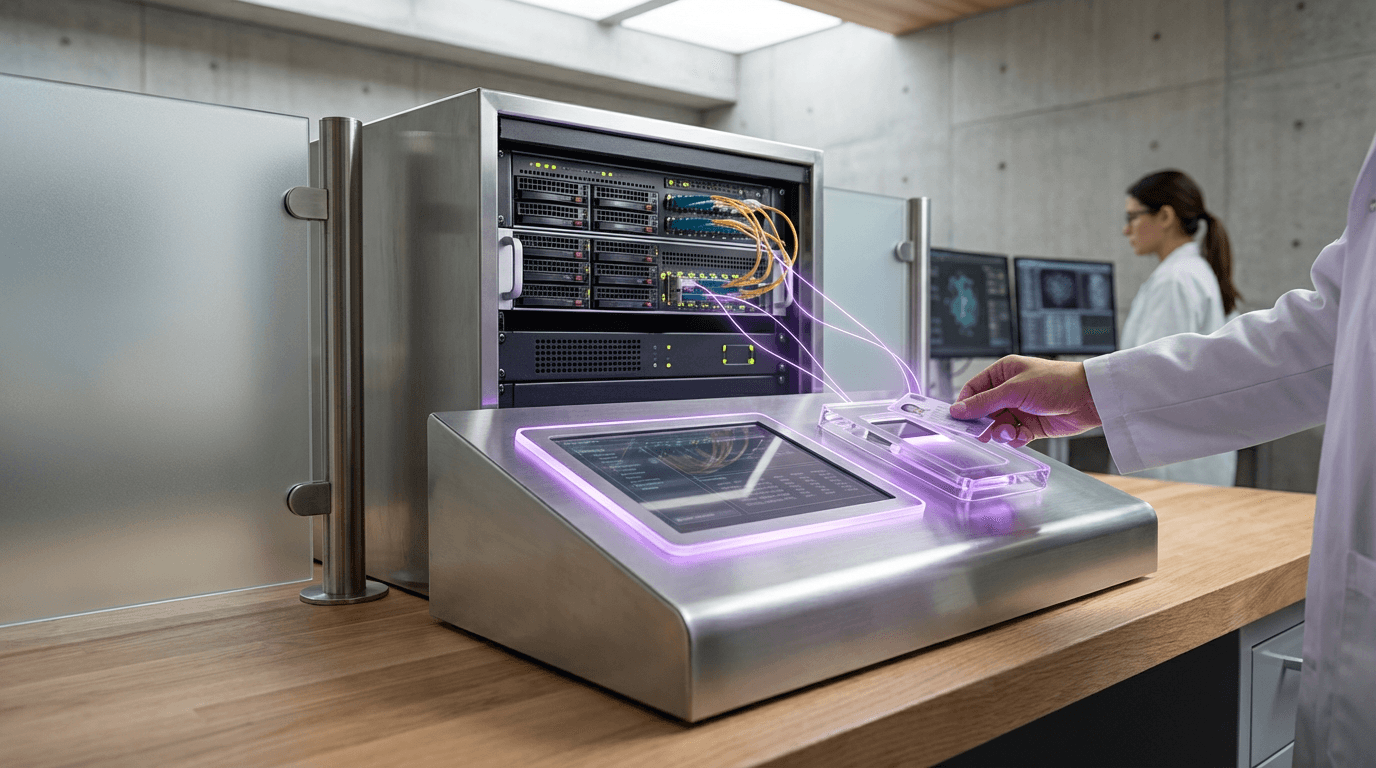
The management of digital assets after death has become an increasingly complex challenge as our lives become more intertwined with online platforms, cloud storage, and digital services. Traditional estate planning frameworks were designed for physical assets and financial accounts, leaving a significant gap in how we handle the vast digital footprints that individuals accumulate over their lifetimes. Digital Executor Authentication addresses this gap through sophisticated cryptographic and biometric verification systems that enable designated individuals to access specific portions of a deceased person's digital estate in a controlled, secure manner. These systems typically employ multi-factor authentication protocols, including cryptographic key pairs, biometric verification of the executor, and time-locked access mechanisms that prevent unauthorised entry while ensuring legitimate executors can fulfil their duties. The technology often incorporates blockchain-based verification chains or distributed ledger systems to create immutable records of access attempts and successful authentications, providing transparency and accountability in the estate settlement process. By compartmentalising digital assets into distinct access tiers, these systems allow executors to retrieve essential documents, photographs, or account information without exposing sensitive data such as private communications, medical records, or other protected information that the deceased may have wished to remain confidential.
The financial services, technology, and legal industries face mounting pressure to develop standardised approaches to digital estate management as regulatory frameworks struggle to keep pace with technological change. Digital Executor Authentication solves the critical problem of balancing access rights with privacy protection, addressing concerns from both platform providers who face liability risks and families who need to settle estates efficiently. Traditional approaches often required either sharing passwords in advance—compromising security during the account holder's lifetime—or lengthy legal processes to prove death and establish executor rights to each individual service provider. This technology eliminates these inefficiencies by creating a unified authentication framework that can be recognised across multiple platforms and services. Early implementations suggest that these systems can reduce estate settlement timelines by months while simultaneously strengthening security protocols, as they eliminate the need for password sharing or the creation of vulnerable master access credentials. The technology also enables more nuanced estate planning, allowing individuals to specify different access levels for different executors, ensuring that financial matters, personal communications, and creative works can be handled by the most appropriate parties.
Several digital estate planning services and financial institutions have begun piloting digital executor authentication systems, with some jurisdictions exploring regulatory frameworks to standardise these protocols across the industry. Current applications range from simple password vault systems with designated beneficiary access to sophisticated platforms that integrate with major technology companies' account recovery processes. The technology is particularly relevant for managing cryptocurrency wallets, cloud storage accounts, social media profiles, and subscription services, where traditional probate processes often prove inadequate. As digital assets increasingly represent significant financial and sentimental value—from cryptocurrency holdings to irreplaceable family photographs stored in the cloud—the demand for robust authentication systems continues to grow. Industry analysts note that this technology aligns with broader trends toward zero-trust security architectures and privacy-preserving data management, suggesting that digital executor authentication will become a standard feature of comprehensive estate planning services within the next decade. The evolution of these systems may also influence how platforms design their services, encouraging the development of built-in legacy planning features that respect both security requirements and the emotional needs of bereaved families navigating digital inheritance.
Related Organizations
Developing 'Apple Intelligence', a personal intelligence system integrated into iOS/macOS that uses on-device context to mediate tasks and information.
A comprehensive digital legacy platform allowing users to manage social media, financial accounts, and memories, including AI-driven photo animation.
Creators of CausalImpact, a package for causal inference using Bayesian structural time-series.
A digital inheritance service that detects fatal events and unlocks assigned assets to beneficiaries.
A password manager that includes 'Emergency Kit' features to facilitate digital access transfer to next of kin.
Software for logging last wishes, including social media wills and digital legacy curation.
Online will-writing platform that includes provisions for digital assets and executor instructions.
Security software including a password manager with 'Emergency Access' features for trusted contacts.