Digital Twin Identity Frameworks
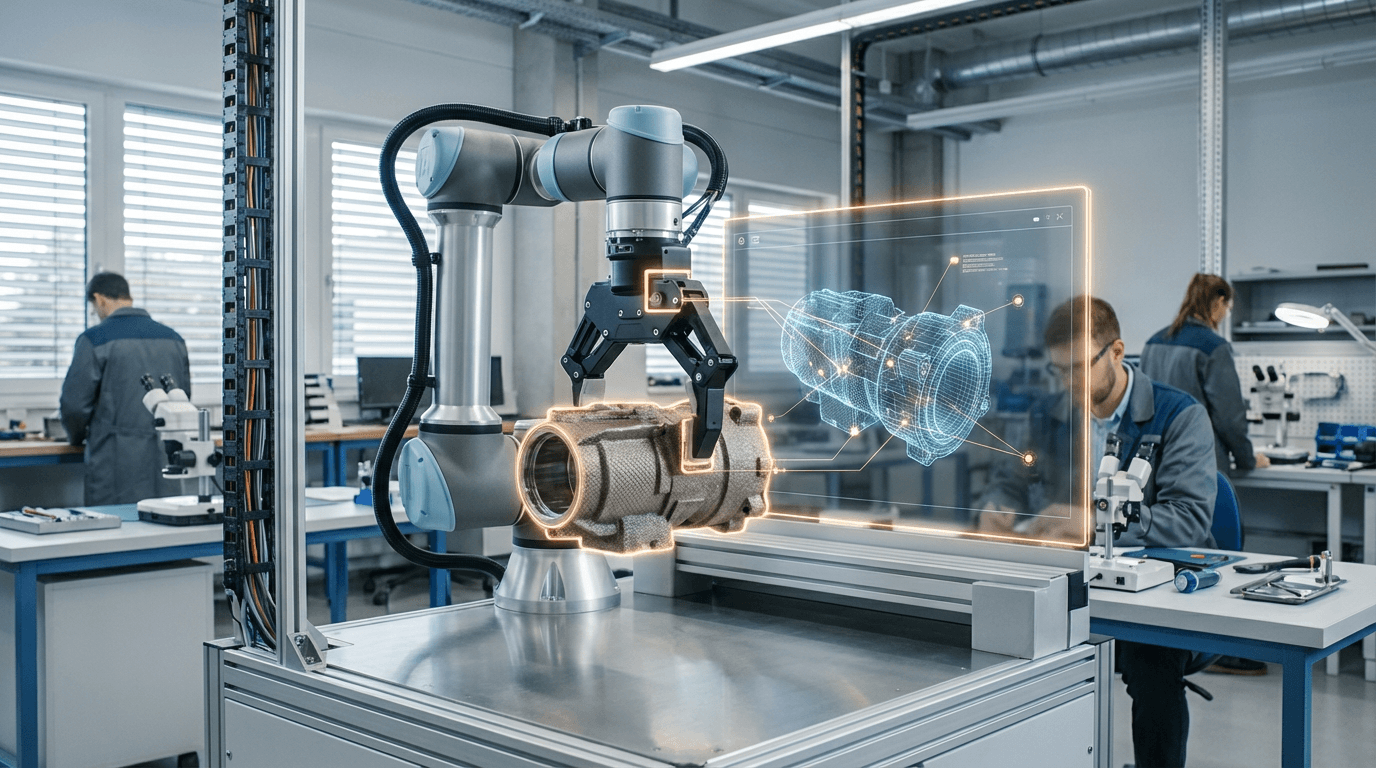
Digital Twin Identity Frameworks address a fundamental challenge in the convergence of physical and digital systems: establishing verifiable, tamper-proof connections between real-world assets and their virtual counterparts. As industries increasingly rely on digital twins—virtual replicas that mirror the state, behavior, and performance of physical objects—the integrity of data flowing between these domains becomes critical. These frameworks employ cryptographic binding mechanisms, often leveraging public key infrastructure, blockchain-based registries, or hardware security modules embedded in physical assets. Each physical object receives a unique cryptographic identity at manufacture or deployment, creating an immutable link that persists throughout the asset's lifecycle. This identity binding ensures that sensor data transmitted from a turbine, manufacturing robot, or building system can be verified as originating from the authentic source, while commands or configuration changes sent to the physical asset can be validated as coming from authorized digital twin instances.
The absence of robust identity frameworks for digital twins creates significant vulnerabilities in industrial operations and critical infrastructure. Without cryptographic verification, malicious actors could inject false sensor readings into a digital twin, causing predictive maintenance algorithms to make incorrect decisions, or send unauthorized commands to physical systems with potentially catastrophic consequences. Industries managing high-value assets—aerospace manufacturers tracking engine performance, energy companies monitoring offshore platforms, or smart building operators managing HVAC and security systems—face particular risks from such spoofing attacks. These frameworks solve this problem by creating a chain of trust that extends from the physical sensor or actuator through communication networks to cloud-based analytics platforms. This enables organizations to confidently automate critical decisions based on digital twin insights, knowing that the underlying data integrity is cryptographically assured. The technology also facilitates regulatory compliance in sectors where asset provenance and operational history must be auditable and verifiable.
Early implementations of digital twin identity frameworks are emerging in aerospace, where manufacturers are embedding secure identities in aircraft components to enable trusted lifecycle tracking and predictive maintenance across global fleets. Industrial equipment manufacturers are similarly integrating these capabilities into next-generation machinery, while smart city initiatives are exploring their application for infrastructure assets like bridges and water systems. Research suggests that as digital twins become more autonomous—making decisions and initiating actions with minimal human oversight—the importance of cryptographic identity binding will intensify. Industry analysts note that these frameworks are converging with broader trends in zero-trust architecture and decentralized identity systems, potentially enabling new models where assets can autonomously negotiate service contracts or participate in peer-to-peer industrial networks. The trajectory points toward a future where every significant physical asset possesses a verifiable digital identity, creating a foundation for trusted automation across industrial ecosystems and enabling the secure orchestration of increasingly complex cyber-physical systems.




