Privacy-Preserving Network Analytics
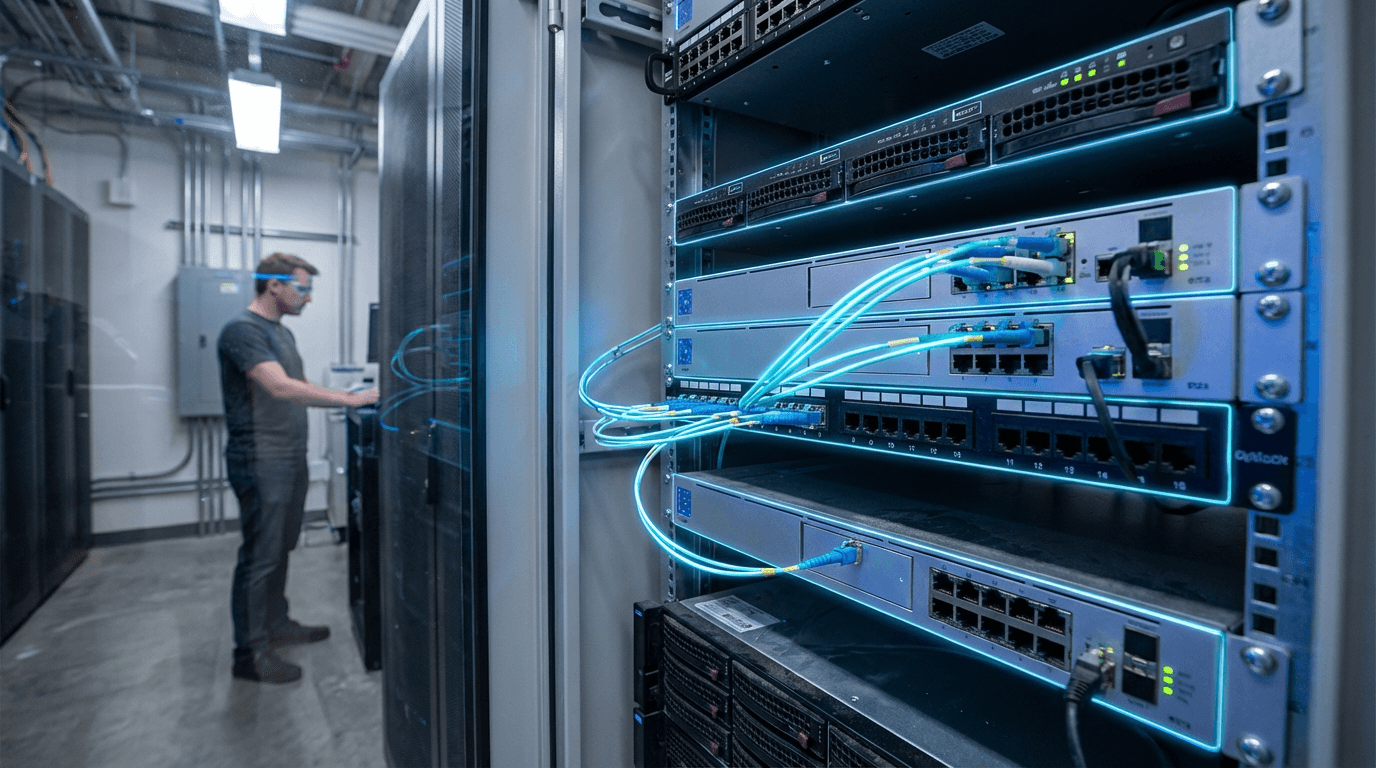
The telecommunications industry faces a fundamental tension between operational necessity and privacy protection. Network operators require detailed analytics to optimise infrastructure, detect anomalies, and plan capacity expansions, yet this same data contains sensitive information about individual users' locations, communications patterns, and behaviours. Traditional analytics approaches often require direct access to raw network data, creating substantial privacy risks and exposing operators to regulatory scrutiny under frameworks like GDPR and various national data protection laws. Privacy-preserving network analytics addresses this challenge by enabling telecommunications companies to extract valuable insights from network data while mathematically guaranteeing that individual user information remains protected. These techniques employ sophisticated cryptographic and statistical methods—including differential privacy, which adds carefully calibrated noise to datasets to mask individual contributions; secure multi-party computation, which allows multiple parties to jointly analyse data without revealing their individual inputs; and federated learning, which trains machine learning models across distributed datasets without centralising the underlying information.
The implementation of privacy-preserving analytics transforms how telecommunications operators approach critical business functions while maintaining compliance with increasingly stringent data protection requirements. Network optimisation, traditionally dependent on detailed user movement and usage patterns, can now be performed using aggregated insights that preserve individual anonymity. Fraud detection systems can identify suspicious patterns across the network without exposing the specific behaviours of legitimate users. Capacity planning benefits from understanding traffic flows and congestion points while avoiding the collection of personally identifiable information that could create liability. This approach fundamentally reduces both regulatory risk and the potential reputational damage associated with data breaches or misuse, as operators can demonstrate through cryptographic proofs that their analytics processes cannot reconstruct individual user activities. The technology also enables new forms of collaboration between operators and third parties, such as urban planners or public health researchers, who can access network-derived insights without ever touching sensitive raw data.
Early deployments of privacy-preserving network analytics have emerged across telecommunications infrastructure, with operators beginning to integrate these techniques into their standard analytical workflows. Research initiatives have demonstrated the viability of using differential privacy for cell tower optimisation and federated learning for predictive maintenance of network equipment. As regulatory pressure intensifies and public awareness of data privacy grows, these techniques are transitioning from experimental implementations to core components of network management systems. The technology aligns with broader industry movements toward zero-trust architectures and privacy-by-design principles, suggesting that privacy-preserving analytics will become standard practice rather than optional enhancement. Looking forward, the continued refinement of these methods promises to unlock new applications, from real-time network slicing in 5G environments to collaborative analytics across multiple operators, all while maintaining the mathematical guarantees of privacy protection that regulators and consumers increasingly demand.
Related Organizations
A community-driven organization building privacy-preserving AI technology, including PySyft for encrypted, privacy-preserving deep learning.
Provides a platform for secure data collaboration using Homomorphic Encryption.
Industrial research lab with a history of fundamental research in condensed matter physics relevant to topological phases.
Open-source cryptography company building state-of-the-art Fully Homomorphic Encryption (FHE) tools and libraries.
Data privacy software company enabling organizations to use sensitive data safely for analytics.

Replica Analytics
Canada · Company
Develops synthetic data generation technologies for the healthcare industry; acquired by Aetion.
Launched the Digital Asset Broker (DAB) platform to allow devices to trade securely using blockchain technology.