Food System Cyber-Resilience
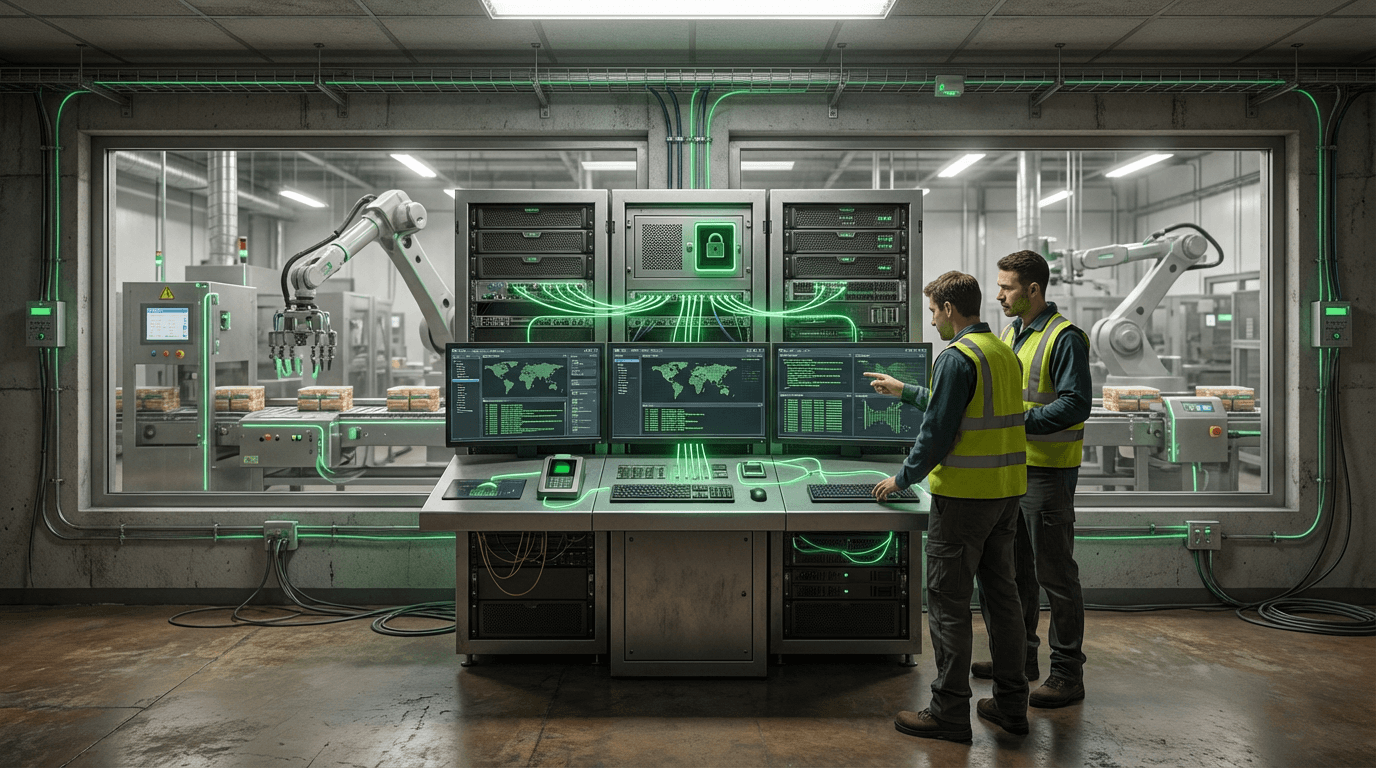
The increasing digitization of agricultural and food supply systems has created unprecedented vulnerabilities to cyber threats. Food System Cyber-Resilience encompasses a comprehensive framework of security measures, protocols, and technologies designed to protect the interconnected digital infrastructure that underpins modern food production, processing, and distribution. At its technical core, this approach integrates multiple layers of defense including network segmentation, real-time threat detection systems, encrypted communication protocols, and secure firmware updates for IoT devices deployed across farms, processing facilities, and cold chain logistics networks. The framework addresses specific vulnerabilities inherent in agricultural technology, such as the remote sensors monitoring soil conditions, automated irrigation systems, climate-controlled storage facilities, and GPS-enabled fleet management platforms that have become standard in contemporary food supply chains. These systems often operate on legacy industrial control systems that were not originally designed with cybersecurity in mind, making them particularly susceptible to ransomware attacks, data breaches, and operational disruption.
The food and agriculture sector faces unique cybersecurity challenges that distinguish it from other critical infrastructure domains. A successful cyberattack on food systems can have cascading effects that extend far beyond financial losses, potentially disrupting food availability, compromising food safety, and threatening public health. Recent years have seen growing concerns about threat actors targeting agricultural cooperatives, meat processing plants, and distribution networks, with attacks capable of halting production lines, corrupting temperature monitoring systems in cold storage, or manipulating automated feeding systems in livestock operations. Food System Cyber-Resilience addresses these vulnerabilities by implementing industry-specific security standards that account for the operational realities of agricultural environments, where equipment may operate in remote locations with limited connectivity, where systems must function continuously during critical harvest or processing periods, and where the workforce may have varying levels of technical expertise. This approach enables food producers and distributors to maintain operational continuity while protecting sensitive data related to proprietary farming techniques, supply chain logistics, and customer information.
Industry adoption of cyber-resilience frameworks is accelerating as regulatory bodies and insurance providers increasingly require documented security measures for food infrastructure operators. Early implementations focus on establishing baseline security hygiene, such as multi-factor authentication for system access, regular security audits of connected devices, and incident response plans tailored to agricultural operations. Larger food companies are investing in security operations centers that monitor their extended supply chains, while industry consortiums are developing shared threat intelligence platforms specific to agricultural technology vulnerabilities. Looking forward, the integration of artificial intelligence for anomaly detection and the development of security-by-design principles for new agricultural IoT devices represent critical evolution points for this field. As climate change drives greater reliance on precision agriculture and automated systems, and as geopolitical tensions highlight food security as a national priority, robust cyber-resilience will become not merely a technical requirement but a fundamental component of ensuring stable, secure food supplies for growing populations.
Related Organizations
The Information Sharing and Analysis Center specifically for the food and agriculture sector to share threat intelligence.
Conducts advanced research in transient electronics for agriculture, specifically soil nitrate sensors.
The world's largest meat processing company, which acquired BioTech Foods and is building a cultivated meat plant in Spain.

Federal Bureau of Investigation (FBI)
United States · Government Agency
Issues specific Private Industry Notifications (PINs) regarding ransomware threats to the Food and Agriculture sector.
A major agricultural machinery manufacturer (Fendt, Massey Ferguson) that integrates security protocols into its connected fleet and internal operations.
Specializes in securing the Extended Internet of Things (XIoT), bridging the gap between IT, OT, and IoT security.
US federal agency responsible for guiding the government's migration to post-quantum cryptography.
Provides industrial cybersecurity platform for asset identification, threat detection, and response in OT environments.
Specialist university for the agri-food sector.
Delivers OT and IoT visibility and security, using AI to detect anomalies in industrial control networks.
The regulatory body convening advisory committees to discuss the safety, efficacy, and ethics of artificial womb technology (EXTEND).
A not-for-profit organization that operates FFRDCs.

Armis
United States · Startup
Asset intelligence platform that discovers and secures managed, unmanaged, and IoT/OT devices.
A global machinery giant that operates the Operations Center, one of the largest repositories of agronomic and machine data in the world.














