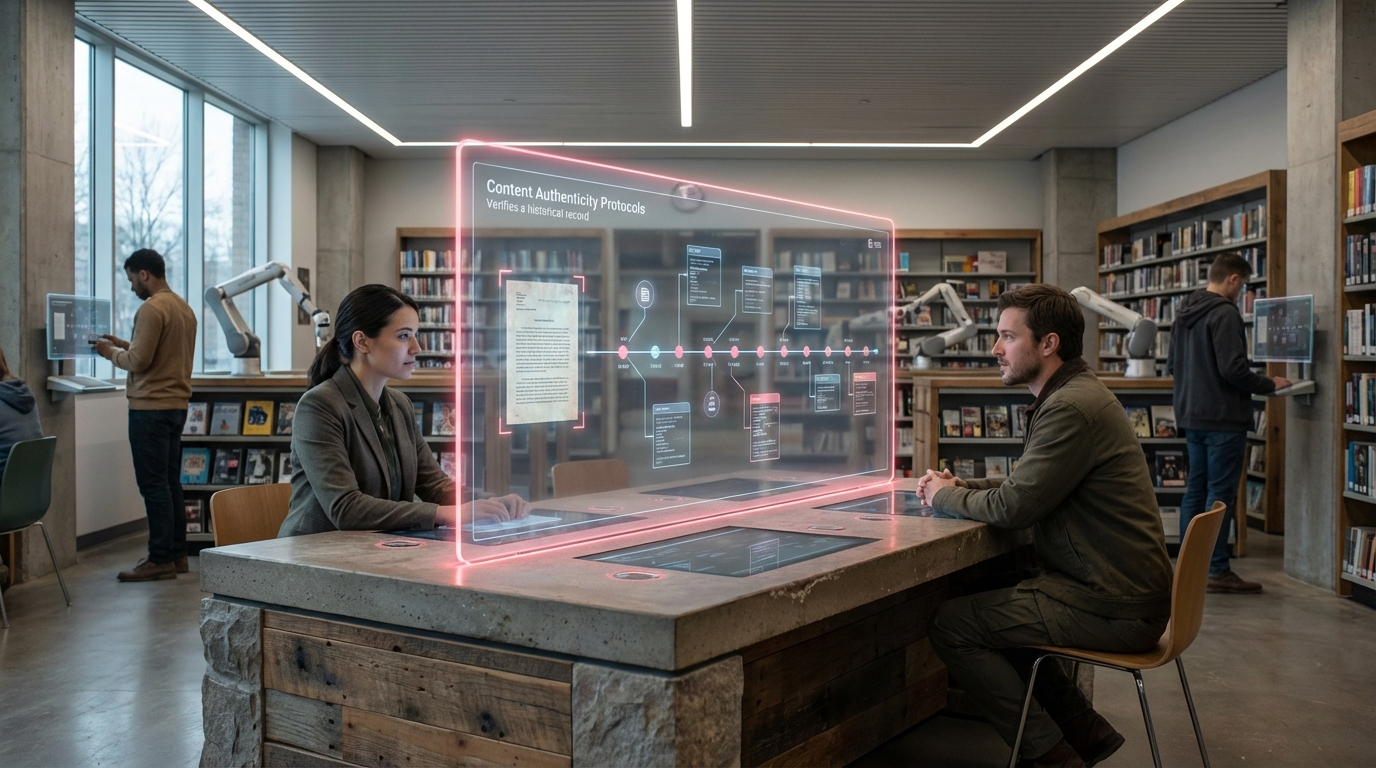
Zero-Knowledge Access Protocols
Zero-knowledge access protocols represent a sophisticated cryptographic approach that addresses a fundamental tension in digital archives and knowledge repositories: the need to verify legitimate access rights while preserving user privacy. These systems employ advanced mathematical proofs that allow one party to demonstrate possession of specific credentials or attributes without revealing the underlying information itself. At their core, zero-knowledge proofs work through interactive or non-interactive protocols where a prover can convince a verifier that a statement is true—such as "I am affiliated with an accredited research institution"—without disclosing any additional details about their identity, location, or institutional affiliation. The cryptographic mechanisms typically involve commitment schemes, challenge-response protocols, and hash functions that create verifiable attestations while maintaining information asymmetry. This technical architecture ensures that access control systems can enforce necessary restrictions based on role, qualification, or institutional status without creating detailed logs of who accessed what resources and when.
The implementation of zero-knowledge access protocols addresses critical challenges facing digital libraries, research archives, and sensitive knowledge repositories in an era of heightened surveillance and data exploitation. Traditional access control systems create extensive audit trails that can reveal research interests, intellectual trajectories, and professional networks—information that may be exploited for competitive intelligence, political targeting, or commercial profiling. For institutions managing sensitive historical materials, medical research databases, or politically contentious archives, these protocols enable compliance with access restrictions while protecting researchers from potential retaliation or discrimination. The technology also resolves practical governance challenges by allowing federated access across multiple institutions without requiring centralised identity management or cross-institutional data sharing. This capability is particularly valuable for international research collaborations where different jurisdictions impose varying privacy regulations and where researchers may face risks if their inquiry into certain topics becomes known to authoritarian regimes or hostile actors.
Early implementations of zero-knowledge access protocols have emerged in blockchain-based credential systems and privacy-preserving authentication frameworks, with research institutions beginning to pilot these approaches for sensitive collections. Academic libraries managing restricted archives related to human rights documentation, indigenous knowledge systems, and corporate whistleblower materials are exploring these protocols as alternatives to conventional authentication systems. The technology aligns with broader movements toward privacy-preserving computation and the principle of data minimisation in digital infrastructure. As regulatory frameworks increasingly recognise intellectual privacy as essential to academic freedom and as surveillance capitalism extends into knowledge work, zero-knowledge access protocols offer a technical foundation for archives that can enforce legitimate access controls without becoming instruments of monitoring. The continued development of these systems will likely influence how future knowledge institutions balance openness with protection, enabling more equitable access to sensitive materials while safeguarding the privacy rights of those who seek to learn from them.
Related Organizations
Develops STARK-based scaling solutions for blockchain (StarkNet, StarkEx).
Formerly Polygon ID, providing Zero-Knowledge (ZK) identity infrastructure for verifiable credentials.
An engineering-driven organization developing the technical specifications and standards for decentralized identity.
Creators of Zcash and pioneers of zk-SNARKs implementation.
Long-standing leader in neuro-symbolic AI, combining neural networks with logical reasoning for enterprise applications.
A Layer-1 blockchain platform for building private applications using zero-knowledge cryptography.
Developing a privacy-first zero-knowledge rollup on Ethereum.
Stewards the Mina Protocol, a lightweight blockchain designed specifically for zero-knowledge applications (zkApps) and identity.
Building a privacy infrastructure (mixnet) to prevent data leakage.