OT Cybersecurity Defense
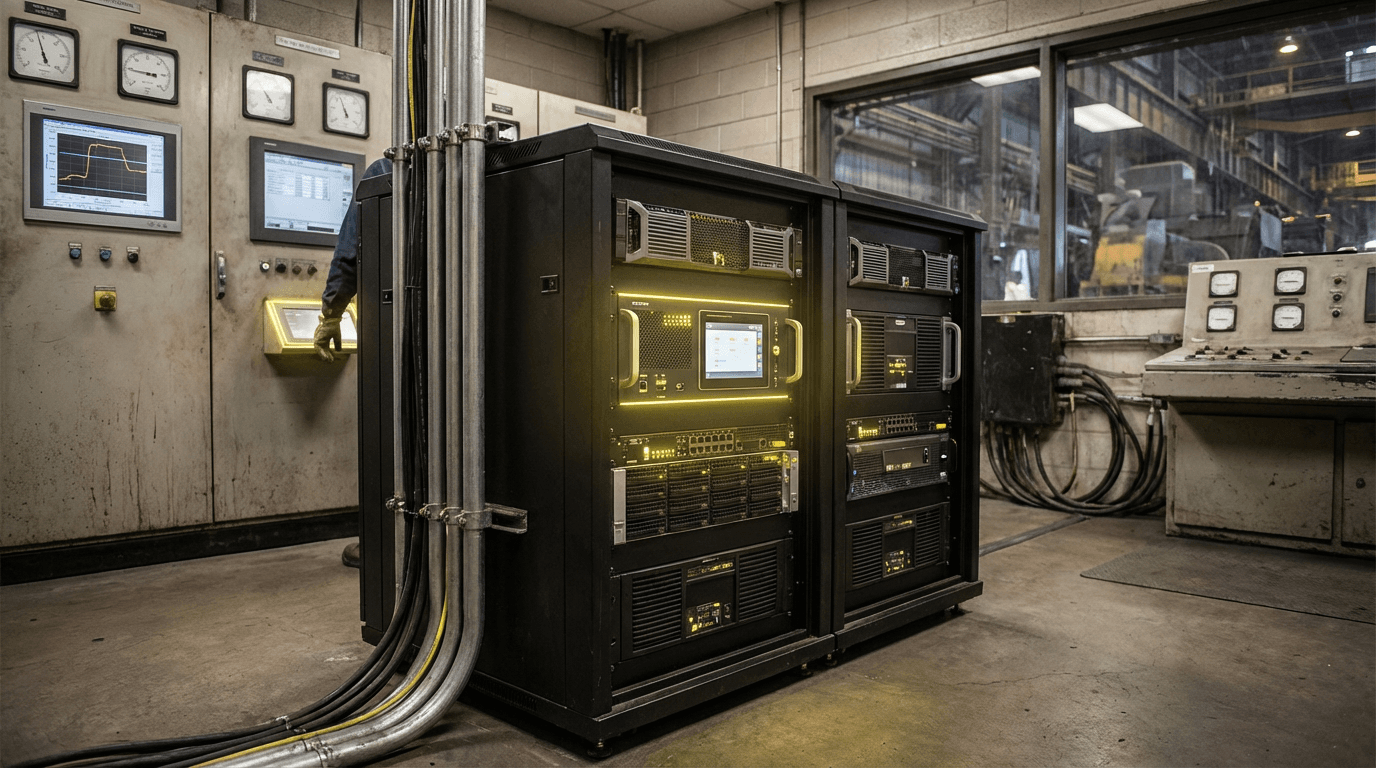
Operational Technology (OT) Cybersecurity Defense addresses the unique security challenges facing industrial control systems, SCADA (Supervisory Control and Data Acquisition) networks, and programmable logic controllers (PLCs) that manage critical physical processes in mining, refining, and heavy manufacturing environments. Unlike traditional IT systems designed for data processing, OT systems control physical equipment—from conveyor belts and crushers to chemical reactors and blast furnaces—where a security breach can result in equipment damage, environmental releases, worker injuries, or catastrophic facility failures. These defense solutions employ specialized techniques including network segmentation to isolate critical control systems, anomaly detection algorithms trained on industrial protocols like Modbus and DNP3, and real-time monitoring that can distinguish between legitimate operational commands and malicious interference. The architecture typically includes hardware-based security appliances positioned at critical network boundaries, protocol-aware firewalls that understand industrial communication patterns, and intrusion detection systems calibrated to recognize the normal operational signatures of specific industrial processes.
The convergence of OT and IT networks—driven by Industry 4.0 initiatives, remote monitoring capabilities, and data analytics requirements—has dramatically expanded the attack surface of industrial facilities that were historically air-gapped from external networks. Mining operations now face threats ranging from ransomware that can halt ore processing to sophisticated nation-state attacks targeting critical infrastructure. Traditional IT security approaches often prove inadequate because they can introduce latency incompatible with real-time control requirements, lack understanding of industrial protocols, or require system downtime for updates that continuous process industries cannot accommodate. OT cybersecurity solutions address these constraints by providing passive monitoring that doesn't interfere with control traffic, maintaining extensive asset inventories of legacy equipment that may run decades-old firmware, and enabling security updates during planned maintenance windows. These systems also help organizations comply with emerging regulatory frameworks and industry standards that increasingly mandate cybersecurity measures for critical infrastructure sectors.
Early implementations of OT cybersecurity have focused on high-value targets such as petroleum refineries, power generation facilities, and large-scale mining operations where the potential consequences of compromise are most severe. Industry analysts note growing adoption across the extractives sector as companies recognize that operational disruptions from cyber incidents can cost millions per hour in lost production. Deployment typically begins with network visibility projects that map existing OT assets and communication patterns, followed by segmentation strategies that limit lateral movement of potential threats, and ultimately progressing to active threat detection and response capabilities. Research suggests that the integration of artificial intelligence and machine learning into OT security platforms will enhance their ability to detect subtle anomalies indicative of advanced persistent threats while reducing false positives that plague earlier systems. As industrial facilities continue their digital transformation journey—incorporating IoT sensors, cloud connectivity, and remote operations centers—the sophistication and importance of OT cybersecurity defense will only intensify, making it an essential component of operational resilience for the extractives and heavy industry sectors.
Related Organizations
Non-profit professional association setting standards for automation.
Specializes in securing the Extended Internet of Things (XIoT), bridging the gap between IT, OT, and IoT security.
Provides industrial cybersecurity platform for asset identification, threat detection, and response in OT environments.
Delivers OT and IoT visibility and security, using AI to detect anomalies in industrial control networks.
Develops unidirectional security gateways (data diodes) that physically prevent cyberattacks from entering industrial control networks.

Armis
United States · Startup
Asset intelligence platform that discovers and secures managed, unmanaged, and IoT/OT devices.
Provides HVDC Plus technology (VSC) and transformers for ultra-high-voltage transmission projects globally.
Offers OT-native network security solutions to protect industrial environments from cyberattacks.
Provides a blockchain-protected cybersecurity mesh for industrial operations and critical infrastructure.








