Modular Forward-Deployed Data Centers
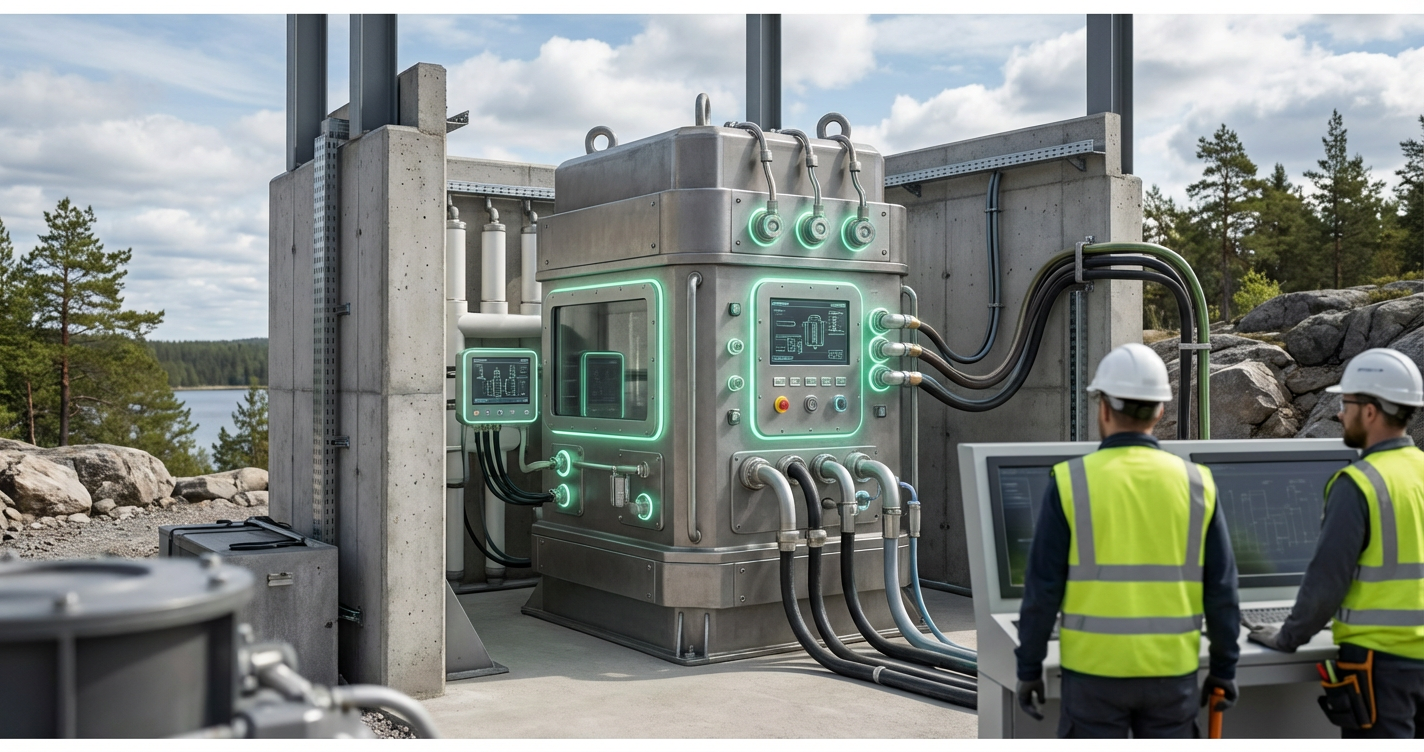
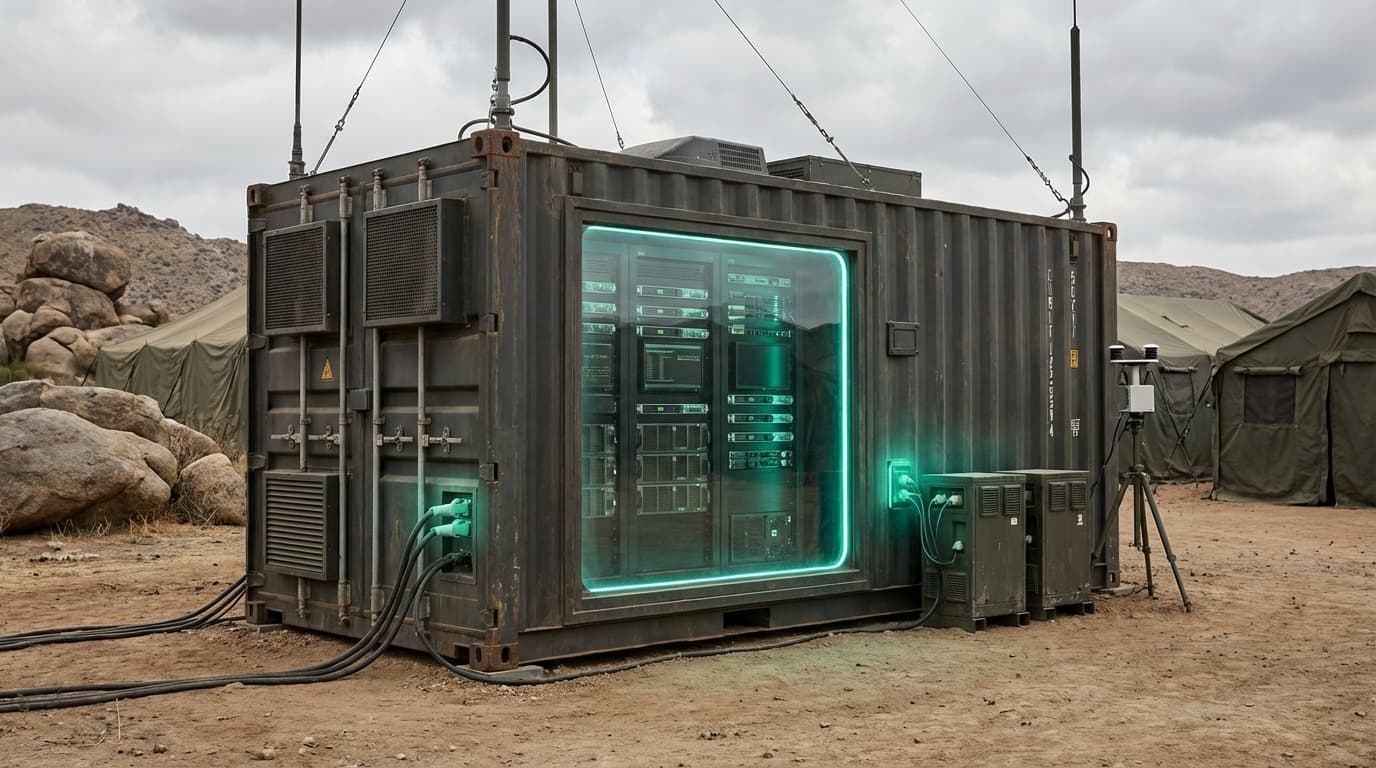
Modular forward-deployed data centers represent a specialized category of ruggedized computing infrastructure designed to operate in austere, contested, or rapidly changing environments where traditional fixed facilities are impractical or unavailable. These systems typically consist of containerized units—often based on standard shipping container dimensions—that house servers, networking equipment, power systems, and environmental controls within hardened enclosures. The modular design allows individual units to be transported via standard military logistics chains, including air, sea, and ground transport, and assembled on-site within hours or days rather than the months required for conventional data center construction. Key technical features include electromagnetic shielding, physical tamper-resistance, redundant cooling systems capable of operating in extreme temperatures, and self-contained power generation or conditioning systems that can interface with unstable electrical grids or tactical generators. Advanced implementations incorporate zero-trust network architectures, hardware-based encryption, and air-gapped operational modes to maintain data sovereignty and operational security in environments where adversaries may have physical proximity or sophisticated cyber capabilities.
The strategic imperative driving adoption of these systems stems from the growing recognition that modern military, diplomatic, and crisis response operations depend critically on real-time data processing, secure communications, and edge computing capabilities that cannot rely on distant cloud infrastructure or vulnerable satellite links. Traditional approaches—either depending on remote data centers connected via potentially compromised networks or attempting to build permanent facilities in unstable regions—introduce unacceptable latency, security risks, or resource commitments. Forward-deployed modular systems solve these challenges by bringing compute capacity directly to the operational edge, enabling secure processing of intelligence data, coordination of distributed forces, management of autonomous systems, and support for coalition operations without exposing sensitive information to transit across potentially hostile network infrastructure. For humanitarian operations, these systems provide the computational backbone for coordinating relief efforts, managing refugee databases, and supporting medical facilities in regions where local infrastructure has been damaged or is nonexistent. The modularity also addresses the challenge of matching compute capacity to mission requirements, allowing organizations to scale resources up or down as situations evolve without abandoning significant capital investments.
Early deployments have focused primarily on military applications, with defense organizations establishing these systems at forward operating bases, aboard naval vessels, and in support of expeditionary forces operating in regions with limited infrastructure. Recent developments indicate expanding interest from civilian agencies responsible for disaster response, with pilot programs exploring deployment to regions affected by natural disasters where local computing infrastructure has been compromised. The technology aligns with broader trends toward edge computing, data sovereignty requirements, and the recognition that geopolitical tensions increasingly extend into the cyber domain, making the physical location and security of computing infrastructure a strategic consideration rather than merely a technical one. As great power competition intensifies and the number of contested or fragile regions grows, the ability to rapidly establish secure, sovereign computing capacity in forward locations represents a critical capability for maintaining operational effectiveness and information superiority in environments where traditional infrastructure assumptions no longer hold.
Related Organizations
Cloud computing giant offering Amazon Braket.
Manufacturer of rugged servers, switches, and embedded computers for military and industrial applications.
Through Copilot and the 'Recall' feature in Windows, Microsoft is integrating persistent memory and agentic capabilities directly into the operating system.
Global specialist in energy management and automation that integrates cybersecurity into its industrial hardware and software.
Designs and manufactures USA-made ruggedized high-performance computing solutions for defense.
Designs and builds prefabricated modular data centers for rapid deployment.
Offers the PowerEdge XR series of rugged servers and modular data center partnerships.
A technology company specializing in directed-energy weapons, unmanned systems, and satellite communications.
Manufactures micro data centers designed for edge environments (mining, remote areas).