Data Security & Privacy Compliance
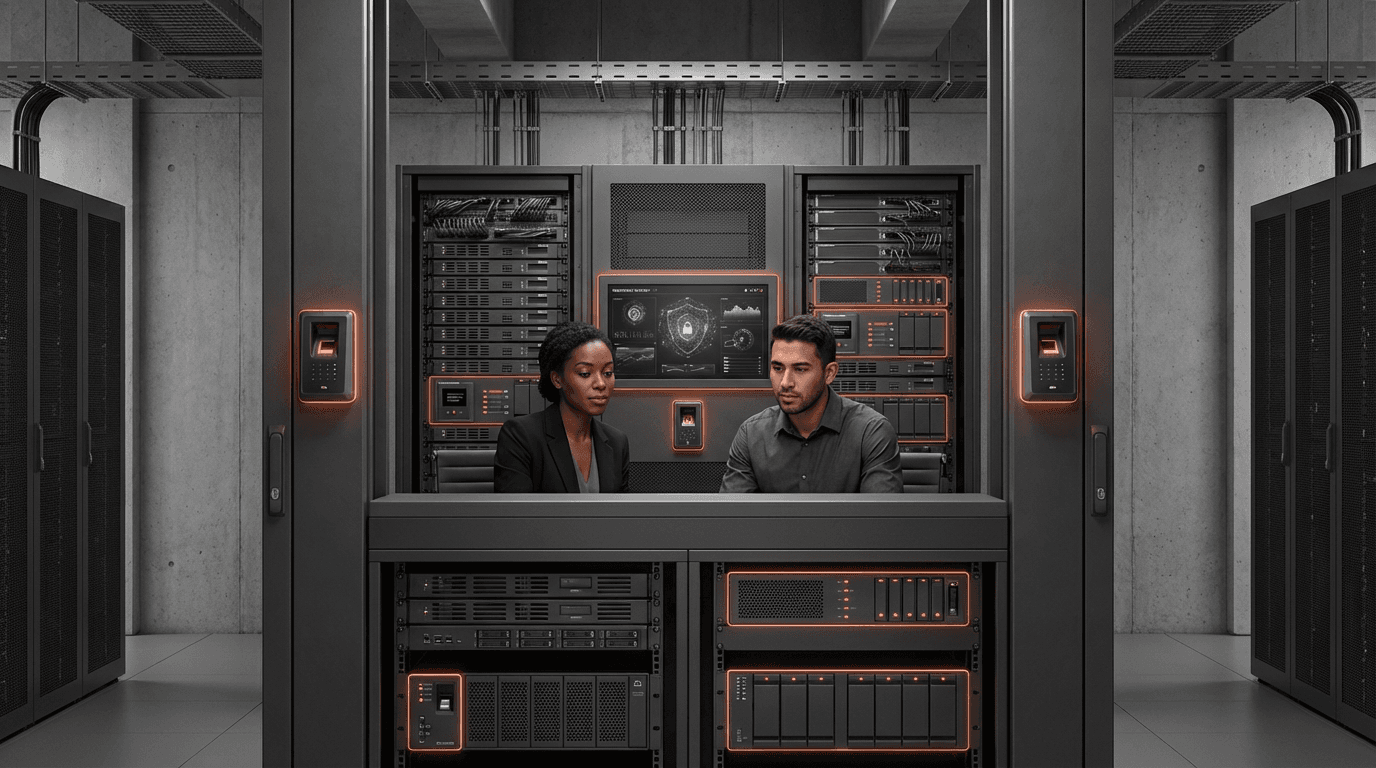
Data security and privacy compliance represents a comprehensive framework of technical controls, organizational policies, and regulatory adherence mechanisms designed to protect sensitive information from unauthorized access, breaches, and misuse. This multifaceted approach encompasses encryption technologies, access management systems, data governance protocols, and continuous monitoring capabilities that work in concert to safeguard digital assets. The technical foundation relies on layered security architectures that combine perimeter defenses, endpoint protection, network segmentation, and behavioral analytics to detect and prevent intrusions. Privacy compliance mechanisms extend beyond pure security measures to include data minimization practices, consent management systems, and automated processes for handling data subject rights requests. These systems must operate across increasingly complex digital ecosystems, spanning cloud environments, edge computing infrastructure, and legacy on-premises systems, while maintaining consistent protection standards and audit trails.
The escalating sophistication of cyber-attacks, coupled with the proliferation of stringent data protection regulations worldwide, has elevated data security and privacy from a technical concern to a strategic business imperative. Organizations face a dual challenge: defending against professionalized threat actors who employ advanced persistent threats, ransomware, and social engineering tactics, while simultaneously navigating a complex regulatory landscape that includes frameworks like GDPR, CCPA, HIPAA, and sector-specific requirements. The financial consequences of non-compliance or breaches extend beyond immediate remediation costs to include substantial regulatory fines, litigation expenses, and long-term reputational damage that can erode customer trust and market position. This pressure is particularly acute in sectors handling highly sensitive information, where a single breach can compromise millions of records and expose organizations to years of regulatory scrutiny. The public sector's heightened focus reflects not only compliance obligations but also the critical nature of citizen data and national security considerations, where breaches can undermine public trust in government institutions and democratic processes.
Current implementations vary significantly across industries and geographies, with leading organizations adopting zero-trust architectures, automated compliance monitoring, and privacy-by-design principles embedded throughout their technology stacks. The public sector increasingly deploys data sovereignty solutions that ensure citizen information remains within national boundaries and under domestic legal jurisdiction, particularly in regions with strong regulatory frameworks. Financial services institutions have pioneered real-time fraud detection systems and advanced authentication mechanisms that balance security requirements with user experience, while healthcare organizations implement specialized controls to protect patient data across increasingly interconnected care delivery networks. The convergence of artificial intelligence and security operations enables more sophisticated threat detection and automated response capabilities, though it also introduces new privacy considerations around the use of personal data in security analytics. As regulatory requirements continue to evolve and cyber threats grow more sophisticated, organizations are shifting from reactive compliance approaches to proactive security postures that integrate privacy considerations into every stage of data lifecycle management, positioning data security and privacy compliance as an ongoing strategic capability rather than a one-time implementation effort.
Related Organizations
The market-defining platform for privacy management and trust.
Data intelligence platform for privacy, security, and governance.
The largest global information privacy community and resource.
Offers a unified DataControls Cloud for data security, privacy, governance, and compliance.
Offers 'Data Marketplace' as part of its governance suite, allowing users to shop for trusted data assets internally.
Provides secure data access control for analytics and AI, ensuring only authorized users/models access sensitive data.

Drata
United States · Company
Automation platform for security and compliance (SOC 2, ISO 27001, HIPAA).
Automates security monitoring and compliance for various standards.