Confidential Computing for Analytics
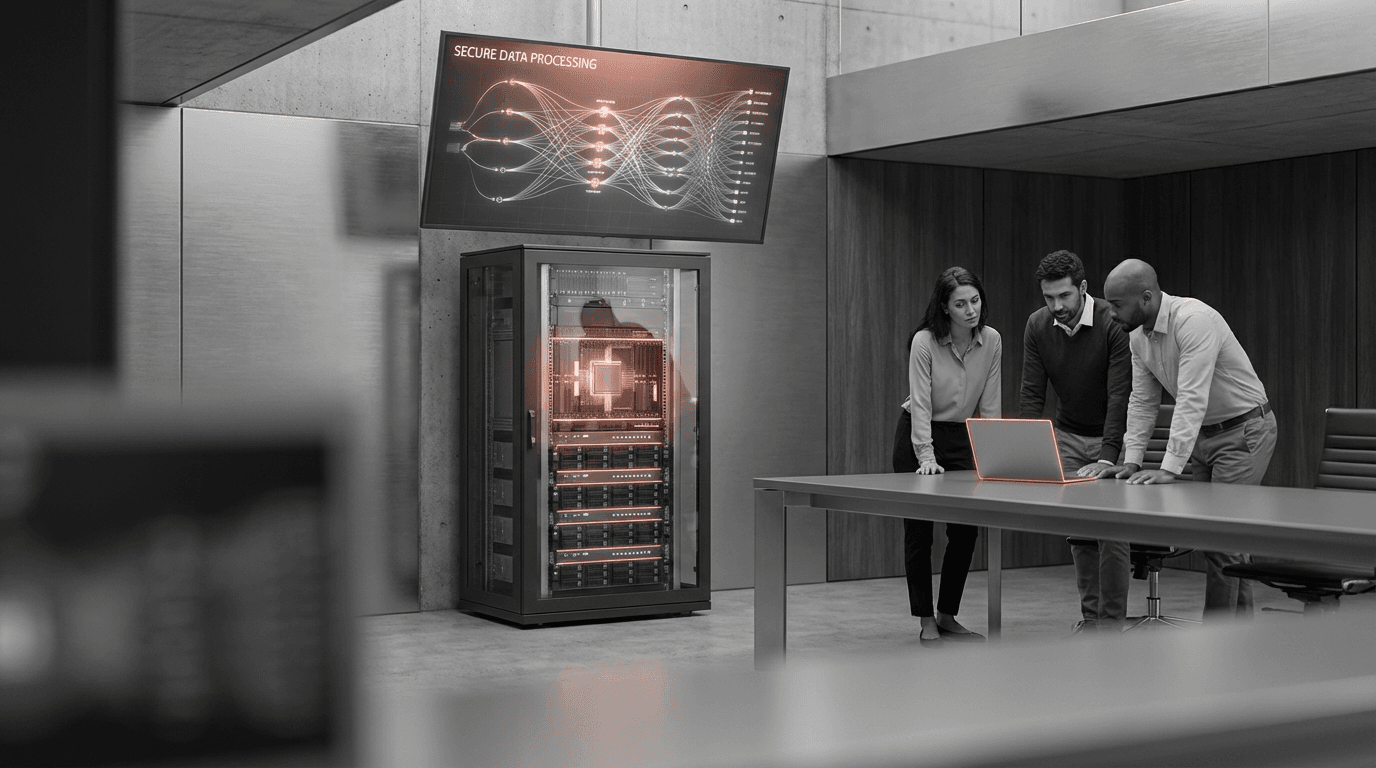
Confidential computing uses hardware-based trusted execution environments to protect data and code during processing, addressing the "data in use" security gap. Organizations are adopting confidential computing to enable analytics on sensitive data while maintaining strong security guarantees. The technology allows multiple parties to collaborate on analytics without exposing raw data, even to cloud providers or system administrators.
Applications include secure multi-party analytics, privacy-preserving machine learning, and analytics on encrypted data. Financial institutions use confidential computing for fraud detection across banks, healthcare organizations for collaborative research, and government agencies for sensitive data analysis. The technology is particularly valuable for analytics that require processing sensitive data in untrusted environments like public clouds.
At the Disruptive Innovation to Incremental Innovation stage, confidential computing is emerging globally, with cloud providers offering confidential computing services and organizations piloting use cases. The technology is advancing with better hardware support, tooling, and integration with analytics platforms. Challenges include performance overhead, complexity, and ensuring that security guarantees are maintained in practice.
Related Organizations
A project community at the Linux Foundation dedicated to defining and accelerating the adoption of confidential computing.
Develops silicon spin qubits using advanced 300mm wafer manufacturing processes.
A startup spun out of UC Berkeley's RISELab, providing a platform for collaborative analytics and AI on encrypted data.
Provides data clean rooms powered by confidential computing to enable secure data collaboration and model training.
Develops the RDNA architecture with Ray Accelerators, powering ray tracing on PC and current-gen consoles (PS5, Xbox Series X).
Provides a data security platform that decouples security from infrastructure using confidential computing enclaves.
Through Copilot and the 'Recall' feature in Windows, Microsoft is integrating persistent memory and agentic capabilities directly into the operating system.
Developing foundation models for robotics (Project GR00T) and vision-language models like VILA.
Software that enables applications to run in secure enclaves (AWS Nitro, Azure, etc.) without code modifications.
European deep tech startup providing a platform for encryption-in-use based on FHE and MPC.
German cybersecurity company building open-source software for confidential computing (e.g., Constellation).